Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Windows IT Pro Blog
URL
Copy
Options
Author
invalid author
Searching
# of articles
Labels
Clear
Clear selected
Analytics
Announcement
App Compat
Application Management
app validation
Capabilities
Chris Jackson-The App Compat Guy
Deployment
Device management
Features
functionality
General
Hardware
Licensing
Memory utilization
Microsoft Connected Cache
Microsoft Edge
MSIX
Onboarding
Partners
Performance
Portal experience
regression
Security
Security updates
Servicing and updates
Test Base for Microsoft 365
testing
Tips and Tricks
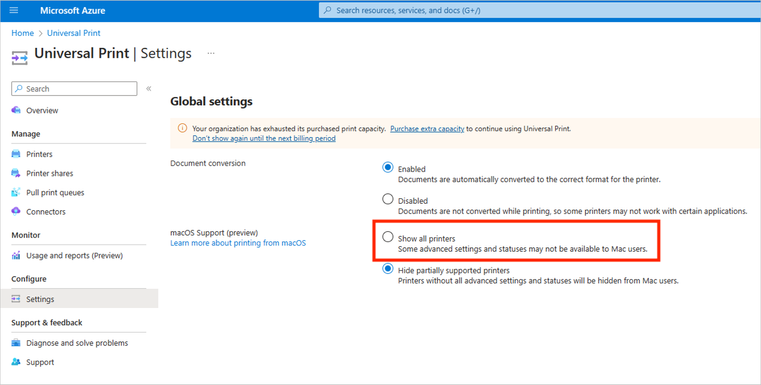
Universal Print
Update Staging Lab
USL
Virtualization
Windows
Windows 10
Windows 11
Windows 365
Windows Autopatch
Windows Autopilot
Windows Server
Windows Virtual Desktop
Options
- Mark all as New
- Mark all as Read
- Pin this item to the top
- Subscribe
- Bookmark
- Subscribe to RSS Feed

























Latest Comments