More on DigiNotar Certificates, and September Bulletins
In an effort to protect customers, last week we released Security Advisory 2607712 along with a non-security update to add fraudulent DigiNotar certificates to the Windows Untrusted Certificate Store. Today, we are releasing another update (2616676), adding six additional DigiNotar root certificates that are cross-signed by Entrust and GTE, to the Untrusted Certificate Store. Update 2616676 supersedes 2607712 and contains the full list of certificates which are:
- DigiNotar Root CA
- DigiNotar Root CA G2
- DigiNotar PKIoverheid CA Overheid
- DigiNotar PKIoverheid CA Organisatie - G2
- DigiNotar PKIoverheid CA Overheid en Bedrijven
- DigiNotar Root CA Issued by Entrust (2 certificates)*
- DigiNotar Services 1024 CA Issued by Entrust*
- Diginotar Cyber CA Issued by GTE CyberTrust (3 certificates)*
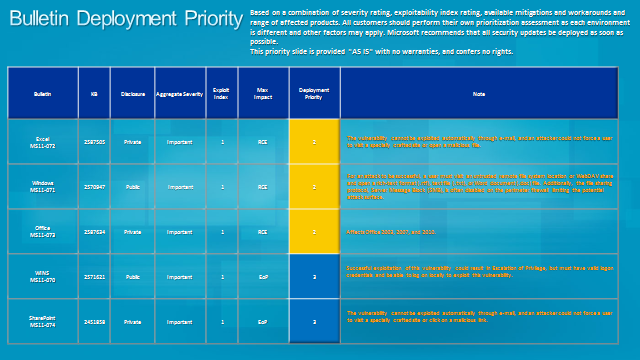
Today, we are also releasing five Important security bulletins as part of our regular monthly release cycle to help protect customers using Microsoft Windows and Microsoft Office. As always, we encourage that customers test and deploy all security updates as soon as possible to protect their systems, but because we did not rate any of September’s updates Critical, we are not giving any a level 1 deployment priority.
In this video, Jerry Bryant discusses this month's bulletins in further detail:
Below is our deployment priority guidance to further assist customers in their deployment planning (click for larger view).
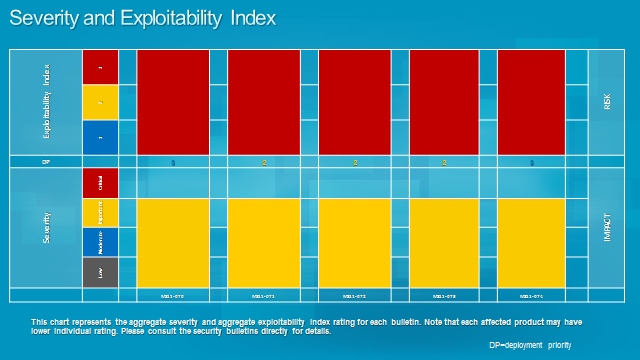
Our risk and impact graph shows an aggregate view of this month's severity and exploitability index ratings (click for larger view).
You can find more information about this month's security updates on the Microsoft Security Bulletin Summary web page.
Per our usual process, we’ll offer the monthly technical webcast on Wednesday, hosted by Jerry Bryant and Dustin Childs. We invite you to tune in and learn more about the September security bulletins, and ask any questions you might have. We’ve scheduled the webcast for Wednesday, September 14, 2011 at 11 a.m. PDT and you can register here.
You can also follow the MSRC team on Twitter at @MSFTSecResponse for all the latest information.
Thank you,
Pete Voss
Trustworthy Computing