Installing a Two Tier PKI Hierarchy in Windows Server 2012: Part VII, Enabling SSL on the Web Enrollment Website
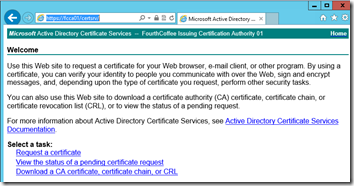
In this installment of this blog series, I will cover enabling SSL on the Web Enrollment website. If you are new to Active Directory Certificate Services this blog will also give you an idea of what’s involved in issuing certificates.
Duplicating the Web Server Certificate Template
A best practice is to duplicate Certificate Templates instead of using the Out-of-box templates. This allows you to retain the original templates, without modification. So, the first step for me to perform is to duplicate the Web Server Certificate Template. In order to do this I open up the Certificate Templates Console. Then I right-click on the Web Server template and select Duplicate Template from the context menu.
In Windows Server 2012 you will first be presented with the Compatibility tab. The idea is that you select the OS Version of your Certification Authority and the OS Version of clients that will be enrolling for certificates based on this template. This will then only allow you to select options in the Certificate Template that are supported by both the CA and the client/enrollee. In my example, I am going to leave the defaults.
Next I am going to name the Certificate Template FourthCoffee Web Server.
Next, I have to give the CA the proper permissions for the template, so that it can enroll for a certificate. On the Security tab, click on Add…
I then ensure that Computers is selected under Object Types…, type the CA name, click Check Names, and then click OK.
Finally, I click OK.
Enabling the Certificate Template on the CA
So, now the CA has proper permission to the Certificate Template. Next, I have to make the Certificate Template available on the CA. So, I open up the Certification Authority Console (certsrv.msc). I then right-click on Certificate Templates, select New, then Certificate Template to Issue.
Then I select FourthCoffee Web Server, and click OK.
Enrolling for the Certificate
I could enroll for the Certificate through IIS. However, I prefer to use the Certificates MMC as that gives me more control over the configuration of my request. So, I type MMC.exe and press Enter. Then on the MMC Console, I select File then Add/Remove Snap-in…
From the Add or Remove Snap-ins selection tool, I select Certificates, and click Add.
I then select Computer account, and click Next.
Then on the Select Computer page of the wizard, I select Local Computer, and click Finish
I then click OK to complete this task.
Next, I expand Certificates (Local Computer), right click on Personal, select All Tasks, and then Request New Certificate…
Now, the Certificate Enrollment wizard opens, and I click Next.
On the Certificate Enrollment page of the wizard, I click Next.
On the Request Certificate page of the Wizard, I select the Check Box to choose FourthCoffee Web Server. I then, click on Details, and then the Properties button.
Under Alternative Name, on the Subject Tab, I change the Type to DNS.
Next I type the short name of the CAs machine name, under Value, and click Add. I then perform the same step for the FQDN of the CAs machine name. I click Apply, and then click on the General tab.
I type SSL Cert under friendly name. I will later use this name to identify the appropriate certificate. Then I click OK.
Next on the Request Certificates page of the wizard, I click Enroll.
After I successfully enroll for the certificate, I click Finish.
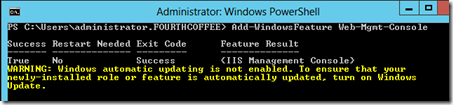
Installing IIS Administration Console
At this point I realized that did not have the IIS Administration tools installed (Oops!). To install the IIS Administration tools I ran the following PowerShell command: Add-WindowsFeature Web-Mgmt-Console.
