Enhancing NAT with TMG
I recently worked in a very interesting case where customer’s Exchange Server got in the SPAM Block list although the environment was clear of malware and no SPAM was originated from that server at all. We ended up identifying why the server got blocked and it was because an external servers was using reverse DNS lookup to verify if the MX record for that email server matches with the source IP address from where the SMTP traffic was coming from. To make it easier to understand, let’s take a look on following diagram for contoso.com network:

Notice that the primary IP bound to ISA’s external interface is using IP 192.168.1.113. The SMTP Publishing rule correctly maps the internal Exchange Server IP but the outbound traffic always will leave with the primary IP of the ISA Server. This means that when the external Exchange Server performs the reverse lookup for the MX record (for example: mail.contoso.com) it will resolve for 192.168.1.60 which doesn’t match with the source IP received in the IP header of the SMTP packet.
The fast resolution here is to change the primary IP to be 192.168.1.60, but sometimes this cannot be done so fast due other policies for example. But….that’s the way it is on ISA Server, not much you can do other than plan to use the primary IP for scenarios like this.
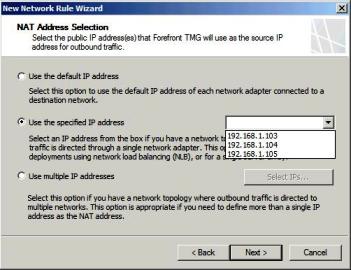
The good thing here is: TMG resolves this problem! How? With a feature called Enhanced NAT (ENAT). Now you can create a network rule to specify which IP address you want to use for outbound traffic as shown below:
Isn’t that nice? It’s amazing for sure!!
Well, we are already in September and TMG is coming very soon…but while is not RTM yet, you still have a chance to download Beta 3 and play with it.