SharePoint Permissions Management: Why it really matters
By Edmund White, Field Product Manager, AvePoint
The “insider threat" is the most damaging obstacle that an IT department faces when it comes to securing company content. Edward Snowden vaulted this notion into public consciousness back in 2013, and statistics show that insiders leaking confidential information or gaining access to content that they are not supposed to causes much concern for the IT organization.
According to the healthcare-focused results of the 2015 Vormetric Insider Threat Report (ITR), 92 percent of healthcare IT admins fear insider threats, 49 percent felt very or extremely vulnerable, while 62 percent identified privileged users – who have access to all resources available from systems they manage – as the most dangerous type of insider. 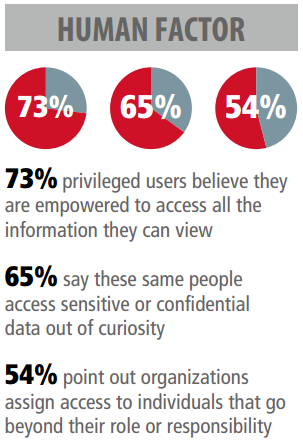
Similarly, according to the 2014 Microsoft Vulnerabilities Report, 97 percent of all critical security vulnerabilities could have been mitigated by removing admin rights. In 2013, admin rights – including the ability to install, modify and delete software and files, as well as the right to adjust system settings – were used to exploit 95 percent of Microsoft Office flaws. Normally, however, these rights are not granted to the majority of employees with the reason being that user accounts with such admin privileges are particularly vulnerable to exploitation and breach.
What can we do to avoid the insider threat and keep our information secure? A typical IT response might be to implement stricter, more intrusive controls on security and access. However, I propose that this is not an issue of control, but an issue of business user productivity.
SharePoint is especially susceptible to users breaking inheritance and granting full control permissions to non-technical users. In many customer SharePoint environments, over-granting of permission occurs. To make matters worse, IT often lacks the visibility to discover and control these users.
Why is this the case? We discovered through interviews with business users that when it comes to collaboration on SharePoint, their primary concern is to get the job done fast and without considering security implications. When asked why they granted full control, users were either unaware of the correct permissions level to grant or wanted to make the job easier for the recipient. While this approach may seem reasonable from their perspective, it makes the job harder for IT admins.
The problem is less about control, but more about providing an easy, appropriate way to grant access that the user understands. A solution would have to promote both productivity and ease of use, while automatically ensuring that no security holes are introduced into the environment.
Finding Third Party Solutions
The good news is that there are ways to ease these concerns. With the right software, organisations can lighten their business users' workload and keep environments in compliance through automation.
In order to function productively, automation must be able to provide both guidance and oversight. To determine if a system is appropriate, key questions to ask include:
- Can the solution provide a process that is easier to use than native SharePoint?
- Can we use language that our users understand instead of technical jargon?
- Can the solution give us advanced features such as approvals, auditability, and life-cycle management?
The overarching purpose of automation is to achieve the best result for both administrators and users, either through a simple self-service request process, or automated life-cycle and disposition actions. The administrators know that changes in SharePoint are executed correctly, and the users have an easy to understand path to get their requests quickly.
Classification is Key
Automating the classification of content is another important step towards user productivity. Though the benefits of content types and proper classification of search, workflow, and retention policies are generally understood, the implementation often puts a large burden on the end user to fill in these forms. Automating classification saves time for the end user and removes the potential for human error or apathy. When users do not fully understand the long-term value of classification, filling out forms can be seen as a short-term hindrance to getting work done.
Once the content is classified, automating the security policy of the site should be considered. If a sensitive document was mistakenly uploaded to a public site, automation could recognize this as an incident and begin an appropriate remediation process. Through this feature, automated classification of content becomes the basis for protection of that content and can prevent any mishaps from occurring on SharePoint.
With all security considerations, a primary concern should be the ease of use, level of intrusiveness, and impact on productivity for the business user. Through boosting the productivity of the business users and reducing risk in the SharePoint environment, automation provides a secure solution.
Resources
Have you experienced issues with admin privileges? Let us know in the comments section or via @TechNetUK
