Your 2017 guide to Azure Security Center

As ransomware attacks become more sophisticated, cloud based applications are at an increased risk. Professionals using Microsoft Azure must now take full advantage of the recently introduced Security Center to defend their cloud infrastructure and applications.
 By Alex Bennett, Firebrand Training
By Alex Bennett, Firebrand Training
With support for Windows Server 2016 recently announced and a host of new updates planned for 2017, organisations will be missing out if they fail to make the most of Azure Security Center.
What is Azure Security Center?
Azure Security Center reached general availability in mid-2016 and is used by organisations to detect threats targeting their Virtual Machines (VMs) or applications in the Azure cloud.
This service provides more than just a basic security overview for your Azure cloud estate. Microsoft utilises an expansive set of telemetry -- powered by its global cloud presence -- to discover new attack patterns and trends.
By tapping into the collective power of millions of cloud customers, Security Center dynamically updates its threat detection capabilities. So, as attackers release new and increasingly sophisticated exploits, Security Center stays up-to-date.
It also accesses information gathered using the Azure Monitoring Agent and Security Monitoring extension. This data is then analysed to produce a set of business-tailored recommendations for your environment.
The service monitors the following resources:
- VMs
- Cloud Services
- Azure virtual networks (vnets)
- Azure SQL service
- Partner solutions integrated with Azure
How to get started quickly with Azure Security Center
Setup is fast, painless, and low-commitment. To trial the service and get full access immediately, professionals can sign up for a 30-day free trial. Alternatively, dive straight in with a subscription to Security Center.
For professionals who can’t invest in the service there’s also a free tier that provides a basic overview of security for your Azure apps.
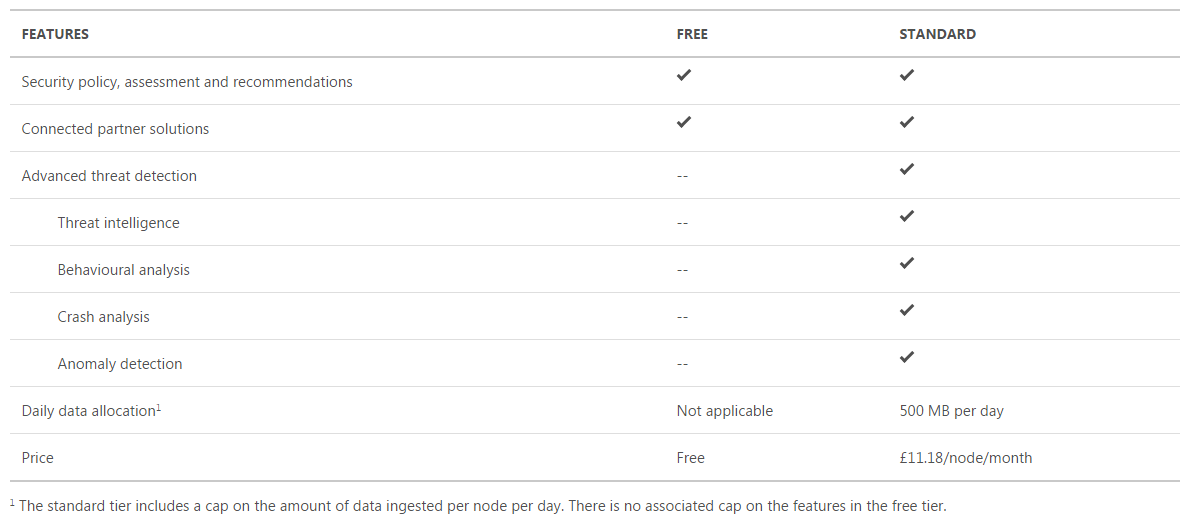
Comparison of features between Free and Standard versions
The Security Center can be accessed from your Azure portal. If this is your first time launching the service, you’ll need to agree to Microsoft collecting meta data and error reports from your virtual machines. These are used to identify vulnerabilities in your Azure services.
