Unable to Access HTTPS Sites behind TMG 2010
Introduction
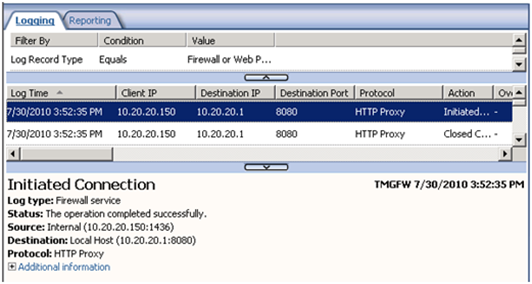
It could be just another case where we grab some data, look at it and resolve the issue, but it was a long road until we get to the bottom of this. The scenario was quiet simple: clients that were behind TMG couldn’t access HTTPS sites. All other sites using HTTP were working just fine and the most phantasmagoric thing that we noticed was that on TMG Logging we just have entries for 8080, no HTTPS request at all as show below:
On the client, the only thing that was showing up was:
Troubleshooting
All the usual suspects during a standard troubleshooting phase were eliminated (HTTPS Inspection, Malware Inspection, NIS, URL Filtering, HTTP Filter, Network, etc), it was time to thing: what else is left? What about the client? Let’s take a netmon on the client and see what’s going, right? Yep…let’s do it. For my surprise, after starting netmon and repro the issue, we did not even saw the HTTPS Request leaving the workstation; we just saw requests on port 8080 and then the clients sent a FIN:
Digging Deeper
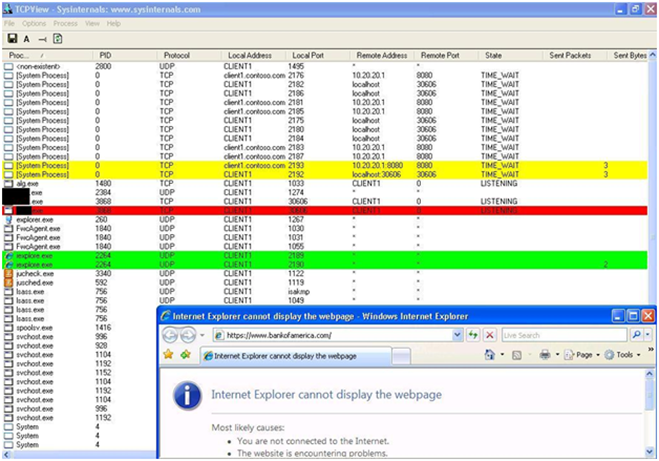
In order to investigate further what was going on I used the tool TCPView, which gives more details information about network connectivity and process that are using for a specific connection. So I tried to access the Bank of America site (which uses HTTPS by default) and here it is the result:
Notice two things:
- Before hit ENTER there was no line highlighted.
- After hit ENTER on IE was possible to see the activity, which was:
- While iexplorer.exe is being in use as main process (green one), other processes were also called during this operation: system process (yellow) and XXXX.exe (red).
Note1: I’m not saying the driver name because this behavior was observed in many others third party AV filter drivers.
Ok, now we have some footprints that we can use to investigate further. The process XXX.exe belongs to a third party antivirus. As a temporary test we disabled the AV solution using MSConfig and restarted the workstation. It didn’t help since there were some other kernel drivers loaded in the system. As a temporary measure we uninstalled the AV, tested and worked. At that point we handled over the issue to the AV Vendor.
Note2: Only disable AV solution on the workstation for troubleshooting purpose, validate your tests and enabled it back. It is strongly recommended to have antvirus solution on your system and address potential issues with the AV vendor.
Just another reminder that not even everything that you think is caused by TMG, it actually is….this is just another example of TMG (as it was on ISA) be a victim of another problem.