Tip of the Day: An easy way to measure computer reboot and logon times
Today's Tip...
Process Monitor has evolved over the years from several different tools, into a single, "must have" tool for a wide variety of troubleshooting scenarios. One of the great capabilities of Process Monitor is its ability to capture a computer trace from very early in the computer startup process. The information collected from this startup trace can be used to determine how long the computer takes to get to various states, such as:
- Logon screen
- Credentials entered by user
- Start Explorer.exe (shell)
- Desktop "ready to use"
I know of at least one other toolkit that performs this; Windows Performance Toolkit (WPT). WPT is also a "must have" set of tools for tracing a reboot scenario, and many other facets of Windows performance. The only condition of WPT that lead me to use Process Monitor, is that Process Monitor has a powerful filtering capability that allows a reboot cycle trace to be as small as 8192 bytes (8 KB). For pure time measurements of reboot and logon timing, the only events that needs to be collected are "process start" events.
Process start events can be used as markers to indicate key events in the Windows startup process.
- Logonui.exe (logon dialog is presented to use)
- Userinit.exe (started after a user has entered credentials, is successfully authenticated, and subsequent processes are started for that user to set up their desktop)
- Explorer.exe (start shell)
- Process Monitor (the user runs Process Monitor to stop and save the trace, which also indicates the desktop is at or near a "ready to use" state)
Regarding the phrase "desktop ready to use", this is an arbitrary time in the logon process, where Windows has started the majority of services and processes, and has achieved a state where the user can begin opening and interacting with applications. At "desktop ready to use", the user should be able to open their e-mail client or their business tools and be able to use them without having unnecessary pauses or busy cursors. This is again an arbitrary state, to be determined by each customer in their environment. You might have for example a tool that starts up to assist with setting up a default printer. This could be a marker that the desktop is at or near "ready to use" for the IT consumer. In this case the user logon time is approximately the time difference between when the 'Userinit.exe' process starts, and the name of your printer assistance tool starts.
There is some consideration that might be given to the fact that a full reboot of the computer can be far more resource intensive than a simple logoff and logon. In many environments, a full computer restart may trigger security software to perform a new scan of files, memory, and processes, or Windows processes such as AppLocker might perform additional scanning only on a full computer restart, that it may not perform on a simple logoff and log back on. A full computer resource can skew a logon time after a full restart. To help offset that to some degree, the test may add a condition where the user does not logon when the logon dialog appears, but instead waits a minute or more to logon. The same markers listed above can be used to measure user logon time. By waiting a minute or two, Windows will have completed most if not all, of the starting of services and other automatic system processes that occur on a full computer restart.
Anyway, on to the procedures to capture startup and logon traces using Process Monitor.
Windows Reboot and Logon Analysis Tool
Sysinternals' Process Monitor
Process Monitor is an advanced monitoring tool for Windows that display and optionally records, real-time file system, Registry and process/thread activity. Process Monitor can run in real-time mode or can be configured to record a boot logging trace.
Process Monitor can be downloaded and copied to a computer being analyzed. There is no formal installation process for Sysinternals tools. If you run the Process Monitor tool interactively, the first time you will be presented the end-user license agreement (EULA). If you accept that, you will not be prompted again to accept the EULA, for that specific user profile. If your profile is deleted or reset, you may have to accept the EULA the next time you run Process Monitor.
If you pin the Process Monitor executable to your taskbar, then during trace capture you will not have to start Explorer or a command prompt to start Process Monitor, you can just click Process Monitor directly from your taskbar.
You can find the Sysinternals' Process Monitor tool using your favorite Internet search engine, and search for Process Monitor.
Recording a "Reboot Cycle"? trace, using the Sysinternals' Process Monitor
- Start Process Monitor (this may require elevation)
- The 'Process Monitor Filter' interface will be displayed. Click the 'Reset' button to reset filters to default values, and then click the 'Ok' button.
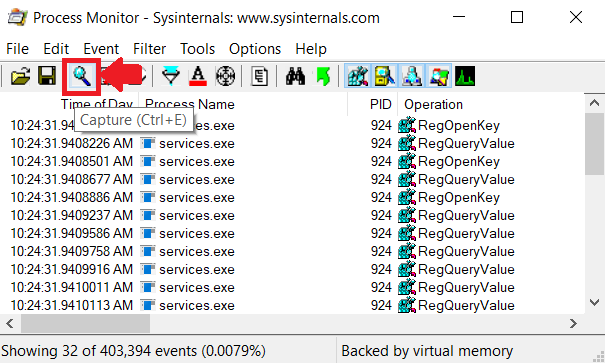
- Click the 'Capture' button to stop the current real-time trace, as depicted below:
- Before the boot logging is started, some filtering can be enabled that will reduce the captured trace to a very small size, and filter out events that are not needed to analyze reboot and logon.
- On the ProcMon icon bar, click to de-select the following categories of events:
- Network (name is "Show Network Events"?)
- Disk and File (name is "Show File System Activity"?)
