Exchange (2007-2010-2013) – Error when trying to Enable-ExchangeCertificate: PrivateKeyMissing – or – how to ensure that when you import an issued certificate you get the private key generated
This post is more a reminder on the main rule on what not to do when installing a certificate that you requested using Exchange or IIS. Why this reminder? Because even I forget all the times (I’m not playing with Certificates everyday).
- Cert from the CA HAS to be imported on the SAME server where you made the REQUEST from so that you get the Private Key. E.g. you made the request (using New-ExchangeCertificate OR via IIS) on <SERVER 1>, you sent the CA the cert request, then you HAVE to import the certificate that the CA issued you on <SERVER 1>(using Import-ExchangeCertificate or IIS).
- don’t use MMC to import a certificate you get back from the CA as it won’t associate the Private Key either.
Here is an excellent reminder as well from DIGICERT.COM:
Error message: "The certificate with thumbprint... was found but is not valid for use with Exchange Server (reason: PrivateKeyMissing)."
Cause 1: Most common cause of this issue is that a server admin imported the .crt/.cer/.p7b SSL Certificate files through MMC and not through the Exchange command line or IIS where the request was generated.
Importing stand-alone certificate files through MMC does not associate those files with their private key. SSL Certificates can only be imported via MMC if they have already been installed to their private key and then backed up to a .pfx file.
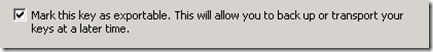
Cause 2: An admin correctly imported the certificates to one server but then backed up the certificate files to a .pfx without backing up the private key.
(------------------------------[Sam’s note]------------------------------- “checkbox “mark private key exportable or when using New-ExchangeCertificate blabla –PrivateKeyExportable:$true] example:
or
New-ExchangeCertificate -GenerateRequest -SubjectName "c=CA, o=CONTOSO, cn=globule.contoso.ca" -DomainName webmail.contoso.ca,sammy.contoso.ca,autodiscover.contoso.ca -PrivateKeyExportable $true
--------------------------------[end of Sam’s note]----------------------)
Source: https://www.digicert.com/ssl-support/exchange-private-key-missing.htm