How to Create Custom Recipient Management Groups Using Exchange 2010 RBAC
Article written by Matt Abraham, Premier Field Engineer.
My customer wanted to assign the "Recipient Management" group to their helpdesk staff, who are responsible for the creation and management of their Exchange mailboxes. However, they didn't want to give the "Delete" permissions to the helpdesk. This is simple to accomplish using Microsoft Exchange 2010 and RBAC (Resource Based Access Control)!
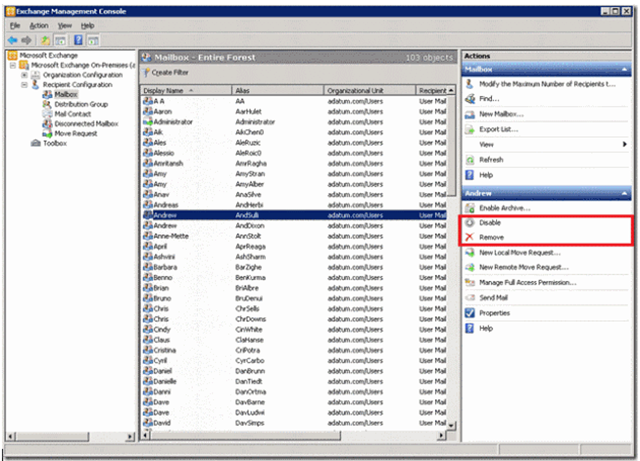
When the helpdesk uses the EMC (Exchange Management Console) with the default "Recipient Administrators" role group, they were able to delete user accounts and mailboxes.
This was unacceptable to my customer as they like to keep their historical mailboxes. We needed to limit the ability to disable and remove mailboxes, without impacting their ability to use the Exchange Management Console. We needed to create a custom Management Role Group which contains all the functionality of the “Recipient Administrators” group, but without the ability to delete mailboxes.
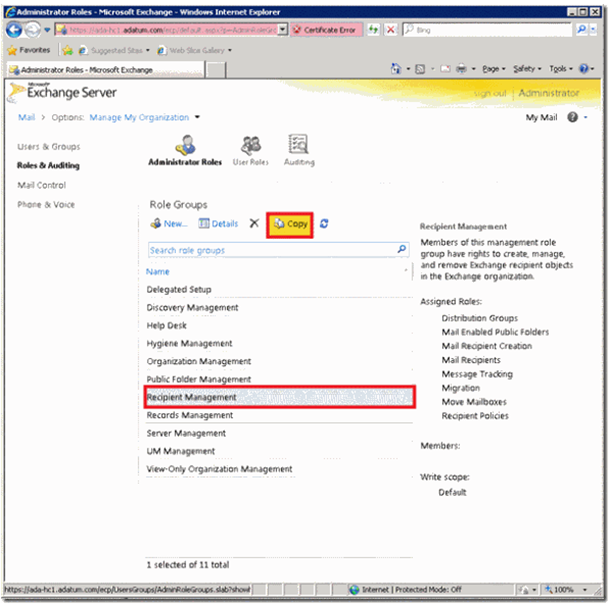
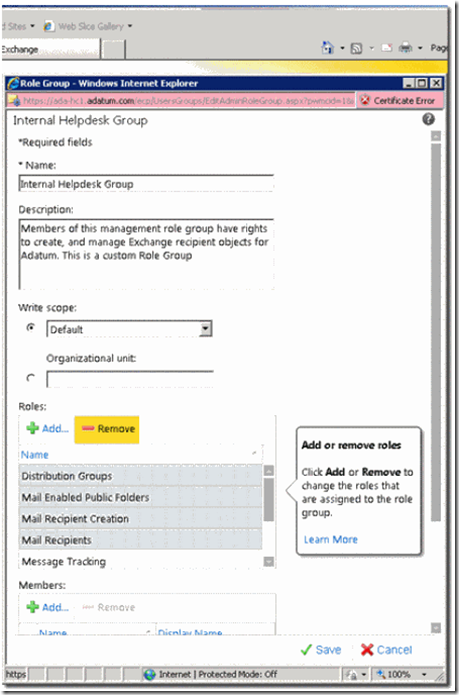
The first thing to do was to create a new Management Role Group. As I wanted to base this on the "Recipient Management" role group, I started by copying this group in the Exchange Control Panel.
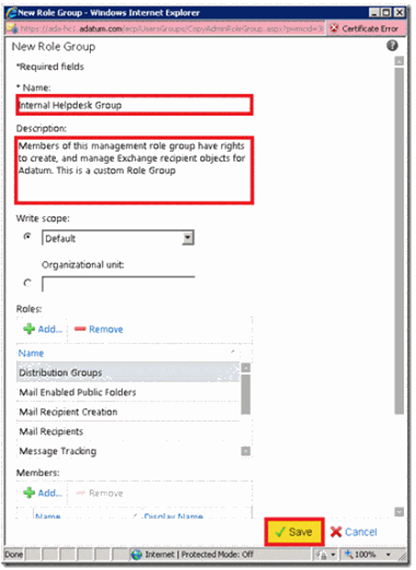
I gave this group a name and I edited the description to reflect the purpose of this group. I added the note that "This is a custom Role Group" so any future administrators can easily see that this has been customised from the default.
