Software Defined Networking – Hybrid Clouds using Hyper-V Network Virtualization (Part 3)
Hello Readers and Viewers!
Welcome to the last part (3 of 3) of this blog series on Software Defined Networking.
In the previous post we have examined how multi-tenant S2S VPN and NAT provide different modes of connectivity to VMs of different tenants with overlapping IP addresses hosted in Fabrikam network. In this post we will examine how Fabrikam is able to deploy disaster recovery as service using these technologies.
Bring it all Together: Cloud Based Disaster Recovery using Windows Server 2012 R2
Scenario overview:
Fabrikam offers Disaster Recovery as a Service, it allows its tenants to replicate their VMs to Fabrikam data center. If the VMs have to be recovered, they are booted up, connected to the tenant virtual network and assigned IP addresses of the tenant virtual network. Once the VMs are connected to the tenant virtual network they are accessible via VPN (Site to Site & Point to Site) and the VMs can access Internet resources via NAT. Also Fabrikam is able to offer self-service cloud services portal for its customers to be able to consume, configure their Networks, enable direct access to internet, or setup their VPN (S2S & P2S) connectivity to the premises.
We will first examine how Contoso is able to replicate its VMs to Fabrikam and access them “post recovery” over Point to Site VPN using multi-tenant gateway. We will also examine how Woodgrove is able to replicate its VMs from New York site (NY) to Fabrikam. In the case of disaster in NY site, all the critical VMs are restored in Fabrikam and are accessible from San Francisco (SFO) site of Woodgrove.
For Replication we assume Hyper-V Replica feature in Windows server is deployed. This link has details of necessary Hyper-v Replica configuration required on the hosts.
Setting up the Disaster Recovery Infrastructure
Setting up Fabrikam network to allow Disaster Recovery involves the following operations:
- Step 1: Facilitating replication of VMs from different tenants to Fabrikam data center
- Step 2: During recovery of VMs : connecting the VMs to tenant virtual networks
- Step 3: Enabling connectivity of the VMs in tenant network to external networks.
Step 1: Enable Replication of VMs to Fabrikam data center
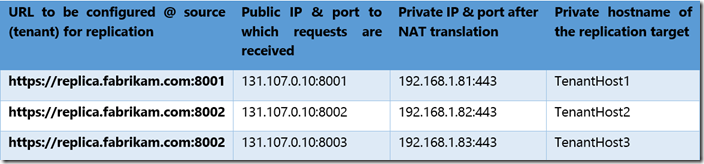
To enable replication of VMs using Hyper-v Replica, the hosts that are the target of the replication need to be accessible by name from tenant sites. To enable multiple hosts as target of replication, Fabrikam can use an FQDN such as replica.fabrikam.com and route traffic to different hosts based on port number. For instance Fabrikam deploys three host with internal names TenantHost1, TenantHost2 and TenantHost3 mapped to different port numbers. Using a single name allows Fabrikam to scale the service dynamically without making any other infrastructure changes like DNS or acquiring more public IPs. Fabrikam avoids wasting multiple public IPs by deploying NAT and assigning IPs in private address range. The following table illustrates a sample URL to IP to end host mappings:
This approach enables Fabrikam to add new hosts to the cluster of replica servers by just adding entries in NAT.
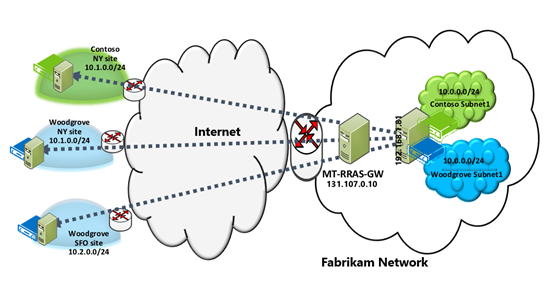
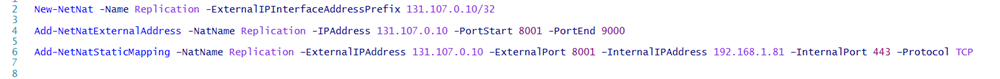
The above diagram show Woodgrove and Contoso replicating VMs with identical IP address (10.1.0.10) to same host with IP address 192.168.1.81. The host is behind MTGatewayVM with public IP 131.107.0.10. MTGatewayVM performs NAT on incoming packets to send traffic to host 192.168.1.81. The following cmdlet enables NAT on GW-VM:
The last cmdlet adds the necessary NAT mapping so that replica traffic to 131.107.0.10:8001 is translated to IP address 192.168.1.81. To add another replica server Fabrikam admin needs to add just another NAT address like this.