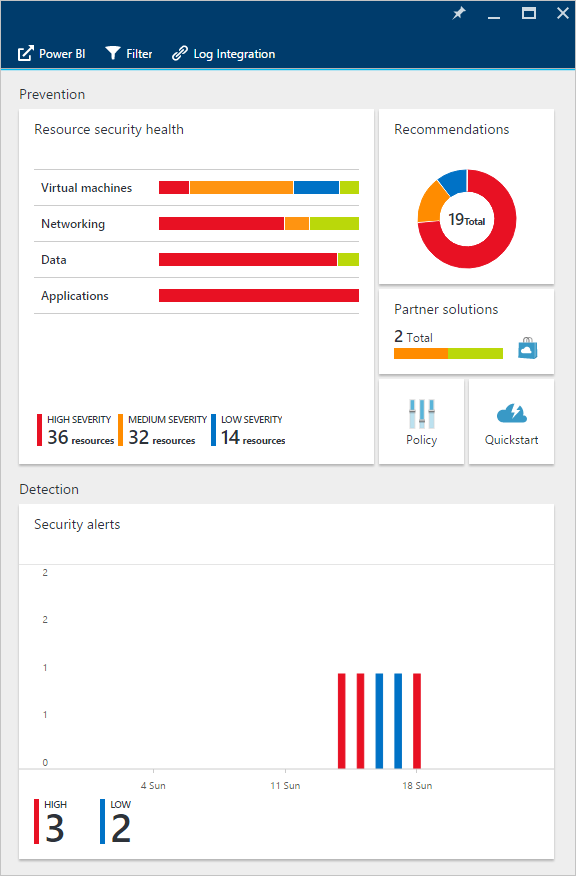
Security Center dashboard
To set up your standard tier free trial, follow these steps:
- Log in to the Azure management portal using a tenant administrator account
- In the Azure Management Portal window, click Security Center in the list of options
- In the Overview panel, click the Policy tile
- In the Security policy panel, click the subscription that you’d like to upgrade
- Click Pricing tier
- In the Choose your pricing tier panel, select ‘Standard – Free Trial’ and click ‘Select’
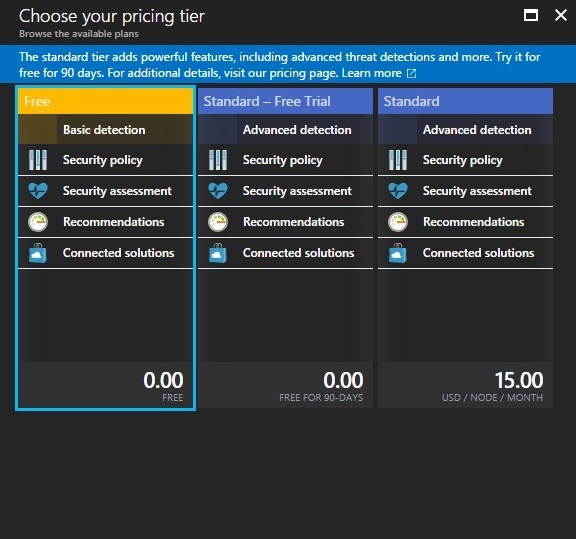
Available pricing tiers (will differ per region)
You’ll now have access to your Security Centre dashboard. You can also explore your security data using Power BI dashboards – enabling you to visualise, analyse and filter recommendations from anywhere, including your mobile device.
There are two Power BI dashboards available – security insights and policy management. Find out how to mesh your Security Center data with Power BI here.
