Mail-enabling Guest Users or "How I made everyone show up in the Address Book"
So, today, I received an email from one of my esteemed colleagues asking how we could get B2B Azure AD tenant guests to show up in the Office 365 GAL. I thought, "Yeah, that should be something that's possible. I mean, they have email addresses."
In a rare turn of events, it actually is as easy as un-hiding them from the GAL.

Yes. Yes it is.
So, to illustrate this, we'll create a couple of users as Azure B2B guests and then make them visible.
So, the first step is to log into Azure AD PowerShell (you could do the portal, but clicking is so 2017) and create an invitation to a guest user. The syntax is pretty simple:
New-AzureADMSInvitation -InvitedUserDisplayName "Aaron Guilmette" -InvitedUserEmailAddress myemailaddress@domain.com -SendInvitationMessage $true -InvitedUserType Guest -InviteRedirectUrl "https://www.bing.com"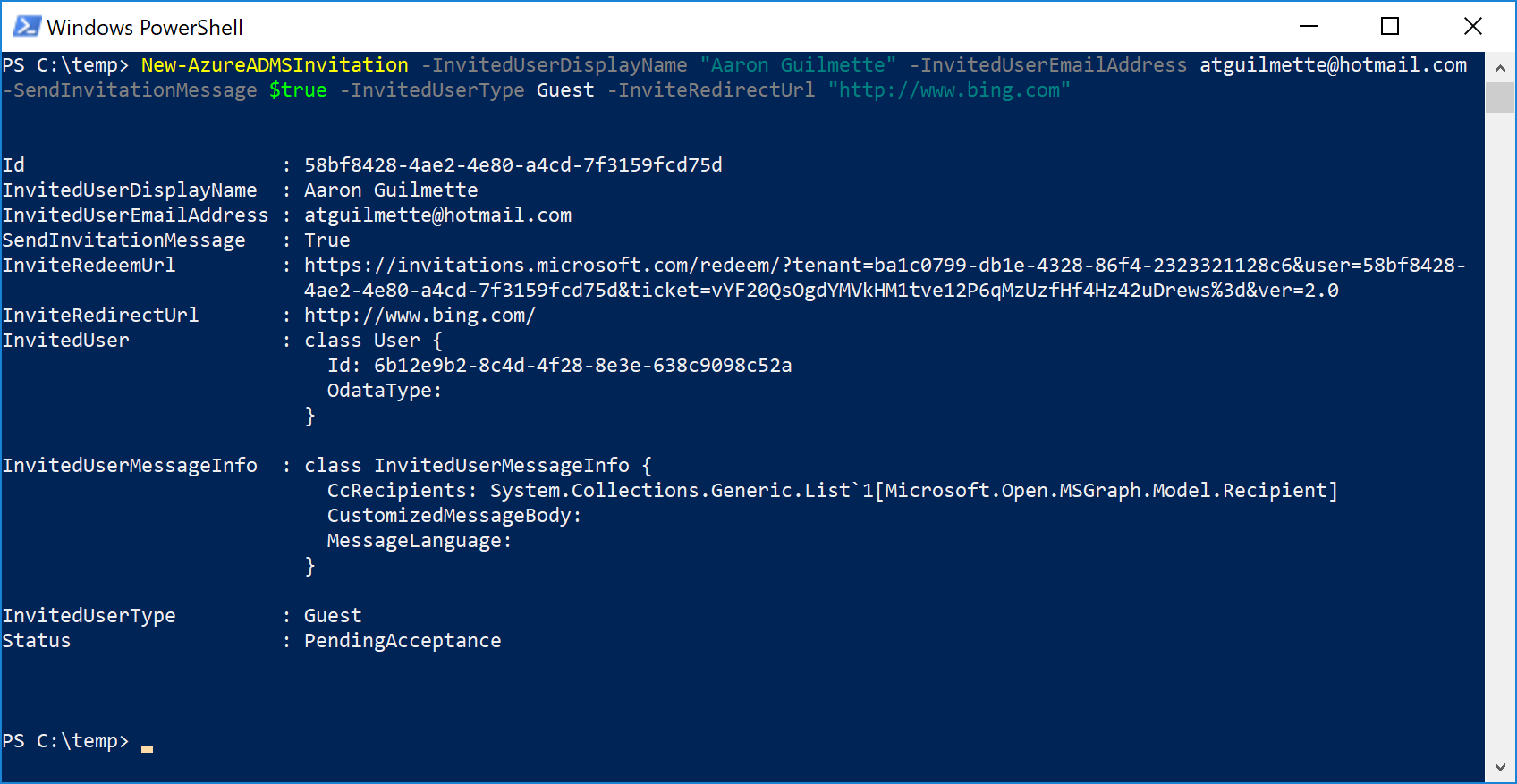
You don't have to approve or accept the invitation; the user ID is created (as you can see above.)
