Static vs. Dynamic Gateways in Azure
|
Rob Waggoner |
I often talk about Site-to-Site VPNs in Azure, and every time I do, I talk about the routers that need to be on-premises to connect to the Azure Virtual Network. We put together the Azure in 5 minute series so if this isn’t making sense, please check out our Azure in 5 minutes series here. You will want to check out the Hybrid Cloud Setup section and then come back to this discussion.
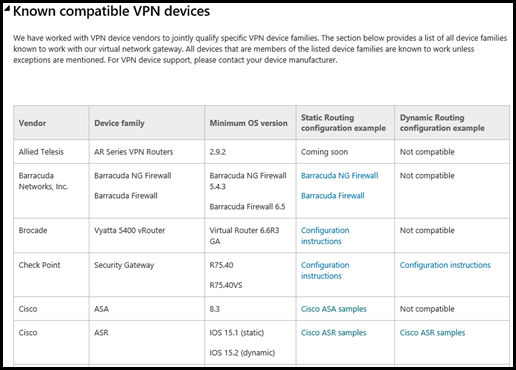
Now that we are on the same page, there are a number of devices we’ve identified as Known compatible VPN devices that work with Azure; we maintain a list of these devices here. Below is a screen shot of the top part of this list. Take note of the 5 columns in the chart, the two right most columns define the “Static Routing” or “Dynamic Routing” for each of the devices listed.
As you can see from my screen shot, some devices only support Static Routing, while other devices can support Static or Dynamic Routing. While I do not have a “favorite” router (aside from RRAS), I am very partial to the Dynamic Routing devices and I’ll cover the reasons “why” below in the section Why does this matter if I only need one S2S VPN connection? …
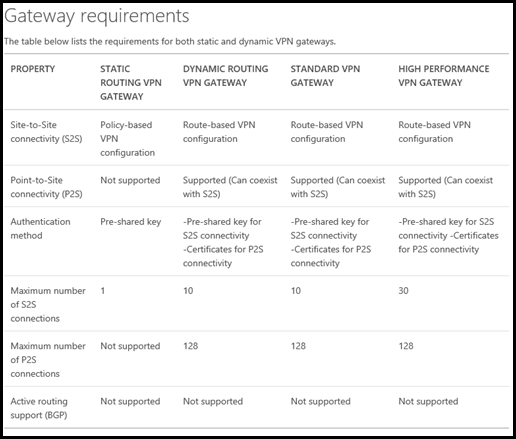
Azure uses the terms “Static Routing Gateways” & “Dynamic Routing Gateways”, the industry also refers to these as “Policy-based VPNs” (Static) & “Route-based VPNs” (Dynamic). So what’s the difference between Static and Dynamic Routing? This article talks about the details, but I will repeat them here because these details are very important. Here is a screen shot of the Gateway requirements, look in the second column (STATIC ROUTING VPN GATEWAY) and third column (DYNAMIC ROUTING VPN GATEWAY):
The reason I encourage my partners to leverage a DYNAMIC ROUTING VPN GATEWAY device whenever possible is because of the extensibility it offers. With a STATIC ROUTING VPN GATEWAY device, you can only have one Site-to-Site (S2S) VPN connection and Zero Point-to-Site (P2S) VPN connections. A DYNAMIC ROUTING VPN GATEWAY device will give you up to 30 S2S VPN connections and 128 P2S VPN connections. As a refresher, a S2S VPN connects two networks together, like your on-premises network connecting to the Azure Virtual Network. A P2S connection connects a Client Device, say a Windows 10 workstation, to the Azure Virtual Network.
Why does this matter if I only need one S2S VPN connection?
If you use a STATIC ROUTING VPN GATEWAY, you only have one S2S VPN connection, but that’s all you need, right? What if your router loses the connection to the Azure Virtual Network, say your Internet Connection drops or a router fails? You cannot connect anything else to your Azure Virtual network without reconfiguring the Azure Virtual Network. This takes time and introduces change into your network for what is hopefully a temporary outage.
If you have a DYNAMIC ROUTING VPN GATEWAY device and it loses its connection to the Azure Virtual Network. Again, if your Internet Connection goes down, you could send everyone to a different network (home or public WiFi) and they could connect via P2S connections back to the Azure Virtual network. This allows everyone to continue working without any changes to the Azure Virtual Network (assuming you’ve already configured the P2S certificates) and once the S2S is back up, everything is back to normal.
STATIC ROUTING VPN GATEWAY devices have their place, but the reality is that the Industry is moving towards “Route Based VPNs” (Dynamic) because they are more secure and more flexible.
Until next time,
Rob
Technorati Tags: Rob Waggoner,Azure,Static,Dynamic,Gateway,Azure Virtual Network