Take Control Over AD Permissions and the AD ACL Scanner Tool
What is the state of your delegation?
Have you a documented and recent report over the permissions in your Active Directory?
Have you granted permissions on the relevant OU's in the past and left it like this ever since??
Maybe it’s time to take a look again to see what’s actually delegated in Active Directory?
Things you probably find when re-visiting the permissions:
- Permissions given to users or groups that does not exist anymore.
- Permissions set to high up in the OU structure so users have the possibility to create/delete/modify Active Directory objects in the wrong places.
- The permissions grant the user more than needed e.g. Helpdesk is supposed to reset passwords on user’s accounts in the defined OU but can create\delete any type of objects.
- Same set of permissions delegated to two groups. Usually only one group is needed for one set of permissions.
- Permissions granted to users or groups that is not needed anymore. This can happen when enabling a project to create objects for a limited period of time or if there were a transition between out-sourcing partners.
What to do?
Every Active Directory should have a documented delegation model that includes the permissions set for the data in Active Directory.
I'm not saying you should type down every single permission on every object, but the permissions that is needed for you organization to be able to perform their given tasks.
Here's a simple example of how you could document Helpdesk's permissions in AD:
| Group | Permissions | OU |
| Helpdesk | Reset Passwords | OU=Users,OU=Corp,DC=Contoso,DC=Com |
| Helpdesk | Create/Modify Groups | OU=Groups,OU=Corp,DC=Contoso,DC=Com |
To verify that the permissions in Active Directory is reflecting the need of you organization you have to go through every OU in your Active Directory where permissions is modified.
It's usually a quite daunting task to click your way through the directory tree to get control over the permissions. For every OU or any object for that matter there are at least 4 clicks to reach the Advanced Security Settings tab, which is often the required view, and if you got a large OU structure that could take a while.
To simplify the work of creating and documenting the delegation model in Active Directory I have written a tool in PowerShell with a GUI.
This tool creates reports of the access control list for all of your Active Directory objects. With these reports you can see what/where and when permissions have been set.
To run the script you need at least PowerShell 2.0 and Windows 7/Windows Server 2008, (Windows Server 2003 with Limited functionality).
Enabled unsigned scripting:
Set-ExecutionPolicy Unrestricted
If you are not local admin and cannot set it on your machine you can set it for your profile:
Set-ExecutionPolicy Unrestricted -Scope CurrentUser
You do not need Powershell Module for Active Directory.
To create a report for an OU.
- Click Connect and the tool will connect to your domain.
- The Domain Node will be populated in the large tree view box below and you can click your way to the OU.
- When the OU is selected click Run Scan and you will get a HTML report of the permissions.
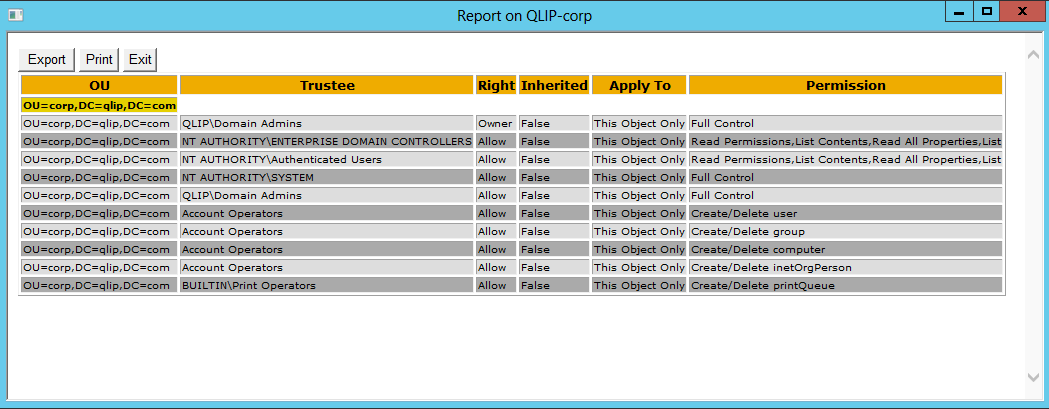
This is an example of a report:
By default you will only get the selected OU, but if you like to list all sub OU's you can clear the One Level check box. Be aware that it can take a long time to though a large OU structure.