- Registry (Show Registry Activity)
- Now, click 'Filter' from the ProcMon menu, and then click the menu item named 'Drop Filtered Event'.
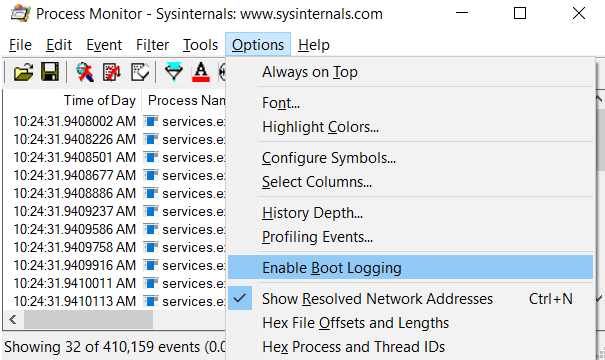
- In the Process Monitor menu, click 'Options', and then click 'Enable Boot Logging', which enables the Process Monitor boot logging, until the tracing is stopped.
- An option dialog will appear titled 'Enable Boot Logging', which offers an option to "generate thread profiling events"?. Don't click any option, just click the 'Ok' button to enable boot logging on the subsequent reboot.
- After clicking the "Ok" button, close Process Monitor and restart the computer.
Note: It is important to log on after the reboot, start Process Monitor, and then stop and save the trace, so that it does not use an excessive amount of disk space.
Analyzing a "Reboot Cycle"? trace, using the Sysinternals' Process Monitor
- After rebooting the device, logon to the device, and then start Sysinternals' Process Monitor.
- You may be prompted to reset the filter, which you can do, and then click OK.
- You will then be prompted to save the current trace. You can click 'Ok' and then choose the folder to save the trace to.
- Once the trace is saved, the boot trace will be available and displayed in Process Monitor.
- Click 'Tools' and then click 'Process Tree'.
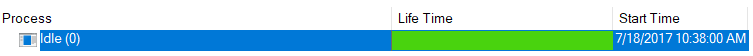
- Click the very first item in the far-left column, which should be the pseudo-process 'Idle', and note the clock time.
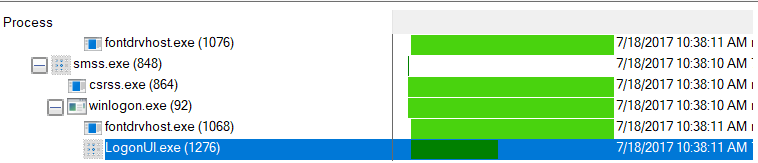
- Next, in the 'Process Tree' display, scroll down while looking in the far-left column for the item 'Logonui.exe'. When found, click 'Logonui.exe', and again note the clock time.
Note: the difference between 'Idle' clock time and 'Logonui.exe' is the time interval from computer startup to the logon credentials dialog box. In this case the difference is 11 seconds.
- At this point in computer startup, the user entered credentials and pressed ENTER. The next marker in the trace to look for is the process 'Userinit.exe'. 'Userinit.exe is the process that is launched if the user's credentials are verified, and initiates the subsequent chain of events leading to the user's shell starting, desktop starting, and the important marker "desktop ready to use"?.
Note: Desktop ready to use is going to be determined by each individual configuration. You are looking for a process starting, at approximately the same time that the computer is responsive enough to allow some other process to start and be used without excessive delay. For example, desktop ready to use could mean that the user is able to start Microsoft Office Word and begin working in Word without delays or excessive sluggishness from the operating system. The marker you are looking for may be the process name of your anti-virus software being started, or some shell item being started. A Windows 10 inbox example might be 'Windows Defender tray item'. The point being that the time that 'MSASCuiL.exe' (Windows Defender tray item) starts, may be approximately the same time that services and other items have started, and that the OS is responsive enough to user input to be declared 'ready to use'?. Therefore, this arbitrary marker is termed by me, 'desktop ready to use'?.
- The 'Userinit.exe' process should be relative close but under the previously noted process Logonui.exe. Note the clock time for starting of the 'Userinit.exe' process.
- A good indicator of "desktop ready to use"?, in this case, is the starting of the process 'Procmon.exe'. Recall that after logging on, we started 'Procmon.exe' in order to stop and save the boot trace. Note the clock time of starting 'Procmon.exe'.
- The difference in clock time between starting of 'Userinit.exe' and 'Procmon.exe' is roughly that particular user's overall logon time.
Note: A reboot/logon trace with default ProcMon filtering may be 3 GB or more. A reboot/logon trace recorded with the filtering options documented in this guide may be as small as 8192 bytes. An additional effect of this filtering is that much less memory and processor resources are needed, and thus the effect of trace capture has far less impact on the overall reboot/logon trace statistics, including clock time.
Reference: "An easy way to measure computer reboot and logon times" - https://blogs.technet.microsoft.com/robertsmith/2017/07/19/an-easy-way-to-measure-computer-reboot-and-logon-times/