Clean up after your server!
While learning about the changes in Active Directory on Windows Server 2008 at a recent conference, the presenters casually mentioned a new feature as an aside that is actually quite exciting!
If you have ever had a Domain Controller stolen or experience catastrophic hardware failure, then you are familiar with the joy that is manually cleaning up the DC metadata in Active Directory with NTDSUTIL. (This KB article has all the steps in case you have trouble going to sleep. Daniel Petri also has a good write-up here). It is a painful experience to say the least.
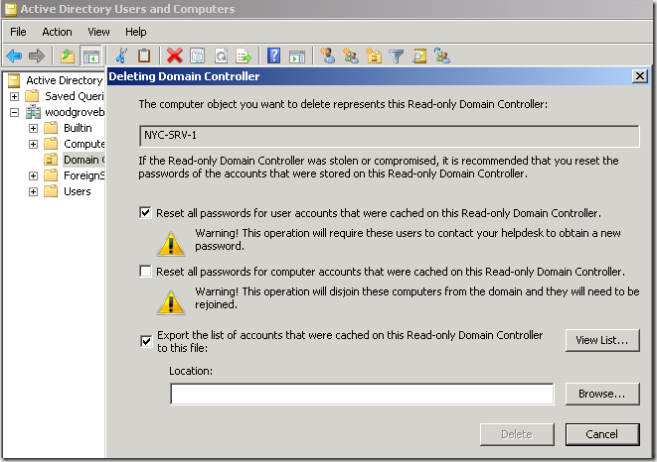
With the advent of the Read-Only Domain Controller role with Windows Server 2008, the Active Directory team has planned for the eventuality that a Domain Controller at a branch office (where it is likely stuck in the Janitor's closet or under a desk) will be stolen. As the RODC only caches the credentials of the users at the branch office, there is no need to reset every password within the Enterprise, you can simply reset the passwords for the few users at the branch office.
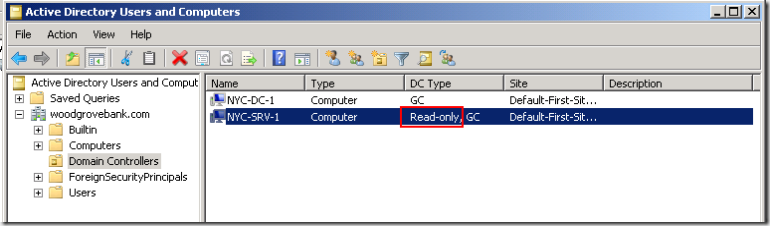
You open up Active Directory Users and Computers
Right click on the stolen DC
Delete
You will be given the option to reset the passwords of the Users that were present on the RODC, export the user list to a file, and then the wizard will clean up all references to that RODC FOR you. No messy ntdsutil work.
I checked with the presenters after the session, and this server cleanup also works swimmingly on a writeable Domain Controller. If you have a catastrophic hardware failure and the Domain Controller has died for all time, you can go into the ADUC GUI and delete the diseased DC. You will not receive the option to reset user accounts (as you would on the RDC), but all lingering metadata in AD relating to that server will be gone.
Making your life as a Windows Server Administrator easier... one feature at a time :)
For more reading, I would recommend: