EO ATP - Considerations, Reports, Demonstrations
Hello folks!
The new truly safety and anti-virus service was announced in previous year called Exchange Online Advanced Threat Protection. The service is a set of two modern, advanced, secure features.
- Safe attachments helps to protect against zero day exploits in email attachments by blocking messages or attachments that could be malicious.
- Safe Links provides real-time, time-of-click protection against phishing and malicious web sites by warning users when they click a link in email that has been determined to be unsafe.
Implementation of the service is ridiculous easy and is published on TechNet articles here Set up a safe links policy in ATP and here Set up a safe attachments policy in ATP
By reading this post you will find out:
- How to check emails go through Safe Attachment module and defense of Zero Day Attack does work;
- How to be confident that feature Safe Link works successfully;
- How to set up exclusions to disable Safe Attachments or Safe Links based on flexible conditions;
- Considerations regarding Dynamic Delivery in Safe Attachments;
- How to make a live demo of Safe Attachments or Safe Links
Let's talk about ways of checking Safe Attachment. There are three distinguished ways.
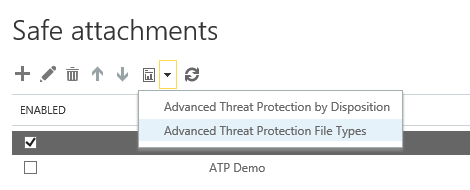
Visual reports. You can find them in Safe Attachment policy setup page. They give you good visual overview and be meaningful to show working results to BDM, IT Managers, CIOs or IT Security staff. You need to push Report on a page of policy creation and chose it between "by Disposition" or "File Types".
After that you just need to choose time frame and extended filters on opened window to get the graph:
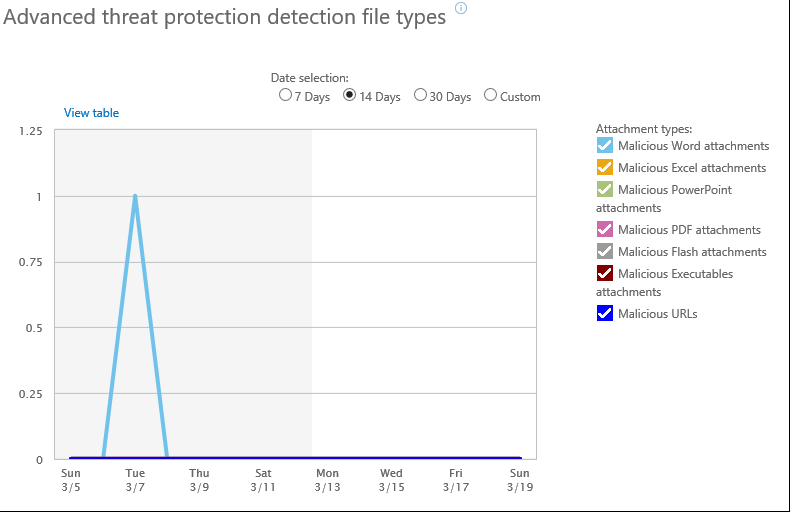
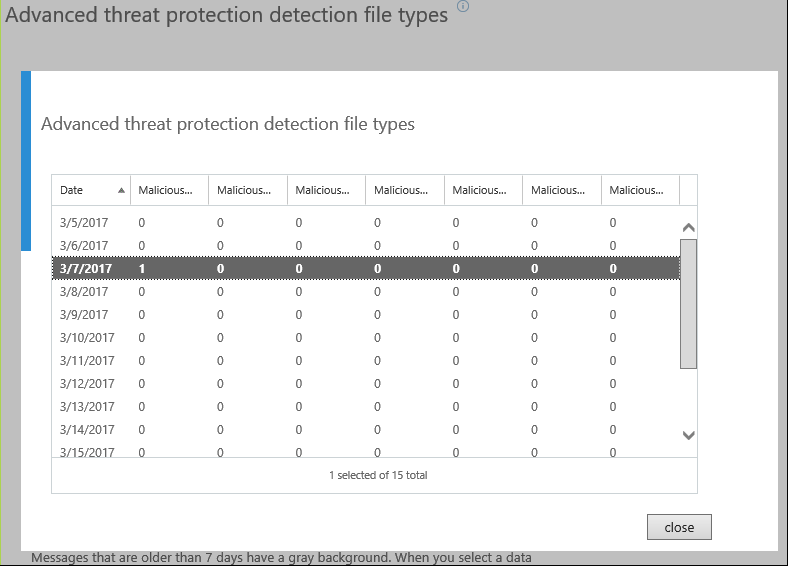
As the need required you may get the report in table view by clicking-on "View table" on upper-left corner.
