Update Services in SBS 2008
[Today’s post comes to us courtesy of Shawn Sullivan]
SBS 2008 includes the Update Services component to provide the administrator with a simple interface for managing software updates from the SBS Console. Those who are familiar with Update Services from SBS 2003 R2 will find that the SBS 2008 implementation is quite similar. It is essentially a wrapper for the native WSUS 3.0 interface meant to simplify the management of software updates for the network. By default all critical updates, security updates, and update definitions will be automatically approved for installation if at least one machine on the network requires it. Other updates are manually approved by the administrator as needed.
Default Configuration Settings
Below is the full list of default configuration settings in WSUS as they exist after SBS 2008 setup has completed:
| Parameters | Settings |
| Update Classifications | Critical Updates Definition Updates Security Updates Service Packs Update Rollups |
| Products | All |
| Languages | English and the Language of the SBS 2008 SKU |
| Update Files | Store update files locally on this server Download update files to this server only when updates are approved |
| Synchronization | Automatically 01:00 am Daily |
| Server Cleanup | Unused updates and update revisions Computers not contacting the server Unneeded update files Expired updates Superseded updates |
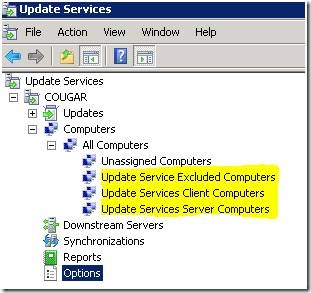
| WSUS Groups | Update Service Excluded Computers Update Services Client Computers Update Services Server Computers |
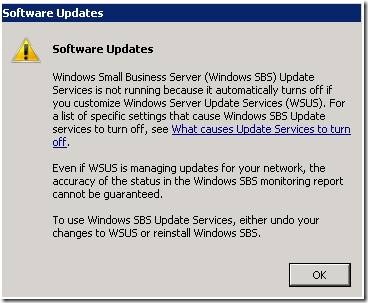
Important: If you go into the native WSUS 3.0 SP1 console and change these default settings, SBS Update Services will detect this and shut down. In order to guarantee the accuracy and reliability of its reporting function, it requires WSUS to be configured with these settings. If you are in this state, you will get the following warning when you click on “Change the software update settings” in the SBS console:
“Windows Small Business Server (Windows SBS) Update Services is not running because it automatically turns off if you customize Windows Server Update Services (WSUS)”
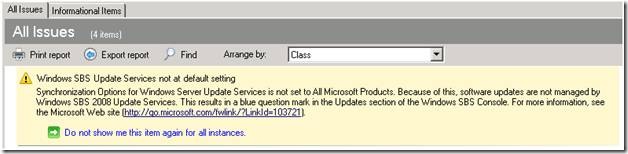
The easiest way to tell which changes you need to revert is to run the SBS 2008 BPA: https://www.microsoft.com/downloads/info.aspx?na=22&p=1&SrcDisplayLang=en&SrcCategoryId=&SrcFamilyId=&u=%2fdownloads%2fdetails.aspx%3fFamilyID%3d86a1aa32-9814-484e-bd43-3e42aec7f731%26DisplayLang%3den
The below screenshot shows an example of the warning and its specific cause:
WSUS Update Groups
The Update Services Excluded Computers, Update Services Client Computers, and Update Services Server Computers groups are created natively in WSUS during setup and managed through the SBS 2008 Console.
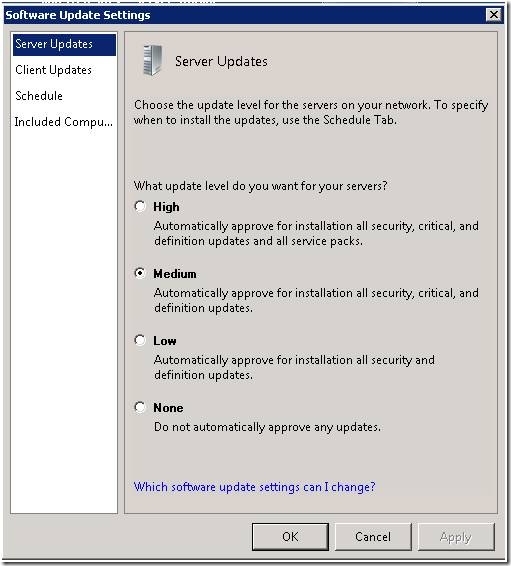
By default, the Client and Server groups will be populated by machine accounts that are either in the SBS Servers or SBS Computers Organizational Units in Active Directory. The purpose of these groups is to assign one of the following update levels to them through the SBS Console:
- High: Automatically approve for installation all security, critical, and definition updates and all service packs
- Medium: Automatically approve for installation all security, critical, and definition updates
- Low: Automatically approve for installation all security and definition updates.
- None: Do not automatically approve any updates
By default, Server updates are set to Medium and client updates are set to High. If you choose to exclude a machine from receiving updates through Update Services, then they will be placed in the Excluded Computers group.
