Security Focus: Report on Unconstrained Delegation
Last week I showed how to report on Constrained Delegation. This week, I'll show you how to report on Unconstrained Delegation.
What's the difference?
"...The feature that allows an application to act on behalf of a user is known as Kerberos Delegation. It has to be explicitly enabled for trusted services on a trusted computer. It can be switched on for a service account running the service or for the computer's Local System account (all services running as Local System). It can be unconstrained, i.e. the application can impersonate the user anywhere else within the forest or across a trust, or it can be constrained, i.e. the application can only impersonate the user to a specific service on a specific computer.
If a trusted computer is compromised, the trusted application could act on behalf of any user that has presented itself to the service to perform malicious activity..."
Unconstrained is bad. Think of it as giving the trusted computer or service account your credential to use where ever it likes within the forest or across trusts. The trusted principal impersonates you. t is you and you have no idea where your credential is being used. Bad, man.
Here's how to find objects in the current domain, that aren't read-write domain controllers, configured for unconstrained delegation.
$TRUSTED_FOR_DELEGATION = 0x80000
$SERVER_TRUST_ACCOUNT = 0x2000
$Findings = Get-ADObject -Filter {(UserAccountControl -band $TRUSTED_FOR_DELEGATION) -and (-not (UserAccountControl -band $SERVER_TRUST_ACCOUNT))}
if ($Findings) {
$Findings | Export-Csv -Path ".\TRUSTED_FOR_DELEGATION.csv"
}
User and Computer accounts have a property called UserAccountControl that stores a number of configuration settings The option that configures an account for unconstrained delegation is stored as part of a binary mask in the 'UserAccountControl' attribute of the user or computer object. In the binary mask, each positional bit represents a different possible user account option that can be switched on or switched off. Like a light switch - when switched on, the option is active. These settings can be queried using PowerShell's 'binary And' ( -band) operator. The hexadecimal setting for unconstrained delegation is 0x80000 and we use -band to check that it is present (switched on) in the binary mask.
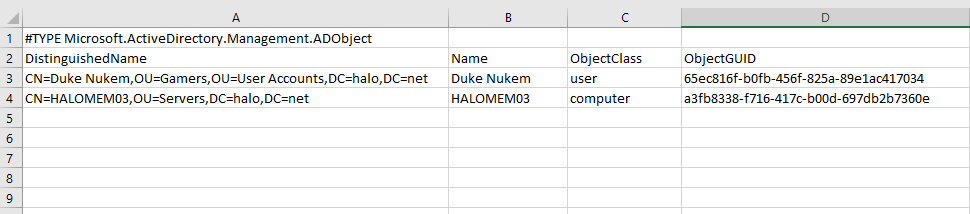
Here's an example of what the CSV might look like.
It's easy enough to turnoff unconstrained delegation with PowerShell.
Set-ADAccountControl -TrustedForDelegation $false -Identity "CN=HALOMEM03,OU=Servers,DC=halo,DC=net"
If you're interested in other options from UserAccountControl, then take a look below.
Property Flag |
Value in Hexadecimal |
Value in Decimal |
SCRIPT |
0x0001 |
1 |
ACCOUNTDISABLE |
0x0002 |
2 |
HOMEDIR_REQUIRED |
0x0008 |
8 |
LOCKOUT |
0x0010 |
16 |
PASSWD_NOTREQD |
0x0020 |
32 |
PASSWD_CANT_CHANGE |
0x0040 |
64 |
ENCRYPTED_TEXT_PWD_ALLOWED |
0x0080 |
128 |
TEMP_DUPLICATE_ACCOUNT |
0x0100 |
256 |
NORMAL_ACCOUNT |
0x0200 |
512 |
INTERDOMAIN_TRUST_ACCOUNT |
0x0800 |
2048 |
WORKSTATION_TRUST_ACCOUNT |
0x1000 |
4096 |
SERVER_TRUST_ACCOUNT |
0x2000 |
8192 |
DONT_EXPIRE_PASSWORD |
0x10000 |
65536 |
MNS_LOGON_ACCOUNT |
0x20000 |
131072 |
SMARTCARD_REQUIRED |
0x40000 |
262144 |
TRUSTED_FOR_DELEGATION |
0x80000 |
524288 |
NOT_DELEGATED |
0x100000 |
1048576 |
USE_DES_KEY_ONLY |
0x200000 |
2097152 |
DONT_REQ_PREAUTH |
0x400000 |
4194304 |
PASSWORD_EXPIRED |
0x800000 |
8388608 |
TRUSTED_TO_AUTH_FOR_DELEGATION |
0x1000000 |
16777216 |
PARTIAL_SECRETS_ACCOUNT |
0x04000000 |
67108864 |
R.I.P.