This is the network configuration required on MTGatewayVM so that data path is setup at Fabrikam for tenants to replicate their VMs.
NOTE: To ensure protection of MTGatewayVM, Fabrikam will have to deploy firewall on the device that connects to the Gateway
Step 2: Connecting the VM to tenant virtual networks
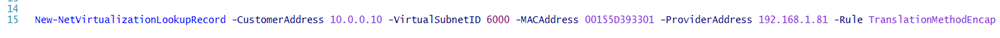
Once the initial replication of the VM is complete, the VNIC of the VM is connected to Fabrikam network. To ensure that VM ContosoVM01 is connected to Contoso virtual network, the following cmdlet is executed on TenantHost1:
New-NetVirtualizationLookupRecord -CustomerAddress 10.0.0.10 -VirtualSubnetID 6000 -MACAddress 00155D393301 -ProviderAddress 192.168.1.81 -Rule TranslationMethodEncap
The same cmdlet needs to be executed on all hosts that have Contoso VMs in virtual subnet 6000. After this configuration, whenever Contoso VM is booted up it will be part of Contoso virtual subnet 6000.
NOTE: You can't change replica VM through Virtual Machine Manager (Set-VM is blocked for replica VM in VMM), HNV PowerShell APIs have been used instead in this step. However, It is recommended to use Windows Azure Hyper-V Recovery Manager (HVRM) to help protect your business critical services by coordinating and orchestrating the replication and recovery of Virtual Machines at a secondary location. HVRM provides network pairing and auto attaching the replica VM to the target VM network. This link provides a quick walkthrough of the steps required to deploy Hyper-V Recovery Manager. For more detailed explanations and procedures read the following:
- Planning Guide for Hyper-V Recovery Manager—This guide summarizes the prerequisites and the planning steps you should complete before starting a full deployment of Hyper-V Recovery Manager.
- Deployment Guide for Hyper-V Recovery Manager—This guide provides detailed step-by-step deployment instructions for a full deployment.
Step 3: Enabling external connectivity of VMs
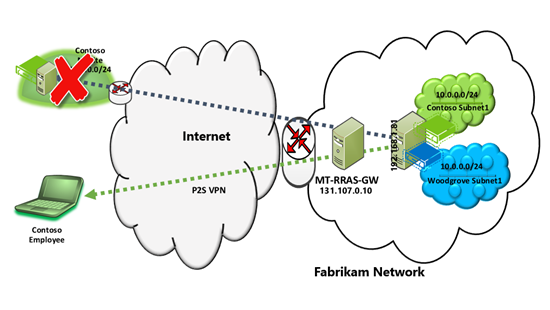
After tenant VMs are replicated and brought up in Fabrikam network, the VMs need to be made accessible to external networks. For businesses like Contoso that have a single office site, in the event of a disaster when their on-prem VMs are not available, their employees will be able to access Contoso VMs by VPN. The steps to enable VPN on MTGatewayVM have been detailed in part 2 of this blog series. To enable Contoso VM with IP address 10.0.0.10 to access Internet servers, NAT needs to be configured on MTGatewayVM. Details of NAT configuration are available in part 2 as well.
As shown in the below diagram, employees of Contoso are able to access Contoso VMs (through Point to Site VPN connection) in spite of their only office in New York not being available.
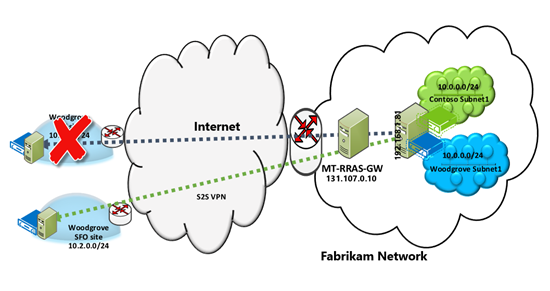
Now let’s examine how enterprises such a Woodgrove bank are able to utilize Fabrikam services and ensure availability of access to their business critical applications.