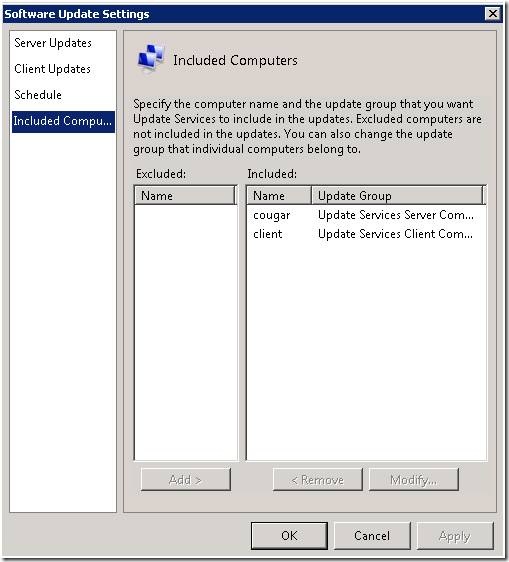
Included Computers adds the machine account to the proper WSUS group and to the security filter of either the Update Services Client Computers or Update Services Server Computers GPOs:
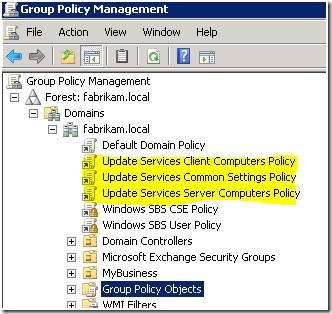
WSUS Group Policy Objects
These GPOs control various settings in how machines in your network contact WSUS. You should not make changes to them:
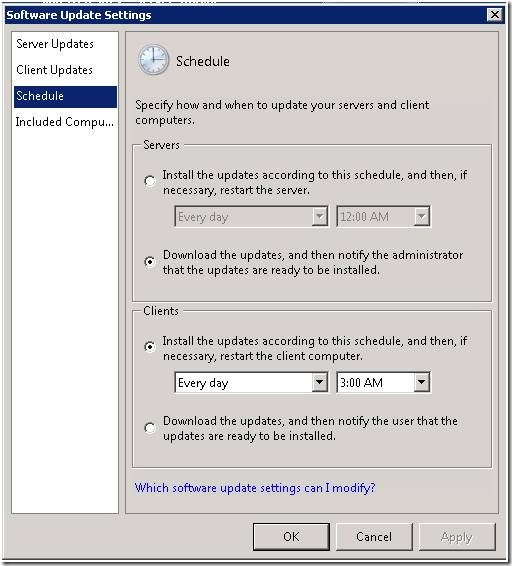
- Update Services Client Computers Policy: Configures client machines to “auto download and schedule the install” everyday at 03:00.
- Update Services Server Computers Policy: Configures server machines to “auto download and notify for install”. Updates will never be automatically installed.
- Update Services Common Settings Policy: Settings common to both servers and clients, include update detection frequency, system restart settings, scheduled installation settings, and the URL that machines contact for Update Services and intranet statistics ( :8530">https://<SBSServer>:8530 )
Windows SBS Manager Service
Among its many responsibilities, this service applies all of the configuration settings that the administrator has chosen through the SBS 2008 Console. It performs the following tasks:
- Every 5 minutes it will check Active Directory and apply machine accounts to the proper WSUS Update Group, either the Client Computers or the Server Computers group. It also adds the machine account to the security filter of either the client or server GPOs. This is all configured by the administrator in the “Included Computers” window in Figure 2 above.
- Every 60 minutes it checks with WSUS to review the updates being reported as needed by the machines. At this time, it will approve critical, security, and update definitions for all machines while including service packs for machines in the Client Update group.
The logs for this service are found in the following directory: C:\Program Files\Windows Small Business Server\Logs\MonitoringServiceLogs.
Administration through the SBS 2008 Console
All of the pieces described above are brought together to give the administrator a simplified interface in the SBS 2008 Console in which to manage all updates for all machines on the network. You can access Update services information from the following locations:
- Under “Network Essentials Summary” on the Home tab: If all updates that are needed have not been installed, you will receive a Warning here. If you have made changes to the default WSUS configuration, you will also receive a blue question mark here
- Under the “Computers” sub-tab on the Network tab: Right-click on the machine accounts and go to properties to access the list of missing and installed updates.
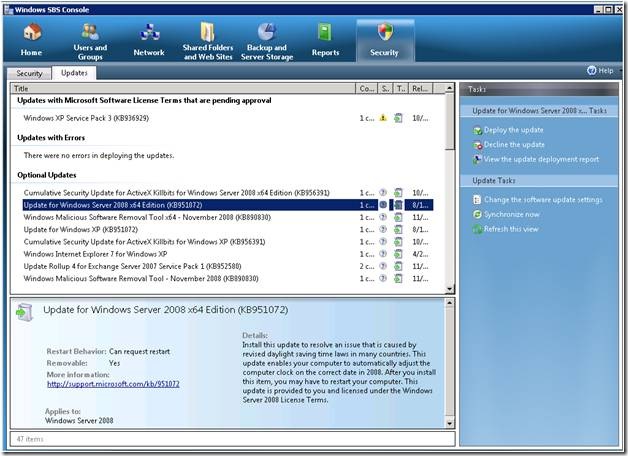
- Under the “Updates” sub-tab on the “Security” tab: At this location, you can “Change the software update settings” to change the update levels for servers and clients, specify the schedule for installation or notify the user, and choose which servers and clients to manage through Update services:
You also receive a list of Updates with Microsoft Software License Terms that are pending approval, Updates with Errors, Optional Updates and Updates in Progress. From here you can deploy the update, decline the update, or view the update deployment report: