(Cloud) Tip of the Day: Determine if a Windows 10 PC is DJ++, Azure AD Joined, or Workplace Joined
Today’s (Cloud) Tip…
Three scenarios exist in which a corporate user might use their Windows 10 PC to access company resources located in Azure: DJ++, Azure AD Joined, or Workplace join to Azure AD. This enables features such as SSO (single-sign-on) to Azure AD resources from anywhere.
DJ++ is the hybrid identity domain join feature which allows domain joined Windows 10 PCs to register as a device in Azure Active Directory when the group policy Computer Configuration/Policies/Administrative Templates/Windows Components/Device Registration/ Register domain joined computers as devices is configured and linked to the Organizational Unit containing the Windows 10 PCs.
Azure AD Join for Windows 10 PCs is where the user is using a managed account (the account originates and resides solely in Azure Active Directory) and the PC is joined to Azure Active Directory, typically during OOBE (Out of box experience.)
Workplace Join is where the PC is not in either Windows Server Active Directory or Azure Active Directory. The user logs on to their Windows 10 PC using a local account and goes to Settings -> Accounts -> Work access with a work or school account which resides in Azure Active Directory.
There are two ways to view and verify Trust Type for devices in Azure:
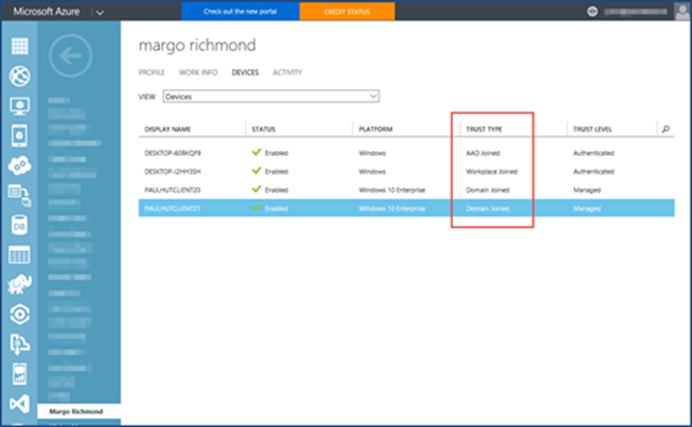
Using the Azure Management Portal…
We can verify whether a machine is registered and we will see the appropriate trust type under the user’s device tab stating Domain Joined, AAD Joined, or Workplace Joined.
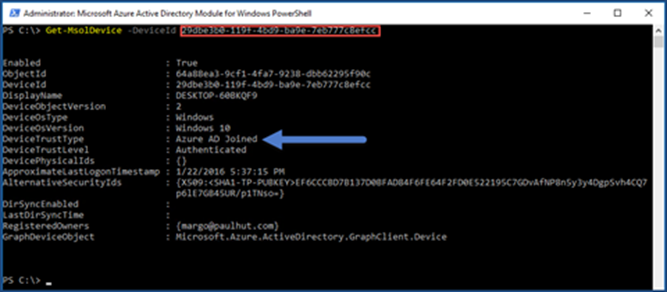
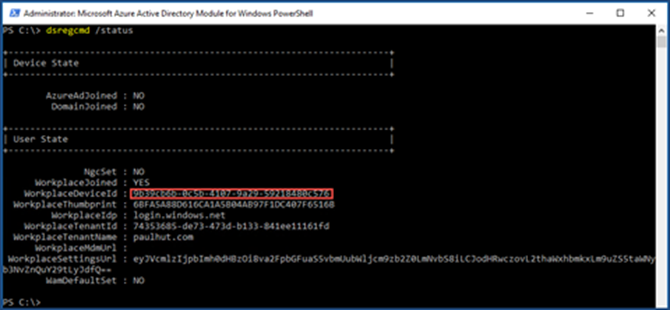
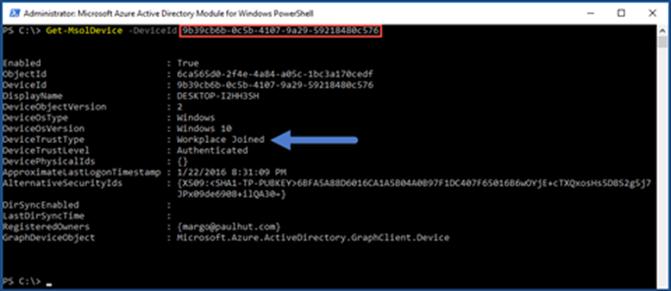
Using Azure AD PowerShell…
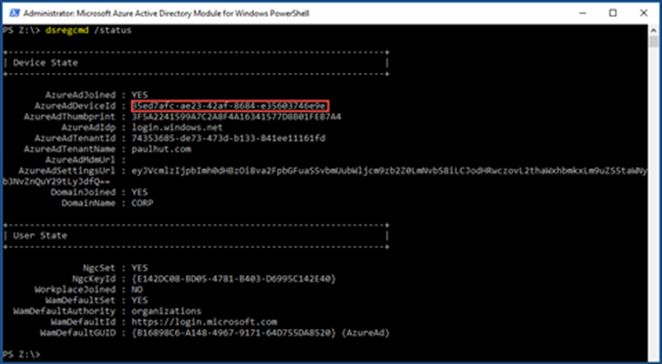
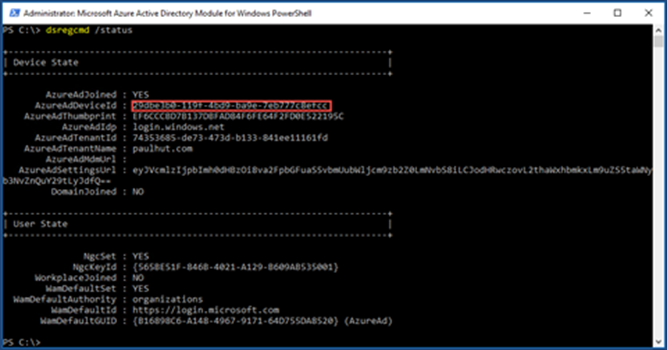
- On the workstation run dsregcmd.exe /status to obtain the AzureAdDeviceId or the WorkplaceDeviceId.
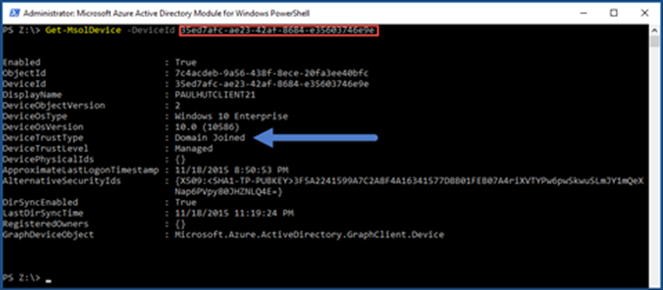
- Use AzureAdDeviceId or the WorkplaceDeviceId in conjunction with the Azure Active Directory Module for Windows PowerShell command Get-MsolDevice -DeviceId 35ed7afc-ae23-42af-8684-e35603746e9e.
DJ++ example:
Azure AD Joined example:
Workplace Join example: