Step-by-step walkthrough: Installing an Operations Manager 2012 Gateway
Step-by-step walkthrough: installing an Operations Manager 2012 Gateway Server
To make this document, I installed 3 test servers; the evaluation image of Windows Server 2008 R2 can be downloaded from the Microsoft site here: https://technet.microsoft.com/en-us/evalcenter/dd459137.aspx
This installation was done on a generation 1 Core i7 portable with 1 SSD drive and 8GB of memory. The ISO image and the 3 Hyper-V VMs are on that 1 SSD drive. All at the same time installing, while opening Microsoft OneNote and Microsoft Word and creating this document – it’s not slow at all!
Windows 8 is great!!! ![]()
And so is OneNote – Windows+S gives you a really nice integrated screenshotting tool!
The setup will be as follows:
- OM12DC: Active Directory, including AD CS (Certificate Services) to generate the certificates for the gateway server. AD CS will be installed as an online enterprise root CA.
- OM12MS: management server, including Operations Manager Reporting, the Operational database and the Data Warehouse database
- OM12GW: a separate server in a workgroup. This one is the reason we need to have AD CS.
This document is meant to further clarify the TechNet article https://technet.microsoft.com/en-us/library/hh456447.aspx Deploying a gateway server which links to a further explanation https://technet.microsoft.com/en-us/library/hh212810.aspx Authentication and Data Encryption for Windows Computers
More about certificates can also be found here:
Win2008 Enterprise CA: https://technet.microsoft.com/en-us/library/dd362553.aspx
Win2008 Standalone CA: https://technet.microsoft.com/en-us/library/dd362655.aspx
After the Windows Update process is finished, you can start installing Active Directory on the DC.
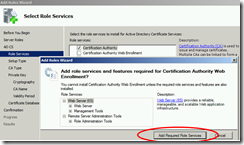
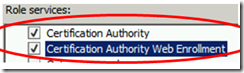
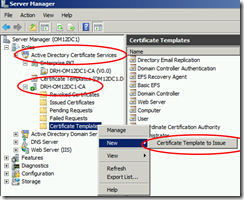
When you have installed and configured AD DS, add the AD CS role + the web site to request certificates.
And the rest is NNF (Next-Next-Finish).
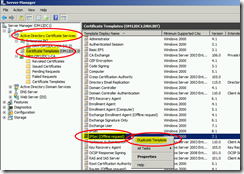
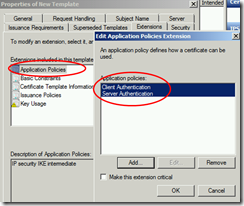
Remove PKI and add Client / Server Authentication to Application Policies
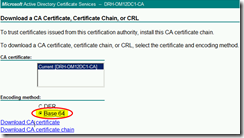
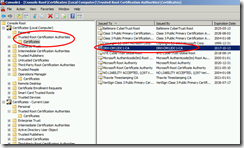
From the GW server, the one that is not in the domain, you don’t trust the Enterprise CA by default.
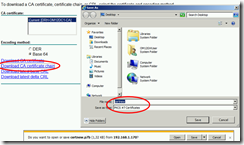
That’s why you first have to get and install the Root CA certificate from the AD CS.
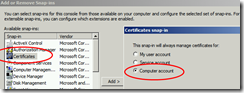
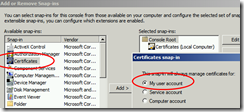
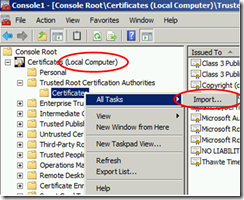
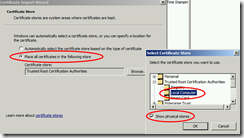
Add both My user account and Computer account – you’ll need both anyway
The certificate from the Root CA needs to be added in this list.
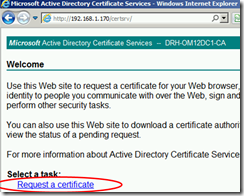
Open a web browser on the gateway server, and go to the CA Web service: https://OM12DC1/certsrv
Add the certsrv website to the Trusted Sites by going to internet options and under security choose Trusted Sites, and click on Sites to add this site.
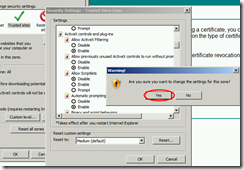
Since the certsrv website uses ActiveX, change the security settings of Trusted Sites so that ActiveX is allowed.
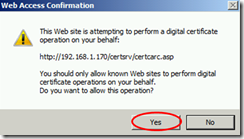
Here we need to request the CA chain
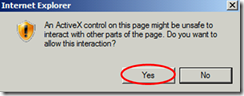
If you don’t see these 2 popups, you need to enable ActiveX first.
The certificate is in the list now, meaning our workgroup gateway server will trust certificates issued by the Enterprise Root CA.
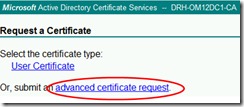
Now we need to request a certificate for our gateway server
Advanced request
Create and submit
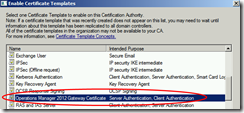
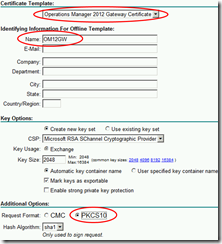
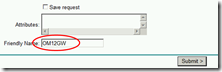
Select the template that was created earlier, and fill in the Name and Friendly Name fields with the FQDN of your gateway server.