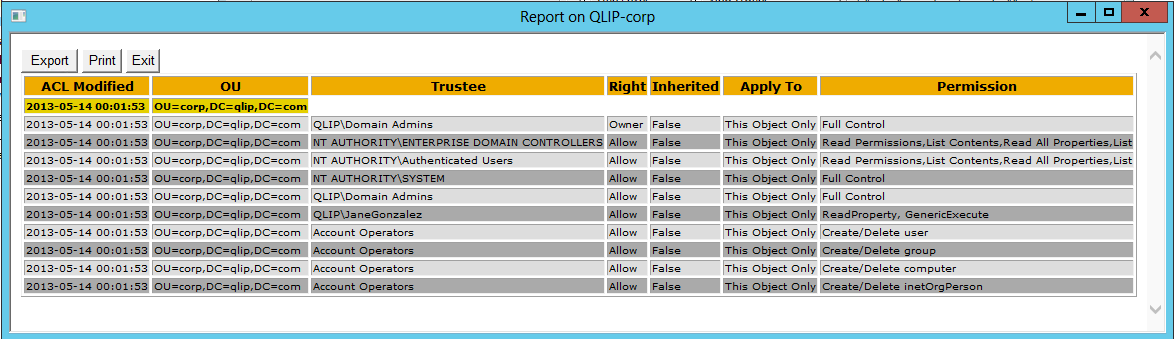
To get the date when the permissions where modified check the Replication Metadata check box. This will add a column to the report with the latest change of the permissions on each object in the report.
This is an example of a report with the date when the access control list was modified.
To browse all objects, click All Objects in the Browse Options box. This is necessary when you would like to get the permissions on another object like a user for example. Then you also have to select All Objects in the Report Objects box too.
If you like to create a report of the whole domain I strongly suggest you select CSV file in the Output Options since it will take a long time to go through all OUs and create a HTML table for it. If you select CSV file it will be much faster and you can convert it to a HTML report afterwards in the Additional Options. You can even use it for comparison.
The Power of AD ACL Scanner
- Comparing
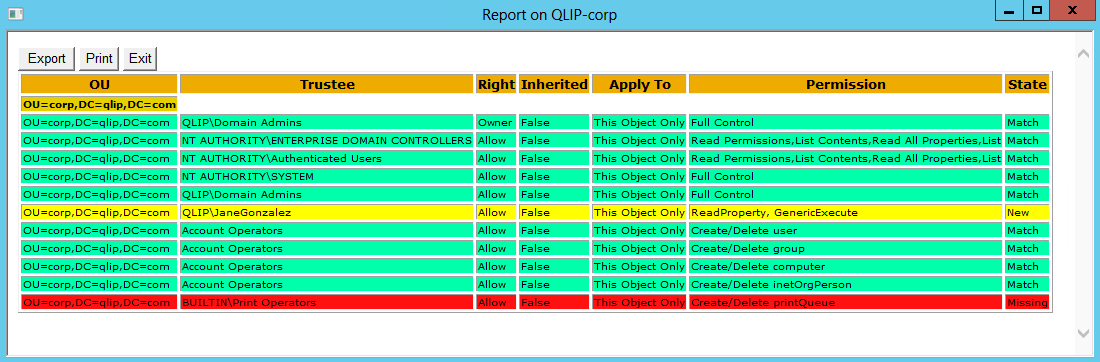
The cool thing with AD ACL Scanner is that you can compare the current state with a previous result. If you select to create a CSV file of the report you can use that to compare the current state with this file and you will get a report of what is missing or what is added.
This is an example of a comparison report:
- Filtering
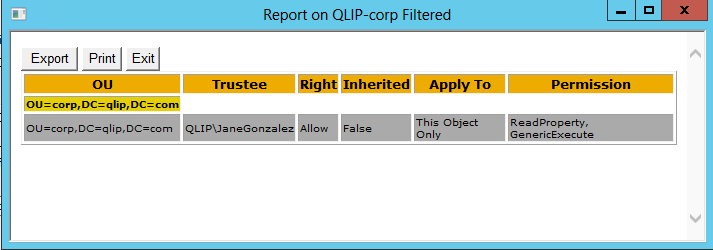
Another nice feature is the filtering feature.
- You can filter on Allow or Deny permissions.
- You can filter on object types, like user or computer.
- You can filter on Trustee, this is a free text field where you can type any kind of name you are looking for. For example: QLIP\JaneGonzalez.
Here's an example of a report with filtering:
Go ahead and download AD ACL Scanner script from Codeplex: https://github.com/canix1/ADACLScanner
Go ahead and explore permissions in AD!
I encourage you to get to know your permissions in AD and starts to document it.