There are two purely (strictly) technical ways of checking Safe Attachments. They will be useful very much for IT engineers to control of delivery/submission and the most important delay of delivery.
Message Trace logs.
It’s hard to beat time-honored Message Trace logs. If only because the logs are available on Exchange Online as well as Exchange Server on-premise. You need to go in Office 365 Admin Center, then Exchange Admin center, Mail flow and Message Trace lately.
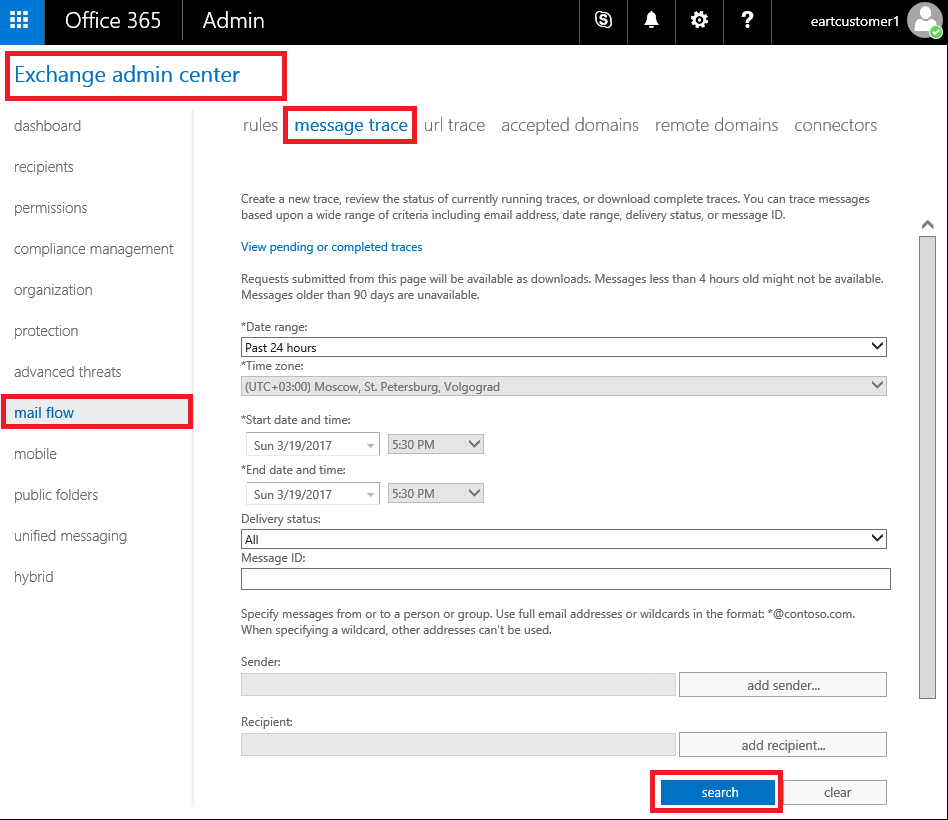
It's mandatory to set time-frame, if you need sender and/or recipients. Be aware, if you need to get reports older than 7 days you should set sender or recipients as well as days.
Click Search button. We get detailed information about routing of the mails throughout EOP and ExO.
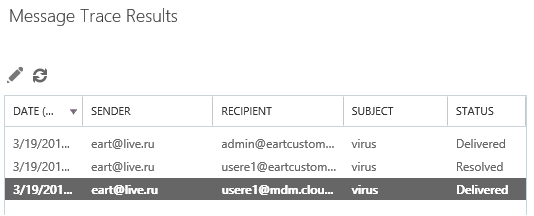
We are concerned the row with Delivered Status, double click on it. We get curious set of events happened with the particular mail. I will emphasize on two pivotal events.
