Managing Azure VMs with PS Remoting
I'm a BIG fan of Microsoft Azure. I'm also a BIG fan of dystopian novels. What have the two got in common? Nothing, AFAIK, although I'm sure some tenuous links could be found by the hard-of-sleeping...
Blimey, I'm off topic already... so, Microsoft Azure...
I'm an even BIGGER fan of remotely managing my Azure VMs from my laptop with PowerShell. In this post, I'm going to discuss what you need to do to achieve this.
First up, to manage your Azure subscription with PowerShell you'll need the Azure PowerShell module:
How to: Install Azure PowerShell
Next, you'll need to download and import your subscription's publishSettings file. This cmdlet helps you perform the necessary authentication and download:
Get-AzurePublishSettingsFile
This cmdlet performs the import (you'll need to reference the path to the newly saved publishSettings file):
Import-AzurePublishSettingsFile
Now, check your subscription out:
Get-AzureSubscription
All done? Good. You can now run the Azure cmdlets against your subscription and control the VMs from the perspective of the virtual host, e.g. you can stop them, start them, interrogate them, provision more, etc.
Take some time to look at the Azure VM-related cmdlets:
Get-Command -Module Azure -Noun *vm*
Onwards...
For this post, I've provisioned a test Active Directory forest in Azure, with two DCs and two member servers, using this handy script:
Build an Active Directory Forest in Windows Azure
https://gallery.technet.microsoft.com/scriptcenter/Build-AD-Forest-in-Windows-3118c100
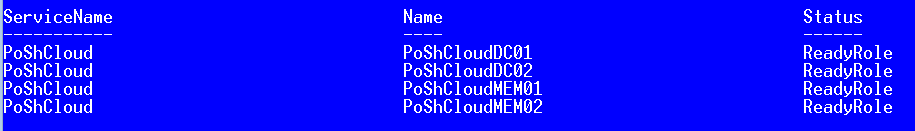
Now, if I run Get-AzureVM I have some infrastructure to manage.
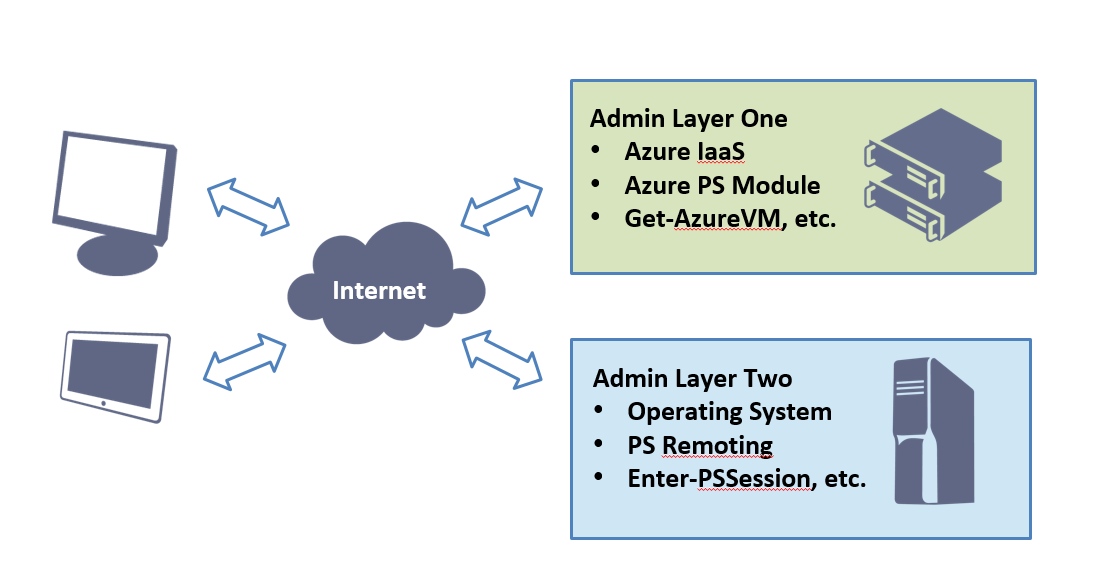
I consider the above output to be from the first administrative layer, i.e. the management of Azure IaaS.
