Enhancements to Exchange 2013 integration with AD RMS
Summary: Jaroslav Zikmund, one of our Czech Republic-based Microsoft Premier Field Engineers who focuses on Messaging, provides us with some insights and details on enhancements in Exchange 2013 for protecting email via Active Directory Rights Management. Better safe than sorry! Enjoy.
 When it comes to utilizing Active Directory Rights Management Services (AD RMS) for protecting and limiting access to e-mail, Microsoft Exchange 2013 preserves the same functionality as Exchange 2010, and adds some exciting new and useful features.
When it comes to utilizing Active Directory Rights Management Services (AD RMS) for protecting and limiting access to e-mail, Microsoft Exchange 2013 preserves the same functionality as Exchange 2010, and adds some exciting new and useful features.
Enhancements to Outlook Web Access
Access to RMS protected emails is available in Outlook Web Access (OWA) in similar ways as in Exchange 2010. The main enhancement from an AD RMS integration point of view is Offline mode.
OWA in Exchange 2013 now supports offline mode, which can be beneficial for users without full Outlook clients. If offline mode is enabled, the web browser will cache data in IndexDB on the local drive. Your browser has to support HTML5 to use this functionality. Currently Internet Explorer 10, Chrome or Safari should support this functionality (I’ve personally tested this with current versions of Chrome and IE10). As in the standard version of OWA, RMS emails are decrypted on the server side and then displayed in the OWA interface or downloaded to the indexDB. Messages are not encrypted in the DB, so some level of system encryption (BitLocker or EFS) is highly recommended.
When a client is offline without connectivity to the corporate network, an end user can read protected emails (rights are enforced by IE) but cannot protect new created emails (templates are not cached in the indexDB)
Note: in case you want to play with this functionality in your lab environment, be sure that your system is up to date, including the latest version of IE 10, as prior/beta versions can have problems with OWA or the Exchange Control Panel (ECP).
Transport Rule Updates
Transport rules has been extended in Exchange 2013 (check out a full list of what’s new in Transport Rules for Exchange 2013). The options to apply the AD RMS temple is still available as in previous versions. I would like to highlight two new conditions available in new version of Exchange. AD RMS templates can be applied based on source IP address of the client, and based on sensitivity of information in the emails. A full list of conditions are available in this article that discusses Transport Rule Predicates.
If you apply templates based on the source IP address, the IP is evaluated even when OWA or Outlook is used (in the case of an OWA user, the IP address is used and not the IP address of the server).
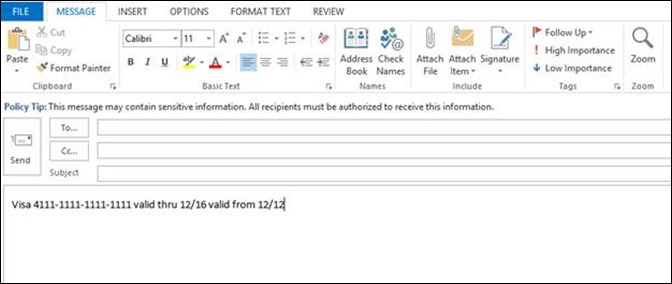
If you apply RMS templates based on the sensitivity of the information, you can choose from list of predefined sensitive information types including passport numbers, bank accounts, IP addresses or credit card numbers. If you specify credit card numbers, Exchange server will be able to detect credit card numbers based on format and checksum. For example, if you send 1111-1111-1111-1111 as credit card number, RMS templates will not be applied because this is not valid credit card number. If you send the same email with this credit card number 4111-1111-1111-1111, theRMS template will be applied because of the valid checksum.
New Features in Data Loss Prevention
A completely new feature in Exchange, Data Loss Prevention (DLP) consists of two parts:
- The first part works on the server level and is based on new set of transport rules which are able to enforce compliance requirements (keyword matches, regular expression evaluation, dictionary search and other technique).
- The second part is called Policy Tips and works only in Outlook 2013 Professional. Policy tips will inform end users that a message contains sensitive information and recipients must be authorized to receive it.
If one of the actions in the DLP policy is to apply an RMS template, the message will be sent from Outlook without protection and the template will be applied on the server level. If the client doesn’t support policy tips (e.g. older Outlook clients) the RMS template will by applied on the server level anyway. If the client is able to support policy tips, the tip will be displayed during the message composition.
How Data Loss Protection works in the background:
- When Outlook starts and a user clicks to the new email button for the first time, Outlook will connect to the externalurl defined in EWS virtual directory.
- Outlook downloads the policy definition files (PolicyNudgeClassficationDefinitions<GUID>.XML and PolicyNudgeRules<GUID>.XML) and stores the information locally in Users\<User>\Appdata\Local\Microsoft\Outlook
- Outlook makse an entry in the registry (HKEY_Current_User\Software\Microsoft\Office\15.0\Outlook\PolicyNudges\ LastDownloadTimePerAccount) that policy was downloaded
- A user types a message and the policy tip is displayed when the appropriate policy condition exists.
- The user sends the message
- The Transport Rule detects sensitive information and applies the AD RMS template
DLP Troubleshooting tips:
- Be sure that you have the correct version of Client (Outlook 2013 professional)
- Check that Externalurl is configured (internalurl is not enough)
- Try to delete the registry entry HKEY_Current_User\Software\Microsoft\Office\15.0\Outlook\PolicyNudges\ LastDownloadTimePerAccount and check to see if is recreated.
- Check presence XML in the profile
DLP Compared to Outlook Protection Rules
Outlook Protection Rules work in the same way as in Exchange 2010. More information on Outlook Protection Rules is available on the TechNet.
The main differences between DLP and Outlook protection rules:
- In DLP, a message is protected on the server; with Outlook protection rule a message is protected on the client.
- If the client doesn’t support Outlook Protection Rules the message will not be protected.
- If the client doesn’t support DLP rules, policy tips will not displayed, but the message is protected on the server
- DLP rules are able to check content of the message; Outlook Protection Rules are able to check only sender or recipient
Hope you found this helpful. Any and all comments are welcome.
Posted by Frank Battiston, MSPFE Editor.