Loss of "ssh" via VIP following the assignment of IP addresses to Linux VM's with multi-nic
Problem:
When creating a VM with multi nic and multiple subnets the Guests "Defualt
Gateway" is not automatically set. This can cause loss of "ssh"
connectivity as the "Default Gateway" is not assigned to the correct NIC
listening for incoming traffic.
The ammount of NIC's that you can assign to a VM is documented here
This is not an Azure problem but is a Linux routing configuration requirement.
Symptoms:
Loss of "ssh" as incorrect Default Gateway is set.
Troubleshooting:
Azure Support staff can verify the serial logs to see if the "Default Gateway" is not
assigned to the correct network.
Alternatively, "ssh" access is possible from a VM in the same Cloud Service as this will use
the Private DIP address and verify one of your logs depending on the OS you are running. It will be one of dmesg,kern.log, messages or boot.log
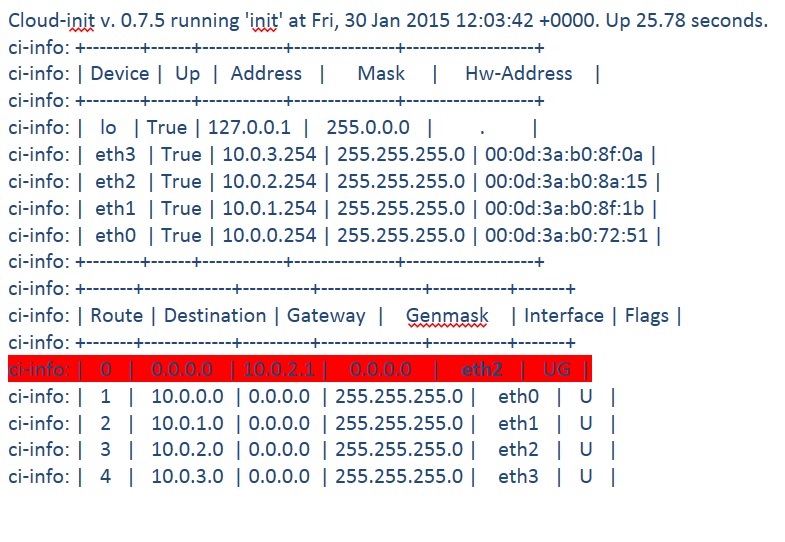
Ubuntu
On this VM we see 4 NIC cards and the
Gateway denoted by UG is assigned to eth2 and not eth0
Solution:
A restart may temporarily fix this and the correct Default Gateway might be assigned.
However, "ssh" access is possible from a VM in the same Cloud Service as this will use
the Private DIP address and a permanent solution should be adopted.
Ubuntu
A permanent solution for an Ubuntu vm (tested on 14.x)
Create a script on the VM with multi-nic to clean up all incorrect "Default Gateway" routes, Which will be executed when networking starts at boot. This will assign the correct network. In this example, eth0 is used as the "Default Gateway" which maps to the network 10.0.0.1
vi /etc/network/if-up.d/defaultgw
#!/bin/sh
route delete default gw 10.0.1.1
route delete default gw 10.0.2.1
route delete default gw 10.0.3.1
route add default gw 10.0.0.1
Set the correct privilieges on the file
chmod 755 /etc/network/if-up.d/defaultgw
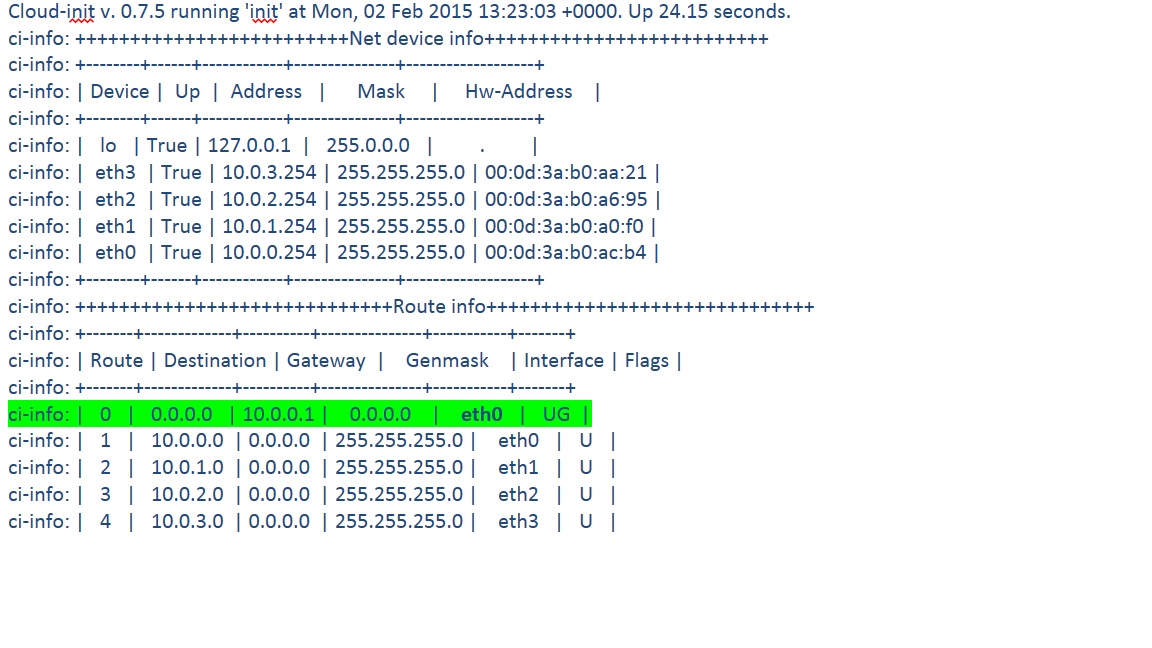
reboot the VM and you will observe that the correct Default Gateway is set and
as such "ssh" will be possible via the VIP/port
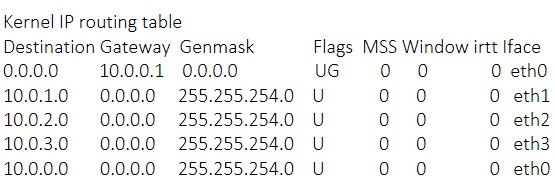
Verify with netstat -rn or route -n
CentOS 6.5
In CentOS append the directive of "GATEWAY" in the file
/etc/sysconfig/network
Taking the above example the configuration file could look like this
HOSTNAME=myvmname
NETWORKING=yes
GATEWAY=10.0.0.1
References:
Blogs:
Documentation:
https://msdn.microsoft.com/en-us/library/azure/dn848315.aspx