In the below diagram, after Woodgrove New York site becomes unavailable, the VMs are brought up in Woodgrove virtual network at Fabrikam. Their VMs come up with the same IP addresses as in New York site. Applications in Woodgrove SFO site access these VMs just as they were accessing them when the VMs were in NY site. With Border Gateway Protocol (BGP), no additional changes are required on Woodgrove SFO site to route traffic to 10.0.0.0/24 via S2S VPN to Fabrikam. This is how it happens:
- When Woodgrove NY site goes down, the route 10.0.0.0/24 that is present over S2S VPN interface to NY site is removed by BGP as peering goes down.
- Once subnet 10.0.0.0/24 route is added in Woodgrove compartment on MTGatewayVM, BGP on Woodgrove SFO router adds route 10.0.0.0/24 on S2S VPN interface to Fabrikam.
Fabrikam also offers its customers self-service, multi-tenant cloud portal to enable them to provision, configure and consume virtual networking infrastructure. The following section details the steps Tenant Administrator should follow to provision their virtual network infrastructure.
Managing Virtual Network Infrastructure using Windows Azure Pack
With Windows Azure pack for Windows Server, Fabrikam offers multi-tenant cloud services portal for its customers to be able to configure their Virtual Networks, enable direct access to internet using NAT, and setup their VPN connectivity (S2S & P2S) to the premises.
In this section we will walk through the steps Tenant admin follows to provision their network services from the Tenant Management Portal.
NOTE: This section does not provide information for deploying and configuring Windows Azure Pack to support VM Clouds scenarios. For more information about the product on this link.
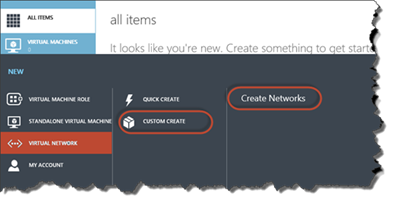
1. After being authenticated, the initial page is shown below. Tenant admin can chooses various services offered by Fabrikam.
2. To create a new VM network, Tenant Admin clicks on “+NEW” option, Select Virtual Network, and Click “Custom Create” option
3. On Selecting “Create Networks” the following web page is shown where the administrator can specify the name of the virtual network and choose between IPv4 or IPv6.
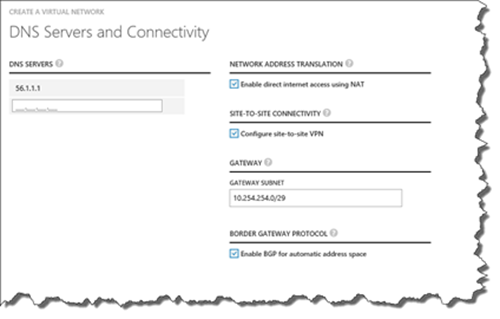
4. On the next page, details of various gateway services offered are provided and administrators can choose the services that need to be configured for the virtual network.
The DNS server address specified here will be configured in the IP Pool options for the tenant virtual network so that VMs in the virtual network are configured with the specified DNS server.
Enabling NAT allows VMs in the virtual network to access Internet resources.
Enabling site-to-site connectivity allows connectivity between VMs in tenant virtual network and tenant premises networks.
Enabling BGP allows tenant routes between tenant premises sites and virtual networks to be exchanged via BGP without need for manual route configuration.
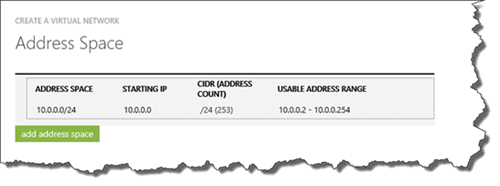
The gateway subnet is the subnet of the tenant compartment on gateway VM. Contoso administrator should ensure that this subnet does not overlap with any other IP subnet in any of the sites of Contoso. The VSID interface in the tenant compartment is assigned the IP address from the second IP of the subnet. Based on the parameters provided on the above screen, the VSID interface will be assigned IP address 10.254.254.2. IP address 10.254.254.1 is reserved for HNV distributed router. All the traffic to subnets that are not present in the virtual network for the tenant are routed to 10.254.254.1. HNV distributed router then routes all the traffic to 10.254.254.2 and the packets land up in the tenant compartment on the gateway. From the tenant compartment if a matching route is found on any of the interfaces, traffic is forwarded on that interface. Otherwise the traffic is NAT’ed (assuming there is a matching route in the default compartment). If a matching route is found on S2S interface in tenant compartment, the traffic is forwarded securely to the corresponding tenant site via S2S VPN.5. Next the tenant administrator needs to specify the address space for its virtual network.
