Renew Web Server (SSL) Certificates Automatically
Working with Internet Information Services (IIS) certificates can be a bit challenging especially during renewal time. Most organizations do not track Web SSL certificates which in turn might expire and cause an unplanned outage. Those who track this information on the other hand, have to make sure certificate are renewed before their expiration period or find ways to notify the application owners of their certification expiration beforehand.
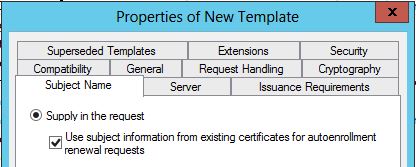
Windows Server 2008 R2 and Windows Server 2012 addresses this issue through Auto-enrollment and Certificate Templates. The Certificate Template’s design includes a new option Use subject information from existing certificates for autorenewal requests. This option allows the certificate to renew automatically, including any information in the Subject Name, or any additional information in Subject Alternate Names fields. This option is available for client certificates installed on computers running Windows 7 or Windows Server 2008 R2 and later.
The Use subject information from existing certificates for autoenrollment renewal requests option causes the certificate enrollment client to read subject name and subject alternative name information from an existing computer certificate based on the same
certificate template when creating renewal requests automatically or using the Certificates snap-in. This applies to computer certificates that are expired, revoked, or within their renewal period.
The Autoenrollment Group Policy has to be enabled for this feature to work. This feature will also work on certificates issued prior to enabling it. For example, an administrator can change the original template’s settings to include Use subject information from existing certificates for autoenrollment renewal updates after a certificate is issued because the scope of enrollment in a Microsoft PKI is the template. Autoenrollment Group Policy and this feature will allow the certificate to renew in the future without any administrative intervention when the certificate is within the renewal validity period time specified by the template – typically within 20% or less of the certificate’s validity period.
Amer F Kamal
Senior Premier Field Engineer