Discovery and Risk Assessment Server 2013 - Risk Configuration
The following is an overview of Risk Configuration in Microsoft Discovery and Risk Assessment Server 2013 to help you understand how to define risk.
Risk is defined as a function of Materiality and Complexity.
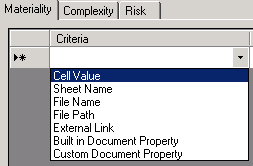
- Materiality – Sensitivity of the document. Based on contents within the file or attributes of the file
- Complexity – Statistics of the file as a function of the features of Excel / Access that are used
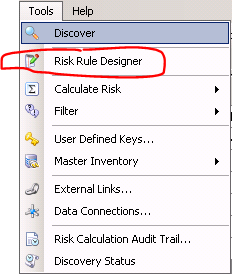
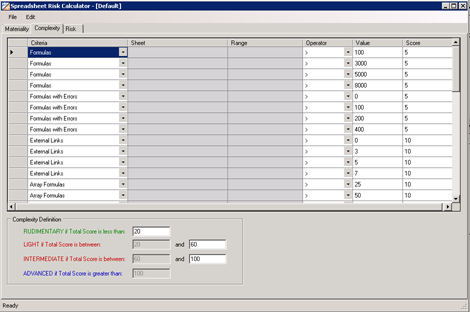
- Risk Rule Designer
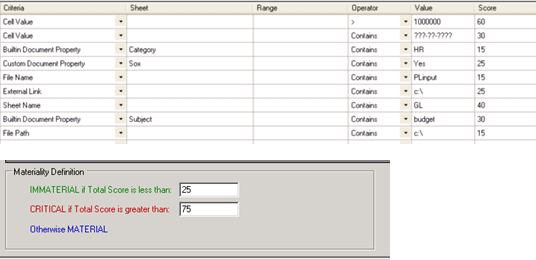
- Point-scoring system for Materiality, Complexity, and Risk
- Publishes a risk definition file (.rsk)
- Accessed from the Tools menu
- Parameters can be filtered to a specific sheet and/or range of cells, if needed.
- Built-in and custom document properties leverage the “Sheet” property to define which property to analyze.
- There are 3 categories of Materiality based on the score:
- Immaterial
- Material
- Critical
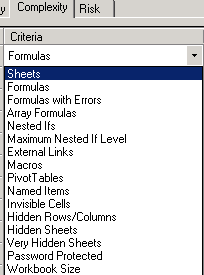
- Complexity analyzes the contents of the spreadsheet to determine which features & functions are used and in what frequency.
- Complexity rules can analyze and identify
- Scoring methodology similar to materiality scoring.
- There are 4 categories of Complexity based on the score:
- Rudimentary
- Light
- Intermediate
- Advanced
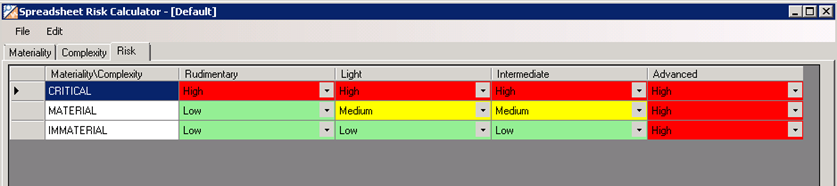
- Risk is a function of Materiality and Complexity
- Using the configurable grid, you can adjust levels as needed. Material goes by rows, and Complexity goes by columns. You define the Risk level at each intersecting point.
- Files that score high in Materiality and Complexity would normally by High risk files, and files that score low in Materiality and Complexity would be Low risk files.
- There are 3 categories of Risk based on the Materiality and Complexity levels:
- Low
- Medium
- High
After defining risk using the Risk Rule Designer, also called Spreadsheet Risk Calculator, you can run a Risk Assessment on your files to check file content and structure to determine the risk level of each file.