Since mine is in a workgroup, the NetBIOS name is sufficient.
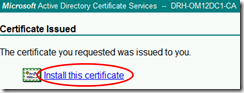
And now the certificate is generated and we can install it
Done ![]()
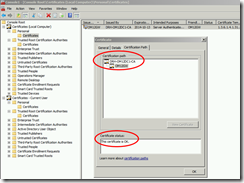
But wait a minute… Installed, where???
We need to authenticate computers, and the certificate is imported in the personal certificate store.
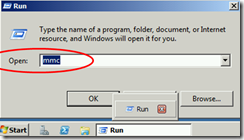
So we need to open the Certificates MMC and copy the certificate from the personal store to the local computer store.
The certificate is now installed and you can verify everything is installed correctly by opening the certificate and checking if the certification path is ok.
On the Management Server, we also need to install a certificate. Since we have an Enterprise Root CA, integrated with AD, the root CA certificate is already trusted by our MS who is a domain member.
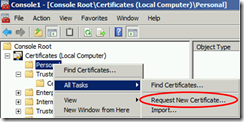
We can also request certificates in another way: we can request a new certificate from our CA directly from the MMC.
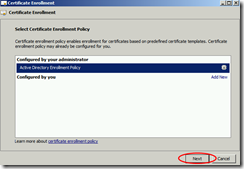
Click next
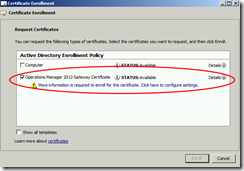
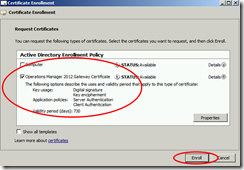
Select the certificate that we’ve created earlier
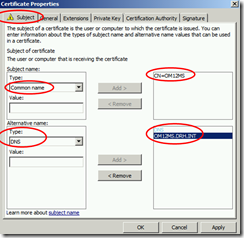
The extra information needed is the Common Name in the first box (OM12MS) and the FQDN in the bottom box with DNS.
And click Enroll to finish this
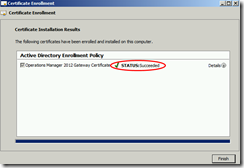
NOW we’re done ![]()
Now we have to approve the gateway to be able to communicate with the management server.
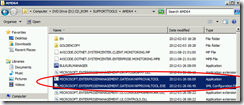
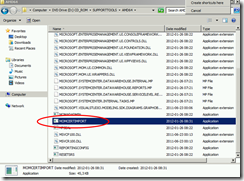
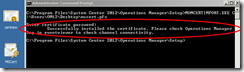
Copy the Microsoft.EnterpriseManagement.GatewayApprovalTool.exe and the corresponding Microsoft.EnterpriseManagement.GatewayApprovalTool.exe.CONFIG file from the support tools directory on your installation media to the installation path of your OpsMgr installation, in my case that’s C:\Program Files\System Center 2012\Operations Manager\Setup
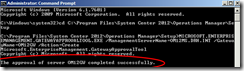
1. Approve the gateway server: At the command prompt, run Microsoft.EnterpriseManagement.gatewayApprovalTool.exe /ManagementServerName=<managementserverFQDN> /GatewayName=<GatewayFQDN> /Action=Create
If the approval is successful, you will see The approval of server <GatewayFQDN> completed successfully.
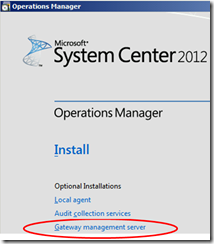
Now you can install the gateway software by clicking the Gateway Management Server link in the setup splash screen
We did this, so we can continue the setup
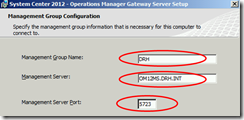
Give the management group name - this can be found in the title bar of the console on the management server - and the management server name
The port number can be changed if desired. Only this 1 port needs to be open on the firewall, that’s the big advantage of using a gateway server!
Copy the MOMCertImport.exe tool to the gateway server, into the gateway installation path.
In my case, this is C:\Program Files\System Center Operations Manager\Gateway
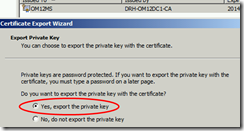
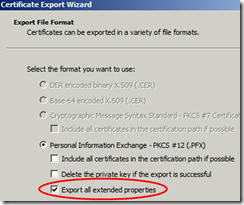
Export
You’ll get a message that the action succeeded, and you can check progress in the Operations Manager event log.
Do the same for the gateway server:
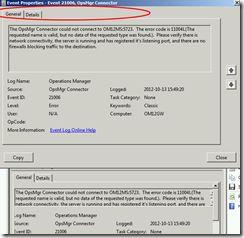
Troubleshooting:
If you get event 21006, make sure the firewalls on the gateway and/or on the management server are not blocking communication
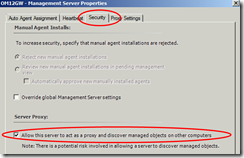
Don‘t forget to enable Agent Proxy for the gateway, as this one will act as a proxy for other systems connecting through the gateway server!
To check if it’s working, go to the Operations Manager Console – you should see something similar to this!! ![]()
HTH and a big thank you to my colleague Ingo for double-checking the certificate part!
/Danny