Security Focus: Find User Accounts Configured for DES Encryption
Once more, with feeling: extended support for Windows Server 2003 ends on July 14, 2015...
Hopefully, you've already upgraded your domain controllers to at least Windows Server 2008 R2. If you haven't, there are security enhancements to be aware of. Here's more information:
W2K3 to W2K8 and W2K8R2 Active Directory Upgrade Considerations
One of those enhancements is the disabling of DES encryption for Kerberos authentication. If you have user accounts, most likely service accounts, configured to just use DES there'll be authentication 'trouble at mill'!
How do you check for these accounts?
Get-ADUser -Filter {UserAccountControl -band 0x200000}
That was easy!
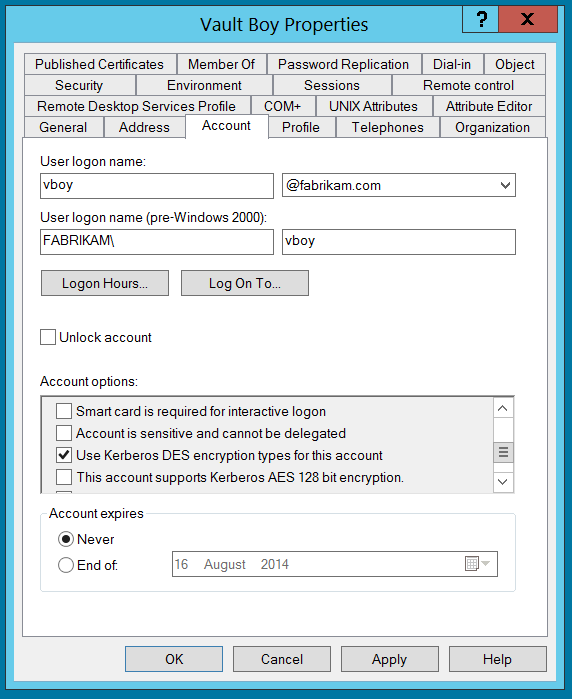
User Accounts have different options that can be set to control security settings. In Active Directory Users and Computers most of these options can be found in the 'Account' tab of the user object dialogue box, under 'Account options' :
In the above window, the user is set to use DES encryption. This setting is stored as part of a binary mask in the 'UserAccountControl' attribute of the user object. In the binary mask, each positional bit represents a different possible user account option that can be switched on or switched off. Like a light switch - when switched on, the option is active. These settings can be queried using PowerShell's 'binary And' ( -band) operator. The hexadecimal setting for DES encryption is 0x200000 and we use -band to check that it is present (switched on) in the binary mask.
Here are other values you could check for with the aid of a filter and Get-ADUser:
| Property Flag | Value in Hexadecimal | Value in Decimal |
| SCRIPT | 0x0001 | 1 |
| ACCOUNTDISABLE | 0x0002 | 2 |
| HOMEDIR_REQUIRED | 0x0008 | 8 |
| LOCKOUT | 0x0010 | 16 |
| PASSWD_NOTREQD | 0x0020 | 32 |
| PASSWD_CANT_CHANGE | 0x0040 | 64 |
| ENCRYPTED_TEXT_PWD_ALLOWED | 0x0080 | 128 |
| TEMP_DUPLICATE_ACCOUNT | 0x0100 | 256 |
| NORMAL_ACCOUNT | 0x0200 | 512 |
| INTERDOMAIN_TRUST_ACCOUNT | 0x0800 | 2048 |
| WORKSTATION_TRUST_ACCOUNT | 0x1000 | 4096 |
| SERVER_TRUST_ACCOUNT | 0x2000 | 8192 |
| DONT_EXPIRE_PASSWORD | 0x10000 | 65536 |
| MNS_LOGON_ACCOUNT | 0x20000 | 131072 |
| SMARTCARD_REQUIRED | 0x40000 | 262144 |
| TRUSTED_FOR_DELEGATION | 0x80000 | 524288 |
| NOT_DELEGATED | 0x100000 | 1048576 |
| USE_DES_KEY_ONLY | 0x200000 | 2097152 |
| DONT_REQ_PREAUTH | 0x400000 | 4194304 |
| PASSWORD_EXPIRED | 0x800000 | 8388608 |
| TRUSTED_TO_AUTH_FOR_DELEGATION | 0x1000000 | 16777216 |
| PARTIAL_SECRETS_ACCOUNT | 0x04000000 | 67108864 |
You're quite at liberty to combine them. This one tests for users who have the following set: 'Password never expires', 'Store password using reversible encryption' and 'Use Kerberos DES encryption types for this account'.
$COMBINED_VALUE = 0x10000 + 0x0080 + 0x200000
Get-ADUser -Filter {UserAccountControl -band $COMBINED_VALUE}
One would hope that this query never returns objects!
TTFN!