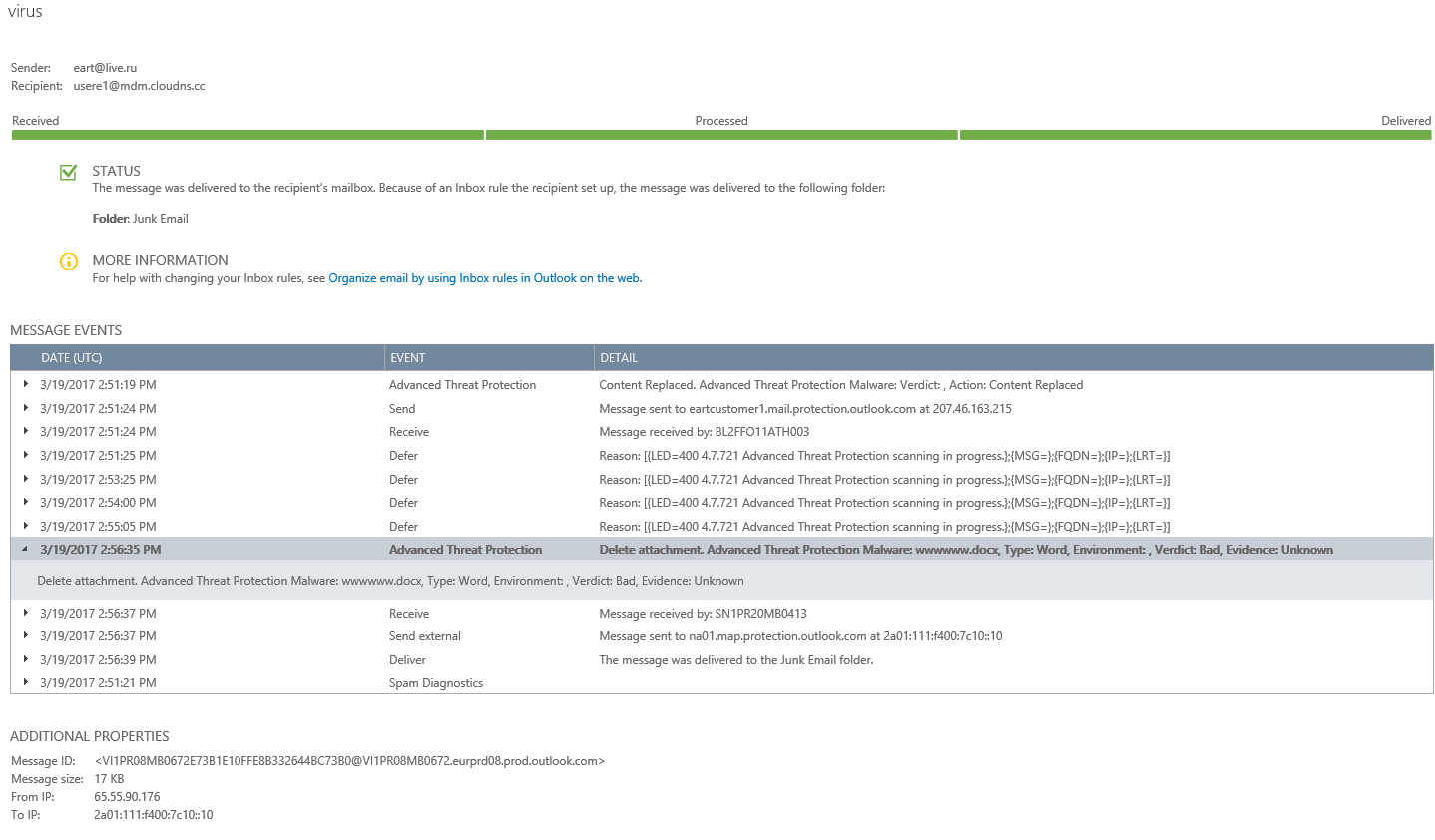
Immediate Advanced Threat Protection event holds that Attachment was deleted due to virus positive verdict. Repeated Defer events tell us that Safe Attachment process informs Transport Service about his work. It fairly points out on his work.
Basically, these set of event logs in Message Trace tell us about work and actions of Safe Attachment.
Third way is analysis of mail's headers
If Safe Attachment did his job then you may expect the header
X-MS-Exchange-Organization-SafeAttachmentProcessing
Pay your attention on the header X-MS-Exchange-Transport-EndToEndLatency. It tells us how much time did it take to deliver the email throughout EOP/ATP and ExO to mailbox.
It will be longer for mails penetrated through Safe Attachments (SA).
Just look over:
X-MS-Exchange-Transport-EndToEndLatency: 00:02:12.9456274 (mail with checked SA)
X-MS-Exchange-Transport-EndToEndLatency: 00:00:04.1022305 (mail w/o checking SA)
Circumstantially, larger value of the header tells us about SA working.
Now let's look on approach of Safe Links control
There is URL Trace Report.
It is next to Message Trace. You need to go in Office 365 Admin Center, then Exchange Admin center, Mail flow and URL Trace Log lately.
