Defender PowerShell Module
As an IT professional it's almost a given that you provide free support to your immediate family, perhaps your not-so-immediate family, occasionally your good friends and sometimes your neighbour's dog!
The other day I was helping the father-in-law remove a third party anti-virus product to reactivate Windows Defender on his laptop.
I thought it would be a good opportunity to introduce him to some PowerShell!
Here's what we looked at...
Defender Status
This cmdlet gives you a view of how Defender is doing:
Get-MpComputerStatus
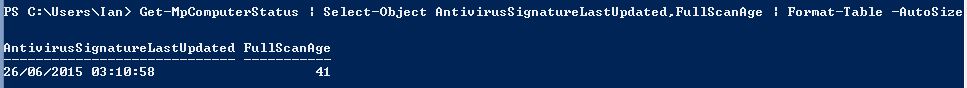
This command shows your signature file was lasted updated. It also shows you how many days ago the last full scan was performed:
Get-MpComputerStatus | Select-Object AntivirusSignatureLastUpdated,FullScanAge
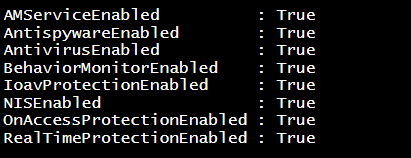
This one shows whether the defender subcomponents are enabled:
Get-MpComputerStatus |
Select-Object -Property AMServiceEnabled, `
AntispywareEnabled, `
AntivirusEnabled, `
BehaviorMonitorEnabled, `
IoavProtectionEnabled, `
NISEnabled, `
OnAccessProtectionEnabled, `
RealTimeProtectionEnabled
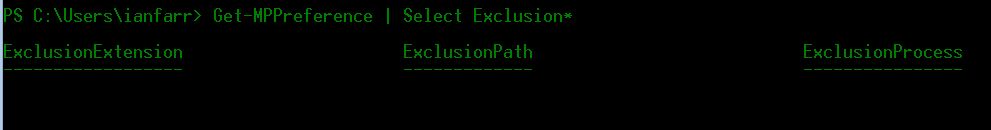
What about exclusions?
Get-MPPreference | Select Exclusion*
Threats
Has anything been detected?
Get-MpThreat
If anything comes back, pay particular attention to the IsActive and DidThreatExecute properties.
Want to know what threats defender checks for? This makes for very interesting reading:
(Get-MpThreatCatalog).ThreatName | Sort-Object | Out-File .\threat_names.txt
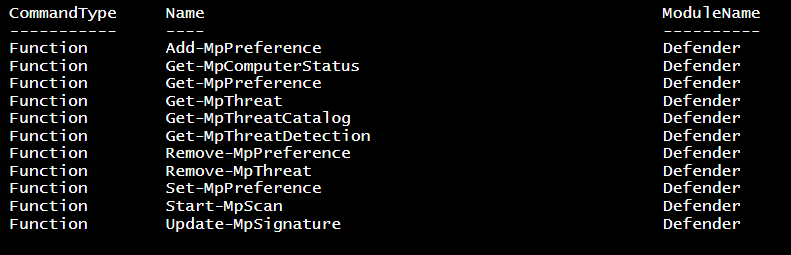
Defender Module
Run this:
Get-Command -Module defender
Notice the Start-MPScan cmdlet. Have a play; go on now; don't be shy!
Well, I'm sad to say that the father-in-law struggled to see the awesomeness of PowerShell, but this was a good start - one battle a war does not make!