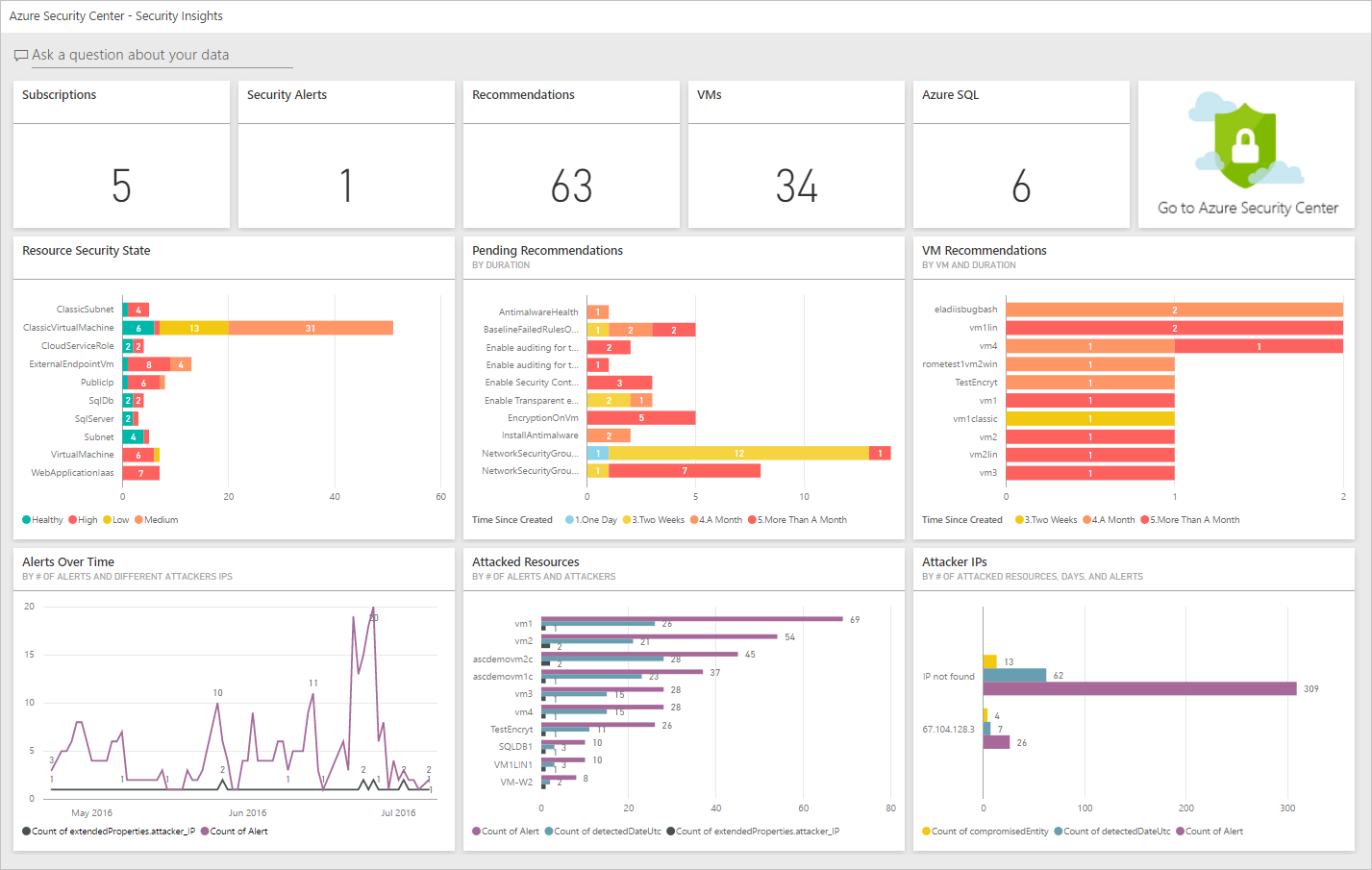
Security Center integrating with Power BI
But before you sink your teeth into Azure, it’s important to understand the data security and privacy considerations associated with Azure Security Center data collection. To provide you with visibility on your security, this service analyses data from a number of sources:
- Azure services
- Virtual machines
- Partner solutions
- Network traffic
For more information on Azure Security Center data security, including Microsoft’s privacy statement, take a look at this documentation.
Setting up security policies
Get started securing your Azure cloud by setting up security policies. In a nutshell, security policies define a set of areas which the service looks at to provide recommendations and alerts. This helps you to focus on what’s important, and lessens the focus on irrelevant information.
Start implementing security policies for your Azure subscriptions and resource groups. Take a look at this Microsoft guide for a more detailed look at setting up security policies.
Planning for your organisation
To take full advantage of Security Center, it’s important to understand how different individuals or teams in your organisation use the service to meet development, monitoring, operations, governance and incident response needs.
Multiple users and teams can use Security Center through Role-Based Access Control (RBAC). This provides built-in roles that can be assigned to users, groups, and services in Azure.