It allows you to see full or filtered list of events. In the particular example I want to know Has userE1 clicked on spamlink.contoso.com during the latest 24 hours. 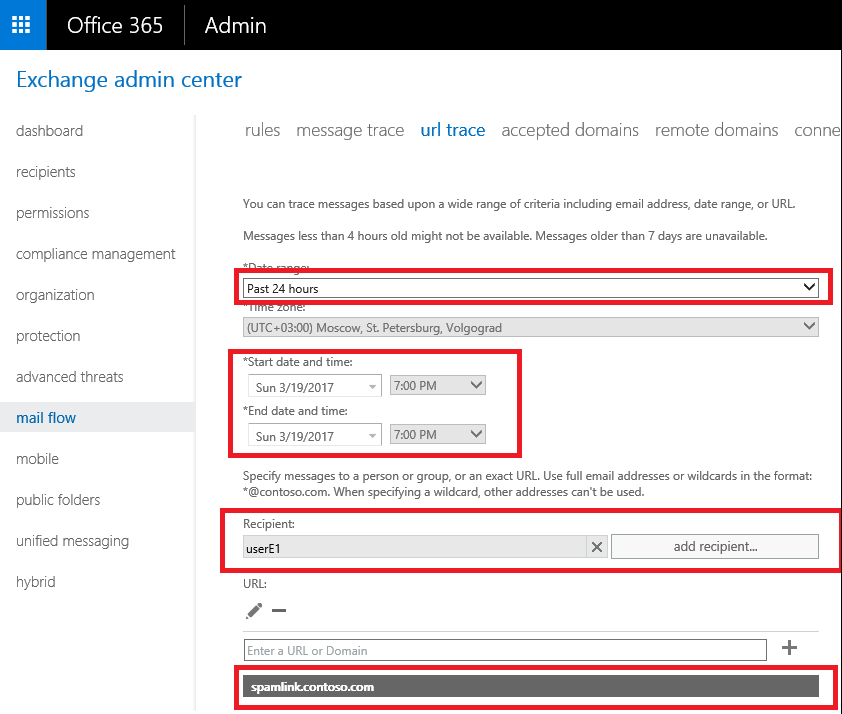
In fine I got the accurate list of the registered and filtered events.
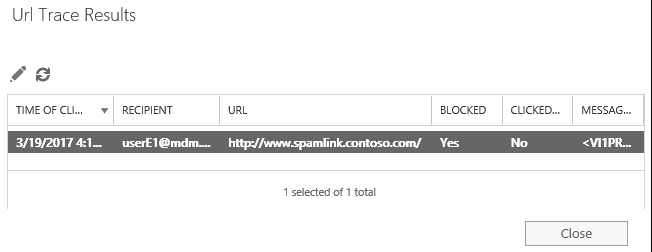
Be aware the report shows when clicks were happened but does not show the events regarding procedure of changing link s by Safe Links. Apparently you just need to look over the link and where it routes. It looks like
First part may be diverse based on DC of EOP location: NA, EMEA, APAC etc.
How to disable Safe Attachment/Safe links w/o disabling the policy?
There are numbers of scenarios when it may require to disable Safe Links/Attach,ents. For instance, there is no need to check email from scanners, LOB Applications or from trusted partners etc. You should use
Exchange Transport Rules (ETRs).
- Goto the Exchange Admin Center.
- Select the mail flow link in the left nav
- Select rules from the top nav
- Select the + icon to add a new rule
- From the pull down menu select create a new rule…
- At the bottom of the new rule dialog, select More Options… to expand the dialog to all option.
- Under Apply this rule if… chose The sender is located… and then Inside the organization
- Under Do the following… chose Modify the message properties… and set message header

- Click the Enter text… link to the right of Set the message header.
- To skip Safe Attachments enter:
- X-MS-Exchange-Organization-SkipSafeAttachmentProcessing
- To skip Safe Links enter:
- X-MS-Exchange-Organization-SkipSafeLinksProcessing
- Then click Enter text… next to to the value
- And enter 1 and click OK.
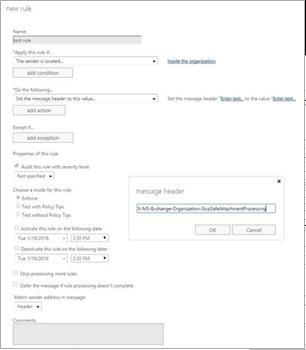
Then EOP will skip corresponding checking if see the headers, even if policy is enabled.
It's worthwhile to refer the built-in Safe Link exclusions filter.
