Part 4: Managing Local Administrator Passwords
Overview
This is Part 4 of a multi-part series on managing local admin passwords. In this part I will discuss how to update the password of a local user account using PowerShell. In case you missed it:
Here is Part 1 - Overview
Here is Part 2 - Random Password Generation
Here is Part 3 - Secure Active Directory Attribute Update
If you want to skip straight to the script you can copy it from this post directly, or you can download the script which is attached to this post as a text file.
The Problem
To manage the passwords for an enterprise environment, any comprehensive local admin password management solution must include a way to programmatically update the password of the local administrator account with a new password when needed..
The Solution
The following function will update the password for any account specified in $AccountName with the value of the password specified in $Password
#==================================================================================
# Set Local Admin Password
#==================================================================================
function fnSetAdminPassword
{param([string]$AccountName,[string]$Password)
try{
#Connects to local admin account and sets password
([ADSI]$Admin=”WinNT://$env:COMPUTERNAME/$AccountName”); $Admin.SetPassword("$Password")
#Log Output
#fnLog -LogPath $LogDir -LogFileName $LogFileName -Data "INFO: Successfully Updated Local Admin password"
#Return Code
Return "SUCCESS"
}
catch{
#Log Output
#fnLog -LogPath $LogDir -LogFileName $LogFileName -Data "ERROR: Unable to set local admin password"
#Return Code
Return "ERROR"
}
}
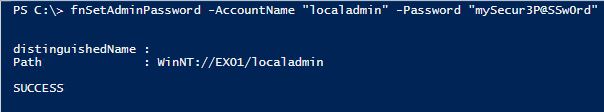
Below is a screenshot of the preceding function updating a local account called localadmin to a password of mySecur3P@SSw0rd on a machine called EX01.
The keen observer may have noticed that I commented out the fnLog function in the example script above. The function above is a part of a larger local administrator password management solution which I will continue to reveal in the next part of this series. What you have so far is a configurable random password generator which can be integrated into pretty much any random password script, a cryptographically random character generator which can also be used for many different purposes, a means to securely transmit the password to Active Directory using Kerberos to secure the data in transit, and a programmatic way to update any local account on a workstation or server with the password of your choosing.
Limitations
The account running the script must have the rights needed to update the password for the target account. Additionally, the target account name must exist for the update to succeed.
Still to Come
The upcoming parts in this series will explain how to do the following:
- Write a log file that logs the success and failure of each function
- Create a confidential attribute to store the local admin password
- Create fnMain to control the order in which all of the functions are called
- Create a XAML based secure password viewer to retrieve the local admin password
Each portion of the solution is modularized using functions which allows the IT administrator to make use of all or just parts of the solution and allows the IT administrator to easily integrate any portion they wish into a larger script or even a different solution entirely. So stay tuned as Part 5 discusses how to log the success or failure of each function using PowerShell.