Exchange 2010 – Pre-staging the Cluster Name Object (CNO) to support a Database Availability Group (DAG)
In Exchange 2010 when using the Database Availability Group (DAG) we leverage the cluster services in Windows 2008 and Windows 2008 R2.
When utilizing the cluster services in Windows 2008 and Windows 2008 R2 the cluster core resources – cluster name is a Kerberos enabled name. This requires that a machine account be created within the directory for association with this cluster name resource. This is known as the CNO or cluster name object.
With previous versions of Exchange this Kerberos enabled machine account was created in the domain leveraging the credentials / rights assigned to the user logged into the machine using the failover cluster management tools to establish the clustered services. This would require either the user’s account have permissions to create and enable machine accounts within the domain or the machine account to be pre-staged with the appropriate rights assigned.
In Exchange 2010 the establishment of the cluster and the cluster name object is performed by using either the Exchange Management Console or Exchange Management Shell. Specifically the cluster creation occurs when running the command add-databaseavailabilitygroupserver when adding the first server to the database availability group. Since we are leveraging the Exchange management tools to establish the cluster service, this also means that we are utilizing RBAC. In this case when the first server is added to the DAG, the remote powershell contacts the replication service of the first node to be added. In turn, the replication service of that local machine installs the failover cluster management service and begins cluster creation utilizing the credentials assigned to LOCAL SYSTEM (since the replication service starts on the machine in the LOCAL SYSTEM security context). Therefore, the individual user rights to create machine accounts in the domain are not leveraged when establishing the clustered services for the database availability group, but rather that of the replication service.
In environments where computer account creation is restricted, it may become necessary to pre-stage the CNO for the clustered services and assign the appropriate rights. There are two methods which work to establish this security context:
1) Assign the machine account of the first node added to the DAG with full control of the pre-staged object.
2) Assign the Exchange Trusted Subsystem universal security group with full control of the pre-staged object.
The first method works by ensuring that the LOCAL SYSTEM security context will be able to manage the pre-staged computer account fully. The second method works because the Exchange Trusted Subsystem group contains the machine accounts of all Exchange servers in the domain. If utilizing method one you need to ensure that the first member added to the DAG is the machine granted permissions. If the second method is utilized any DAG member can be added as all members have rights to manage the account.
Here is an example of how to pre-stage the machine account utilizing the local system rights of the first DAG member.
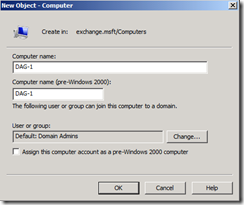
1) Select the appropriate container in Active Directory where you wish the account to be created. Right click, select NEW –> COMPUTER.
2) In the Computer Name field, type the name that was assigned to the database availability group.
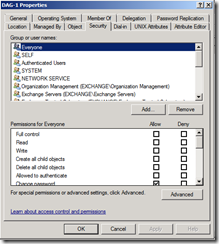
3) After the account is created, right click on the account and select properties. Select the security tab. (Note: You may have to enable advanced features in Active Directory Users and Computers).
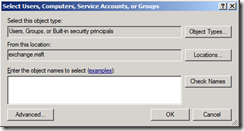
4) Select the ADD button to present the add dialog.
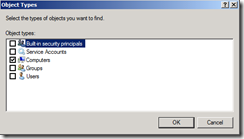
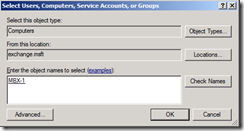
5) Select the Object Types button. De-select all options and select the COMPUTERS option. Press OK.
6) In the Enter the object name to select field, type the name of the first DAG member. Select Check Name to ensure the name resolves to a valid account in the directory. Select OK to add the account.
7) Select the machine account in the Group or User Names field, assign the machine account full control. Press OK.
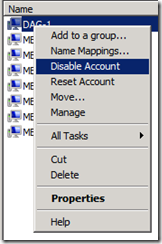
8) Locate the account in the container where it was created. Right click on the account and select disable account.
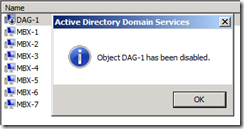
9) When presented with the disable dialog, select YES.
10) After the object has been successfully disabled, press the OK button on the success confirmation.
11) At this point allow time for active directory replication to occur. Once replication has completed, the first database availability group member can be added and the cluster services established.
======================================
Update 3/14/2010
======================================
It was recently asked how can I programmatically achieve establishing these permissions? Thanks to Jeff Kizner and Robert Gillies for providing these instructions.
cd ad:
$comp = Get-ADComputer DAG01
$sid = (Get-ADGroup "Exchange Trusted Subsystem").sid
$rights = [System.DirectoryServices.ActiveDirectoryRights]::GenericAll
$perm = [System.Security.AccessControl.AccessControlType]::Allow
$acl = get-acl $comp
$ace = new-object System.DirectoryServices.ActiveDirectoryAccessRule $sid, $rights, $perm
$acl.AddAccessRule($ace)
set-acl -AclObject $acl $comp
======================================