If you do not need to check links for internal portals It's possible to set exclusions for predefined links by template. You can find it on a capture below.
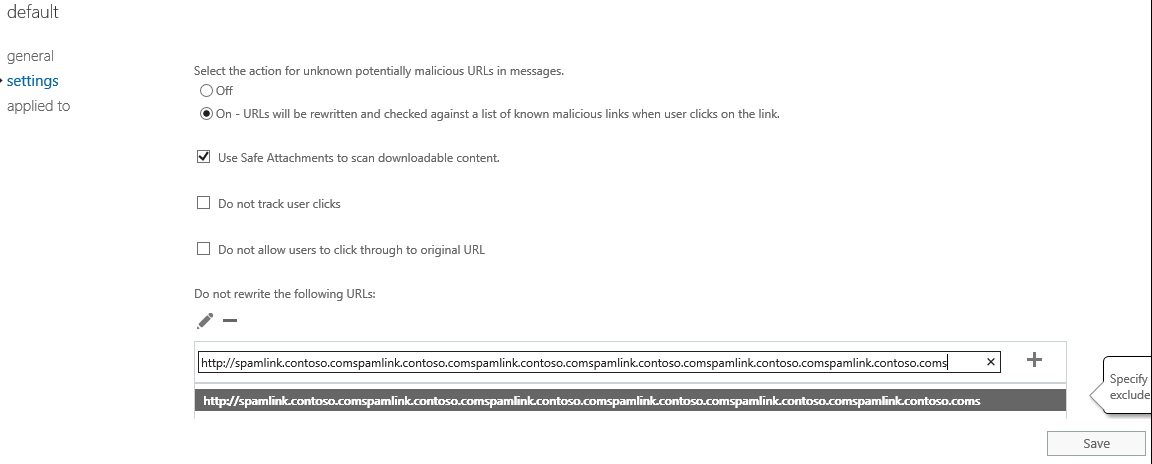
Be aware, there is a limitation of interface, it’s impossible to add link longer than 128 characters. Obviously, it's more than enough for vast of majority cases, if not use ETRs.
Dynamic delivery consideration.
Since introducing Safe Attachments, we have greatly reduced the time it takes to scan emails containing attachments. While any malware solution requires some small amount time to scan suspicious attachments, Advanced Threat Protection enables you to remain productive during this scan time. Now, with Dynamic Delivery, recipients can read and respond to the email while the attachment is being scanned. Dynamic Delivery delivers emails to the recipient’s inbox along with a “placeholder” attachment notifying the user that the real attachment is being scanned—all with minimal lag time.
If a user clicks the placeholder attachment, they see a message showing the progress of the scan. If the attachment is harmless, it seamlessly re-attaches to the email so the user can access it. If it is malicious, Office 365 Advanced Threat Protection will filter out the attachment.
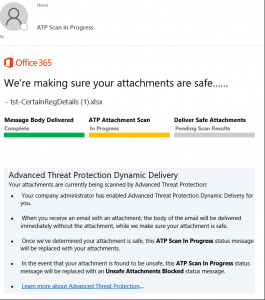
Just be aware it works with Exchange Online hosted mailboxes. If mailbox is hosted on premise (any premise Exchange, 3rd-party) than "Replace" method will be applied.
ATP Demonstration.
Here I'm going to cover "How to Demo of ATP" as I promised in the beginning.
When it comes to classic EOP, You need to create specific EICAR.txt file to demonstrate A/V engine working and just send file via mail to O365 mailbox. You will see blocking actions by EOP under the emails. How to do it you can read in the article Configure anti-malware policies.
To show Safe Link in actions Microsoft has prepared two specific links. Just send an email to Office 365 mailbox with these links: https://www.spamlink.contoso.com/ and/or https://contoso.com/maliciousfile.pdf to be confident that the policy works correctly.
Detailed steps you will find in the articles Set up a safe links policy in ATP and Advanced Threat Protection for your Office 365 dev/test environment
I used these links to make screenshots of reports and positive events in my article.
To demo Safe Attachments we need to create the new Virus. It's very important the virus should be unknown for A/V engines. Indeed, it is not trivial task. I did not heard about public tools to demo Safe Attachment. If you are the MAPS, Silver or Gold partner and you have a real customer who intends to buy ATP and is asking you to provide real demo, come to Partner Technical Service and we will discuss how we can help you. https://aka.ms/mysupport
Folks, I really hope it was worthwhile to read the article and you found something useful. I will really appreciate any feedback, comments.
Good luck!