Go ahead and look for the user account. You can use either the Get-MsolUser cmdlet or the Get-AzureADUser cmdlet. They'll both return similar information. Since we're already connected with the Azure AD cmdlets, I'll just keep using those.
Get-AzureADUser -SearchString myemailaddress@domain.com
One of the neat things to notice is how the UPN is formatted. The @ sign is replaced with an underscore, and then #EXT#<tenantname> is appended. We're going to use later on in one of our enablement scenarios.
For our next trick, we're going to connect to the Exchange Online PS endpoint and and take a look at our users. Do it in the same session, because we're going to need both the Azure AD cmdlets as well the Exchange cmdlets.
$EXO = New-PSSession -ConfigurationName Microsoft.Exchange -ConnectingUri https://outlook.office365.com/powershell-liveid -Authentication Basic -AllowRedirection -Credential (Get-Credential)Once you're connected, we're going to use the Get-User cmdlet. This Exchange cmdlet is used for identifying available directory users, just like it is in on-premises Exchange. We're going to search for a specific recipient type: in this case, GuestMailUser:
Get-User -RecipientTypeDetails GuestMailUser
The "GuestMailUser" recipient type tells us that the user is indeed mail-enabled (since it has an email-address). The last thing to do is really just to un-hide it from the Address Book.
To do this, you can simply pipe the previous command into Set-MailUser:
Get-User -RecipientTypeDetails GuestMailUser | Set-MailUser -HiddenFromAddressListsEnabled $false
As you can see, I've already done it before for some others users in my tenant.
But, now we can confirm with my newly updated user:
Get-MailUser myemailddress@domain.com | FL *hidden*
Now, to go check my tenant's GAL.
Log into Office 365, select the People app, select Directory, and...HOLY POPULATED GAL, BATMAN!

[ takes a bow ]
And, for the bonus round: mail-enable members of a security group
I'll just drop a few handy snippets here. Let's say you've created a group and have a workflow that puts your external users in a security or distribution group in order to grant them access to an application or a SharePoint site, and you want to programmatically enable just those users.
There's a script for that:
$GroupObjectId = (Get-AzureADGroup -SearchString 'sgSiteAccess').ObjectID.ToString()
Get-AzureADGroupMember -ObjectId $GroupObjectID | % { Set-MailUser $_.Mail -HiddenFromAddressListsEnabled $false }
And, the extra credit assignment: mail-enable all Azure AD guests that are part of a group without touching the Exchange Online mailboxes (since Set-MailUser would generate errors on them) and suppress the warning message that no properties that were updated:
$GroupObjectId = (Get-AzureADGroup -SearchString 'sgSiteAccess').ObjectID.ToString()
$GroupMembers = Get-AzureADGroupMember -ObjectId $GroupObjectID | ? { $_.UserPrincipalName -match "\#EXT\#" }
$GroupMembers | % { Set-MailUser $_.Mail -HiddenFromAddressListsEnabled $false -wa SilentlyContinue }
The sky kinda is the limit.