Operating a PKI: CA Certificate Renewals and OCSP
There are some effects that CA Certificate Renewal has on OCSP. OCSP provides revocation checking information for clients. For, each CA an OCSP Responder has a Revocation Configuration. Each Revocation Configuration has an OCSP Signing Certificate associated with it. The private key of the OCSP Signing Certificate is used to sign OCSP Responses so that clients can verify the authenticity of those responses.
As explained in the following article: https://technet.microsoft.com/en-us/library/cc754774.aspx
Online Certificate Status Protocol (OCSP) Response Signing certificates need to be signed by the same certification authority (CA) key that was used to sign the end-entity certificates that they provide status for.
After a CA key is renewed, the CA will be using the new key to sign newly issued certificates. In the period between the time a CA certificate is renewed and the expiration date of the original CA certificate, the CA cannot issue or renew OCSP Response Signing certificates, which may prevent an Online Responder from signing OCSP responses.
The Solution
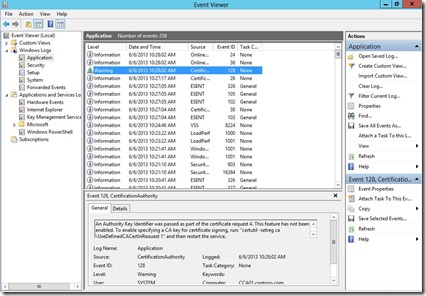
The solution to this issue is to configure the CA to issue certificates based on information about the issuer in the request. In other words the OCSP Responder normally sends information about the issuer in the request so that the CA can sign the new OCSP Response Signing certificate with the same key pair it was previously signed by. So, we just need to configure the CA to honor these requests. In fact if you have an OCSP Responder setup in your environment, you may have noticed this event in the Application Log:
In order to enable this feature you need to run the following command on the CA and then restart the CA Service: “certutil -setreg ca\UseDefinedCACertInRequest 1”
So, once you run this command your existing Revocation Configuration will be able to properly renew it’s OCSP Signing Certificate, even after the Issuing CA Certificate is renewed. However, if you do need to renew your CA Certificate with a new key pair you do need to setup a new Revocation Configuration to support that new key. Instructions for configuring a Revocation Configuration are available here: https://blogs.technet.com/b/askds/archive/2009/06/29/implementing-an-ocsp-responder-part-iii-configuring-ocsp-for-use-with-enterprise-cas.aspx.
To summarize you will need to perform the following actions to enable your OCSP to support a Issuing CA whose certificate has been renewed with the new key pair:
- Run the following command on your CA: “certutil -setreg ca\UseDefinedCACertInRequest 1”
- Restart the CA Service
- Setup a new Revocation Configuration after your CA Certificate is renewed
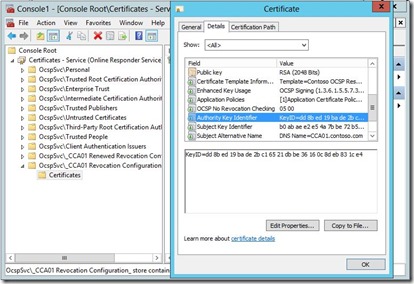
To illustrate the end result, we can view the original Issuing CA Certificate:
Notice that the Subject Key Identifier matches the Authority Key Identifier in my original OCSP Signing Certificate:
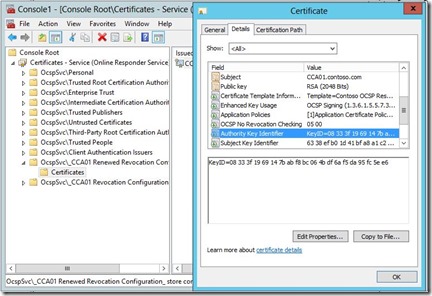
Here is my renewed CA Certificate:
Once I renewed my CA Certificate, configured my CA as mentioned earlier, and configured a new Revocation Configuration you can see that the Subject Key Identifier in the new CA Certificate matches the Authority Key Identifier field in OCSP Signing Certificate for the new Revocation Configuration:
Summary
This is my third blog article relating to CA Certificate Renewal. Hopefully, these articles have given you the information you need to understand CA Certificate Lifecycles, the impact of renewing a CA Certificate, and how to successfully renew your CA Certificates with minimal impact to your environment.
Here are links to the previous two articles:
Operating a Windows PKI: Certification Authority Certificate Lifecycle and Renewals
Operating a Windows PKI: Renewing CA Certificates
-Chris