Don’t trust a fake Microsoft Security Essentials (MSE), Get the Real Thing!
 |
CRN has the following article talking about rogue software that is impersonating itself as Microsoft Security Essentials.
A rogue version of Microsoft (NSDQ:MSFT)'s free antimalware product, Microsoft Security Essentials, is making its way around the Internet by scaring users into buying a bogus security product.
Rogue Antivirus Scareware Exploits Microsoft's MSE
Scareware is a type of malware that tricks users into purchasing a fake security software program by claiming, often falsely, that their computer is infected with viruses, Trojans or other threats. The malware often promotes a bogus product as a way to eliminate the threat.
I’m talking to you about this because we’ve update the licensing of Microsoft Security Essentials to cover Small Business as well as Home use. Check out the full licensing change here:
https://www.microsoft.com/security_essentials/eula.aspx#mainNav
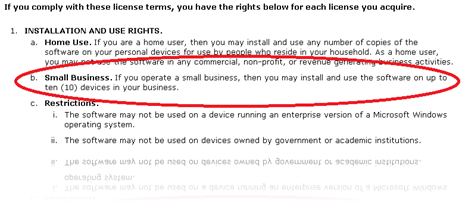 |
Please review the full licensing agreement for additional details. |
If you are deploying MSE, please make sure that you download it directly from Microsoft. You can download the authentic Microsoft Security Essentials from here:
https://www.microsoft.com/security_essentials/default.aspx
Or here:
https://www.microsoft.com/security/products/mse.aspx
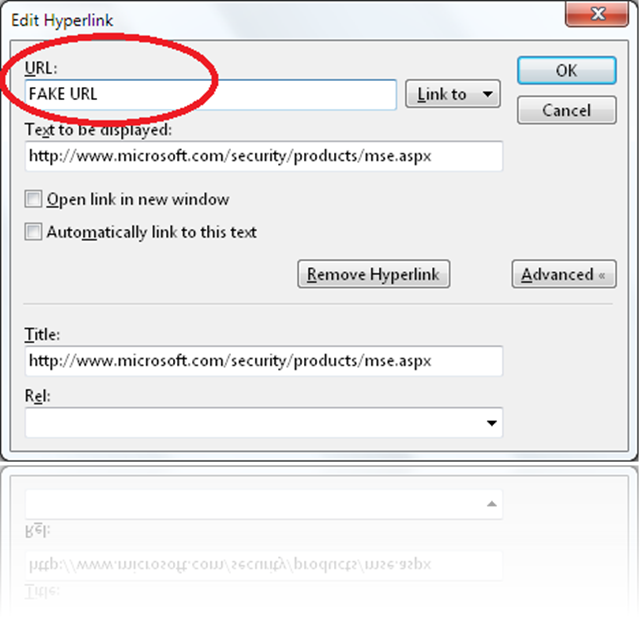
Notice that both URLs are located at Microsoft.com. Personally, I try to not trust embedded URLs. Just because it looks like URLs are “safe” URLs, there’s no guarantee that the URLs are actually what they say they are.
Even in Live Writer, I can present the URLs above, but actually direct you someplace else. Check out this example:
While I confirm my URLs, I think you get the point. Please don’t trust anyone’s links, confirm them first. If you want to access MSE without clicking on a URL, you are welcome to type microsoft.com/security_essentials in your browsers’ address bar and it will take you to the MSE landing page. You can download MSE from there.
Please make sure that you protect the machines you manage. I’m looking forward to the release of Windows Intune, it will give you one more great tool. Until Windows Intune ships, please take a look at Microsoft Security Essentials.
Until next time,
Rob
Technorati Tags: Microsoft Security Essentials,MSE,Rogue MSE
del.icio.us Tags: Microsoft Security Essentials,MSE,Rogue MSE