6. The next page allows to specify details of the Site to Site VPN:
The Name of the connection is used to create the S2S interface on the gateway.
VPN Device IP address is the address of the VPN device at tenant premises. This address is configured as the destination address on S2S interface.
Shared Key is the key used for authentication of S2S connection.
All the static routes that need to be added on S2S interface need to be specified. If BGP is not enabled all the routes of the enterprise premises need to be specified here. If BGP is enabled, the subnet to which the BGP peer in the enterprise belongs to needs to be specified.
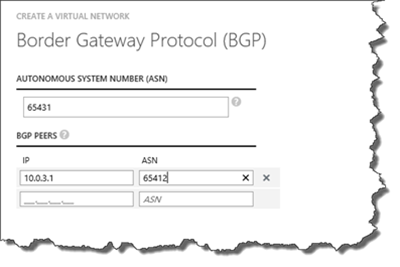
7. The next page in the wizard allows the administrator to specify BGP parameters
The Contoso virtual network in Fabrikam needs to be assigned an ASN number. For each of the BGP peers in Tenant premises, their IP address and ANS numbers have to be specified. The BGP router in Tenant compartment tries to peer with each of the specified on-premises peers.
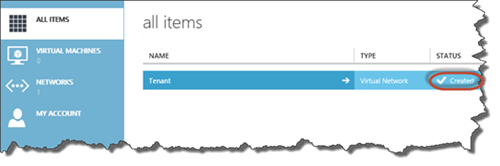
8. After successfully provisioning the virtual network the below page is shown.
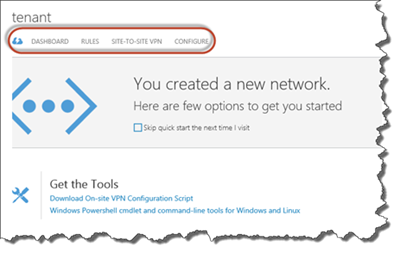
9. After creating the virtual networks through the mentioned flow, the tenant can specify additional parameters by clicking on the virtual network in the above page. The below page allows the administrator to specify more options. As shown in the page, Tenant administrator can download VPN scripts to configure his premises VPN devices.
10. On selecting “Rules” tab, NAT rules are displayed. On selecting “Site-To-Site VPN” the page with all configured S2S VPN connections is displayed. Tenant administrator can select a specific VPN connection and click edit to modify parameters of VPN connection. The IP addresses of the VPN device in enterprise premises can be modified in the below page.
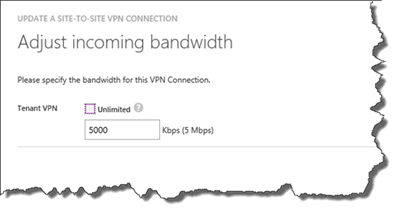
11. The next pages allow updating the Routes within the network behind the VPN device, also specifying bandwidth limits in each direction for the selected Site-to-Site VPN interface.
That’s it!
In this post we have seen how the following technologies introduced in Windows Server 2012 R2 enable cloud service providers like Fabrikam to provide at scale disaster recovery as a service to enterprise and small and medium business:
- Hyper-V Network Virtualization
- Hyper-V Replica
- Multi-tenant TCP/IP stack
- Multi-tenant NAT
- Multi-tenant S2S VPN
- Multi-tenant Remote Access VPN
- Multi-tenant BGP
I hope this Blog post series have provided you with helpful overview of the SDN solution, specifically Hyper-V Network Virtualization. Thanks for taking a look!
Also I would like to thank my colleagues Uma Mahesh Mudigonda and CJ Williams for providing inputs.