Step By Step Guide: IPsec NAP Enforcement in a Test Lab
The NAP team has just released a Step-by-Step guide to setting up IPsec NAP Enforcement in a Test Lab.
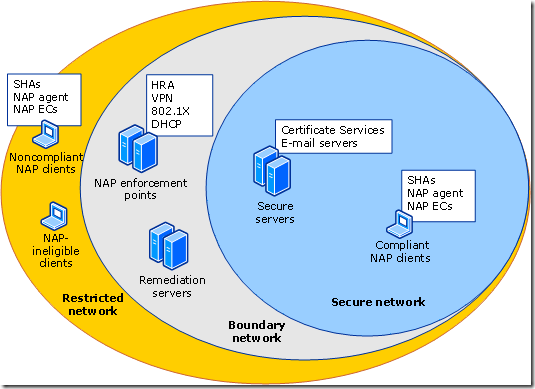
This paper contains an introduction to NAP and instructions for setting up a test lab and deploying NAP with the IPsec enforcement method using two server computers and two client computers. The test lab lets you create and enforce client health requirements using NAP and IPsec.
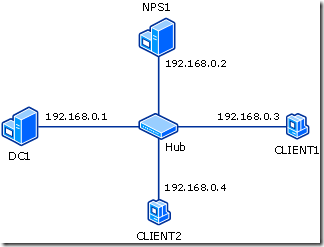
The test lab consists of an intranet network assigned a private IP address range of 192.168.0.0/24 that is connected by a hub or switch.
In the test lab, NPS1 is on the boundary network, CLIENT1 is on the secure network, and CLIENT2 moves between the secure and restricted network, depending on its health status.
Download the rest of the guide here: https://www.microsoft.com/downloads/details.aspx?familyid=298ff956-1e6c-4d97-a3ed-7e7ffc4bed32&displaylang=en&tm