Mastering Identity with Azure Active Directory – Episode 1: Introductions all round
In this series, I will take you through the key aspects of Azure Active Directory, and you will discover how using Azure AD you can build identity solutions for the future. The series is about the technology rather than the marketing hype. It is also a shameless plug for my identity masterclass which goes into all the deep technical details.
Hello, John Craddock here!
 I am a Microsoft MVP and have been working with Active Directory since the pre-release of Windows 2000. I had the privilege of presenting sessions on Active Directory at the Geneva and US launch events for Windows 2000. Since then I have consulted on all aspects of Active Directory and worked with AD FS since its first release. And of course as soon as Azure shone from behind the clouds I started work on Azure AD. I am also a network nut and have worked with many aspects of remote access including Microsoft DirectAccess and IPv6. If you take a look at Channel 9, you will find over 35 videos of my various sessions from around the world. @john_craddock www.xtseminars.co.uk
I am a Microsoft MVP and have been working with Active Directory since the pre-release of Windows 2000. I had the privilege of presenting sessions on Active Directory at the Geneva and US launch events for Windows 2000. Since then I have consulted on all aspects of Active Directory and worked with AD FS since its first release. And of course as soon as Azure shone from behind the clouds I started work on Azure AD. I am also a network nut and have worked with many aspects of remote access including Microsoft DirectAccess and IPv6. If you take a look at Channel 9, you will find over 35 videos of my various sessions from around the world. @john_craddock www.xtseminars.co.uk
So why do I appear before you on this page? I’ve just reread that last sentence, and it sounds like I am appearing before a judge and jury, maybe I am!
Well, Your Honour, it’s like this. I have been asked for some years if I would write a hands-on masterclass on identity. Knowing how much work was involved, I have written many courses in the past, I have politely declined. At the beginning of this year (2016), I was asked again by the wonderful Norwegians who run the Norwegian Infrastructure Conference (NIC). Being from the UK and remembering what the Vikings did to us, how could I refuse?
This series follows the pedagogical progression of my hands-on masterclass, although not to the same level of depth, and each episode includes a short video. I have tried to keep each episode succinct and provide you with a quick insight into an aspect of Azure AD and its associated technologies. If you want to build your skills, the master class has 30+ hands-on labs to consolidate your learning. Warning: the masterclass is a deep-dive into the technologies and goes into the real technical detail.
As they become available you can find the episodes here:
- 1: Introductions all round
- 2: It’s all about protocols
- 3: Creating and managing an Azure Active Directory
- 4: Synchronising Azure and on-premises AD
- 5: Working with SaaS applications
- 6: Managing your applications
- 7: The Azure AD Application Proxy
- 8: Integrating with on-premises AD and AD FS
- 9: Creating a B2C directory
- 10: Enabling partners with B2B invitations
Let’s get started!
Episode 1: Introduction to Azure Active Directory
I am sure you are all familiar with on-premises AD, which can be deployed as a highly available and performant store for user and computer identities. The AD allows users and computers to authenticate against resources in the same forest or other forests via trusts. In addition to its role as an identity store, it has the added benefits such as group policies. Notice in the first sentence I said “can be deployed as a highly available and performant store,” your organisation is responsible for designing and implementing the system so that you have the right number of domains, domain controller, site definition, site link and so on. In addition to maintaining the infrastructure, your administrators are responsible for the directory data: users, computers, groups and other objects.
A limitation of the on-premises AD is that the primary authentication protocol, which is Kerberos, only supports authentication to resources in the same or a trusting forest. Kerberos authentication is restricted to resources accessible within your corporate network. In today’s world where we need to stretch out and embrace cloud services, Kerberos fails us.
So what is Azure AD? It is a highly available and performant store for user and computer identities, sound familiar? However, here the benefit - Microsoft is entirely responsible for managing the infrastructure, with its high scalability and availability. Today it supports over 1.3 billion authentications per day, 9 million directories, 600 million user accounts, and provides a 99.9% SLA. Your organisation is responsible for the data (user, groups, device and applications) in your Azure AD. Your directory is referred to as an Azure AD tenant, you will have to choose a tenant name, which is unique, and you will be assigned an initial domain name of tenantname.onmicrosoft.com. Once you have got started you can add your domain names into you tenant; we will look at this in a later episode of this series of blogs.
Azure AD gives us an identity store in the cloud which we can populate with users. You may be thinking AND? The “and” is Azure AD supports all the major industry standard authentication protocols, SAML-P, WSFederation, OpenID Connect and OAuth 2.0. To be picky, OAuth 2.0 is not an authentication protocol, but I’ll discuss that in the next episode. As a result of the comprehensive protocol support, a user can authenticate against Azure AD and then have Single-Sign-On (SSO) to a plethora other services. Those services may be running on on-premises servers, in a partner cloud or a public cloud. Using Azure AD, our users can reach out to the best of breed cloud services. See Figure 1:
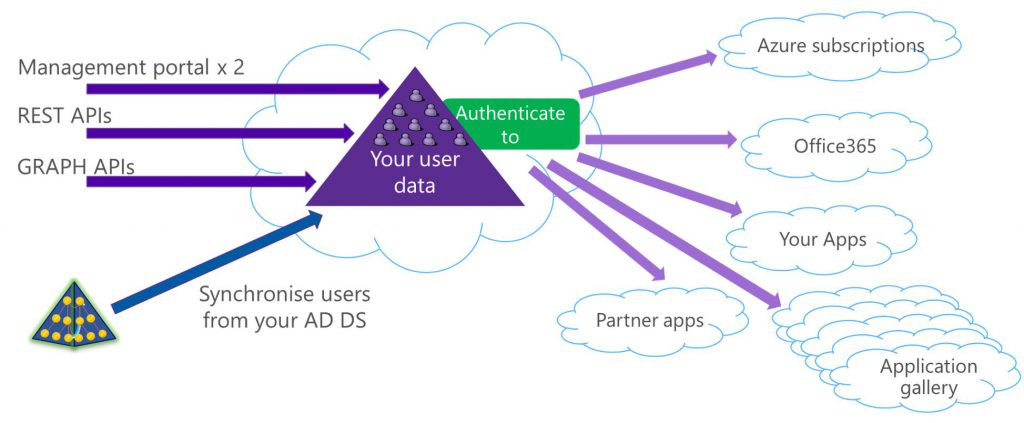
Figure 1: The Azure AD
Azure AD is not just an identity store; it is a feature rich identity service. Services include:
- Self-service password resets
- Self-service group and application management
- Multi-Factor Authentication (MFA)
- Conditional access
- Detailed reporting and auditing
The Azure AD comes in Free, Basic, and Premium (P1 & P2) editions; the available features vary between each flavour. If you already have O365, then you are already an Azure AD tenant and have your directory. Here’s a great table to compare the features.
How do we get our user into the Azure AD directory? If you look back at figure 1, you will see that there are two management portals, APIs to make programmatic changes either through you own applications or via PowerShell and the ability to synchronisation users from you on-premises AD.
The reason that there are two portals is that Microsoft is moving all Azure management to a new HTML 5 portal. The move is a progressing work, with the Azure AD management only being switched on for public preview in September 2016. At the moment not all Azure AD operations can be performed through the new portal. You will need to switch back to the classic portal to manage some features.
That’s it until next time. Please watch the video for a quick tour of management portals:
For details of all the episodes in this series look here. To learn and become skilled in implementing identity systems based on Azure AD, on-premises AD and AD FS, join me at one of my Masterclasses. I hope to see you there!