What I conceptualise as the second administrative layer is where it gets even more interesting: I want to manage my Active Directory forest and the operating systems of my servers using the PowerShell console on my laptop. Over to PS Remoting...
If I want to enable seamless PS Remoting connectivity to the VMs in my new cloud service, here are the one-off steps I need to follow:
- Obtain the thumbprint of the default WinRM certificate from a VM
- Use the thumbprint to export the correct Azure certificate to file
- Import this certifcate to my localmachine\root certificate store
Once done it's just a case of connecting to the appropriate URI with the right credentials and the PS Remoting method of your choice.
The detail...
Obtain the thumbprint of the default WinRM certificate from a VM
As there may be other certificates associated with this cloud service, we get the default WinRM cetficate thumbprint from a VM to use in the next step.
$WinRMCert = (Get-AzureVM -ServiceName PoShCloud -Name PoShCloudDC01).VM.DefaultWinRMCertificateThumbprint
Use the thumbprint to export the correct Azure certificate to file
The thumbprint obtained in the previous step is used to identify and export the appropriate management certificate.
(Get-AzureCertificate -ServiceName PoShCloud -Thumbprint $WinRMCert -ThumbprintAlgorithm sha1).Data | Out-File ".\PoShCloud.cer"
Import this certifcate to the localmachine\root certificate store
Now I add this certificate to my laptop's Trusted Root Certificate Authorities store. I now trust each of the WinRMHTTPs endpoints for the cloud service.
Import-Certificate -FilePath ".\PoShCloud.cer" -CertStoreLocation "Cert:\localmachine\root"
With the certificate imported let's look at my connection options. To establish a session with a particular VM I need its WinRM URI and some credentials:
$WinRmUri = Get-AzureWinRMUri -ServiceName PoShCloud -Name PoShCloudDC01
$Creds = Get-Credential
Now, the magic...
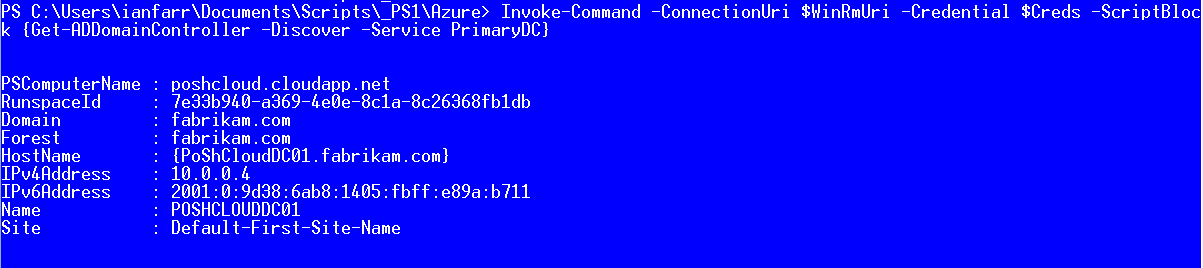
Invoke-Command -ConnectionUri $WinRmUri -Credential $Creds -ScriptBlock {Get-ADDomainController -Discover -Service PrimaryDC}
Or, I could establish and enter a remote session...
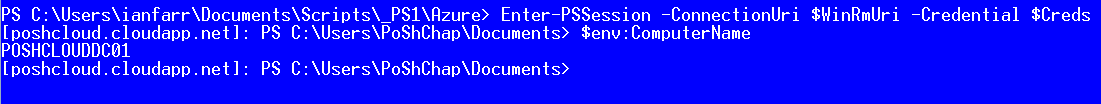
Enter-PSSession -ConnectionUri $WinRmUri -Credential $Creds
You get the idea...
Why did I mention dystopian novels? Well, I've just finished the following book and if you like this particular genre of fiction, it's definitely one to read...
We by Yevgeny Zamyatin