Microsoft recommend that you assign the least permissive role needed for users to complete their tasks. By controlling admin privileges in this way you’ll help reduce any potential damage if that user account is compromised by an attacker.
Learn how to optimise your use of Security Center based on your organisation requirements and user roles take a look at this planning and operations guide.
Recommendations and Alerts
The policies you enable in Azure Security Center define the security recommendations you receive. When security vulnerabilities are identified, you’ll be provided with guidance on how to configure your security in response.
Learn how to monitor your recommendations here. Or for specific recommendations, take a look at these pages:
- Application recommendations
- Network recommendations
- SQL service recommendations
- Virtual Machine recommendations
Security Center also automatically collects, analyses, and integrates log data from your Azure resources, network, and connected partner solutions (like firewall and endpoint protection solutions) to detect potential threats.
A list of prioritised security alerts is shown in Security Center along with the information you need to quickly investigate the problem and remediate in the event of an attack. More information on how to respond to security alerts can be found here.
Don’t forget to turn on handy Security Center email alerts. You’ll only be notified of high severity alerts, so you’re inbox isn’t going to be spammed. Find out how to enable your alerts with this quick email alerts guide from Microsoft Program Manager Thomas Shinder.
Security Center might seem simple on the surface but ‘the key to appreciating Azure Security Center is understanding the common problems it solves for you’ says Thomas Shinder, Microsoft Program Manager.
There are a number of security quick-wins you can use Security Center to fix. Professionals can quickly use Azure security Center to highlight a lack of anti-malware or unpatched virtual machines – a potential issue if you have thousands of them.
Thomas has composed a list of quick ways you can start securing your Azure cloud in 2017. Take a look at the article and start securing Azure now.
What’s new in Security Center for 2017?
Microsoft continues to push out updates for Security Center and Azure customers using the service will only benefit.
Security Center has access to masses of data about cloud network activity which is used to detect threats targeting your organisation. For example, Microsoft is using machine learning to monitor historical remote access attempts, allowing it to detect brute force attacks against SSH, RDP and SQL ports.
Microsoft states that these capabilities will soon be expanded to monitor other applications and protocols, like FTP, Telnet, MongoDB and Elastic Search.
Azure Security Center can now automatically discover and recommend a whitelisting policy for a group of machines and apply these settings to your VMs via the AppLocker feature. This is a great addition for admins who are spending too much time managing and maintaining whitelists.
Microsoft have also introduced Just-In-Time (JIT) Network access to VMs. Cyber criminals commonly target open network ports with brute force attacks to get access to your VMs. With JIT on Azure, these ports are only opened for a limited time when needed to connect remotely to the VM, massively reducing your attack surface.
New behavioural analytics were also introduced recently. To find out more about recent Azure enhancements read take a look at this post from Microsoft.
More Security Center enhancements to come in 2017
There are more Azure enhancement coming in 2017. In spring, Microsoft says it will fully power up the Azure SQL Database Threat Detection service.
The tech, in preview mode for the past year, monitors suspicious database activity and integrates its alerts with Azure Security Center. The SQL Database Threat Detection service will monitor and profile your application behaviour to identify suspicious database activities.
The service uses machine learning algorithms written in R, which is now supported by SQL Server 2016 running on Azure's back-end.
If malicious attempts to breach or exploit sensitive data are spotted, designated administrators get immediate notifications and will be able to view the alerts in the Azure Security Center, along with recommendations for how to mitigate the threats.
What next?
For an early preview of Azure updates, join the Azure Advisors community and Azure Security Center Advisors group.
Plus, for developers using Azure, it’s never been easier to study Azure with a recent Microsoft Azure training initiative from Microsoft. For more detail on that, take a look at this blog post.
2017 is set to be a huge year for Azure. Whether you’re planning on migrating or are already running critical infrastructure in the cloud – learning how to make the most of Azure Security Center is a no-brainer.
---
Alex works for Firebrand Training, a Microsoft Gold Learning Partner. He has worked in the IT training and certification industry for the past 3 years. He writes regularly about Windows Server, Microsoft Azure and IT security.