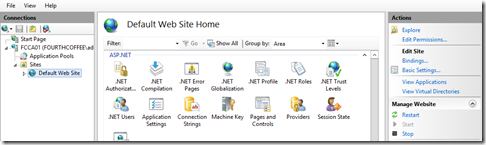
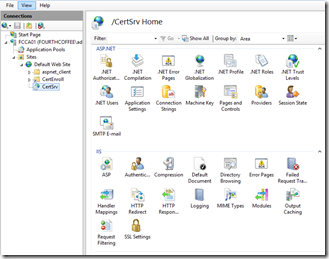
Configuring IIS
Now that I have the IIS Administration Console installed, I open the console. I expand the Server Name node, then expand the Sites node and click on Default Web Site. In the Actions pane I click on Bindings…
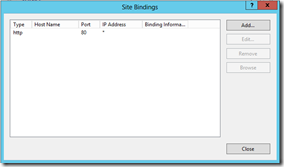
In the Site Bindings windows, I click Add…
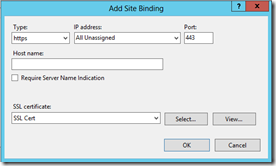
In the Add Site Binding window, I select https from the Type drop-down. Then under SSL certificate I chose SSL Cert, and finally click OK. Then I click Close to close the Site Bindings window.
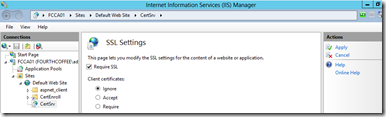
I then expand the Default Web Site, and click on the CertSrv virtual directory. Next, I double-click on SSL Settings.
Under SSL Settings, I select Require SSL, then I click the Apply link in the Actions pane.
Now the Web Enrollment site is configured with SSL.
Conclusion
I have now configured SSL on the Web Enrollment website. The next step for me to take is to perform some security configuration on both CAs to reduce the attack surface, and secure my shiny new PKI.
![image_thumb[29] image_thumb[29]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/8540.image_thumb29_thumb_14D08EC7.png)
![image_thumb[31] image_thumb[31]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/0272.image_thumb31_thumb_36D8EA8D.png)
![image_thumb[33] image_thumb[33]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/3288.image_thumb33_thumb_102A5E40.png)
![image_thumb[35] image_thumb[35]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/1581.image_thumb35_thumb_1217AD49.png)
![image_thumb[37] image_thumb[37]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/2526.image_thumb37_thumb_3734F7B5.png)
![image_thumb[39] image_thumb[39]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/0830.image_thumb39_thumb_63054BA4.png)
![image_thumb[41] image_thumb[41]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/4431.image_thumb41_thumb_1992F6E9.png)
![image_thumb[42] image_thumb[42]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/7140.image_thumb42_thumb_45634AD8.png)
![image_thumb[43] image_thumb[43]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/6825.image_thumb43_thumb_7BF0F61C.png)
![image_thumb[44] image_thumb[44]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/5126.image_thumb44_thumb_79D3F753.png)
![image_thumb[45] image_thumb[45]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/6747.image_thumb45_thumb_10B2C8D0.png)
![image_thumb[46] image_thumb[46]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/6562.image_thumb46_thumb_0E299712.png)
![image_thumb[47] image_thumb[47]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/3324.image_thumb47_thumb_6AACF2AC.png)
![image_thumb[48] image_thumb[48]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/0045.image_thumb48_thumb_07D29AB7.png)
![image_thumb[49] image_thumb[49]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/7041.image_thumb49_thumb_659A8F30.png)
![image_thumb[50] image_thumb[50]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/4111.image_thumb50_thumb_7802DFE5.png)
![image_thumb[51] image_thumb[51]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/0434.image_thumb51_thumb_1A776EA1.png)
![image_thumb[53] image_thumb[53]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/2870.image_thumb53_thumb_262CB5D3.png)
![image_thumb[54] image_thumb[54]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/4863.image_thumb54_thumb_768E9746.png)
![image_thumb[55] image_thumb[55]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/4403.image_thumb55_thumb_70D37DA0.png)
![image_thumb[56] image_thumb[56]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/89/67/metablogapi/1134.image_thumb56_thumb_5311F2E1.png)