At that moment, I was not making any changes to Management Roles assigned to this group.
A Management Role Group is a collection of Management Roles. A Management Role is a collection of Management Role Entries. A Management Role Entry is simply a PowerShell command, along with parameters, that is able to run. So, to try to make this as simple as possible, a Management Role (e.g, Mail Recipients) is a collection of all the PowerShell commands that are required to manage Mail Recipients. A Management Role Group is a collection of Management Roles, that can be assigned to user accounts. So by building these groups and roles, we can be extremely granular in the permissions that can be assigned to users.
A Picture may help explain this: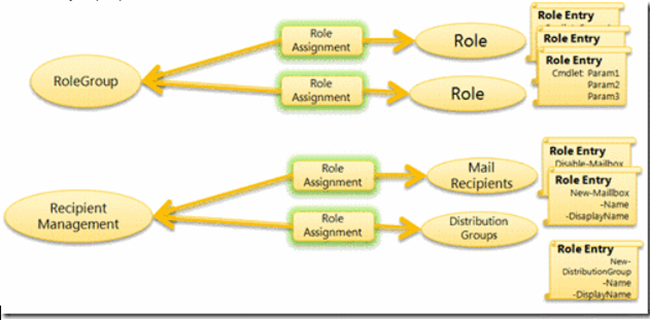
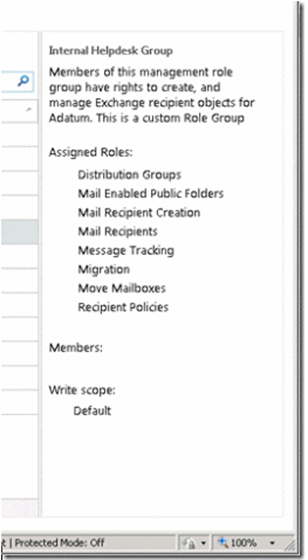
Within my "Internal Helpdesk Group", I had 8 Management Roles assigned, which were copied over from the default "Recipient Management" Role Group.
The requirement was to create a group that is able to manage Exchange Recipients, but not allowed to delete them. So I needed to see what PowerShell Cmdlets each Management Role grants access to. Unfortunately, there isn't a nice GUI to do this, so its time to fire up the Exchange Management Shell!
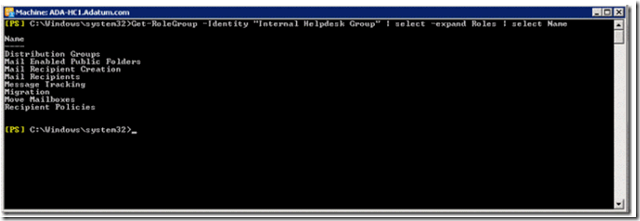
I started by getting the list of Management Roles that are assigned to my "Internal Helpdesk Group." To do this, I used the rather complicated command: Get-RoleGroup -Identity "Internal Helpdesk Group" | Select-Object -expand Roles | Select-Object Name.
If you are using a topology with multiple domains, you may need to add the –DomainController switch to this command, and point it at a domain controller in the domain where the “Microsoft Exchange Security Groups” OU is located.
This formats the roles in a simple to see format, and shows the same information as is in the ECP (Exchange Control Panel).
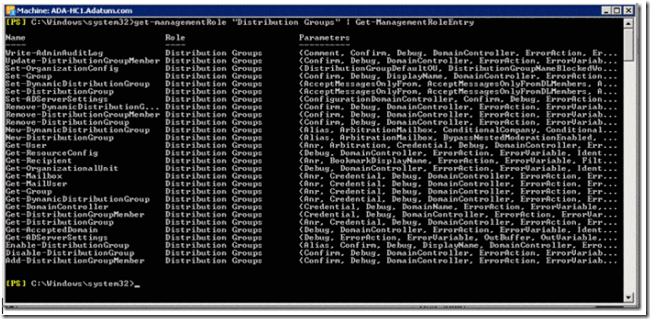
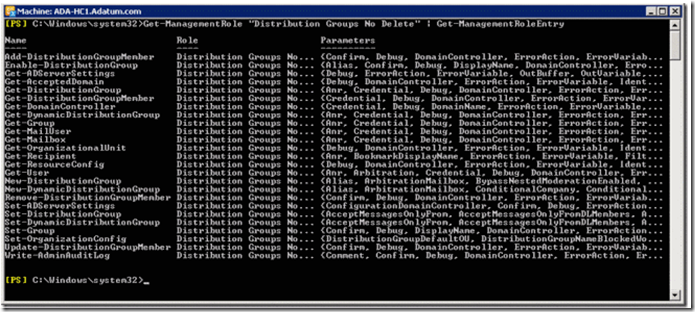
The next step was to look into each Role Group and see what PowerShell Cmdlets (Management Role Entries) are permitted within each group. I started by looking at "Distribution Groups":
Get-ManagementRole "Distribution Groups" | Get-ManagmentRoleEntry
Most of the commands in this role fit with what I wanted to do, however, I wanted to remove access to some of the Remove-* and Disable-* commands. To do this, I needed to edit the Management Role.
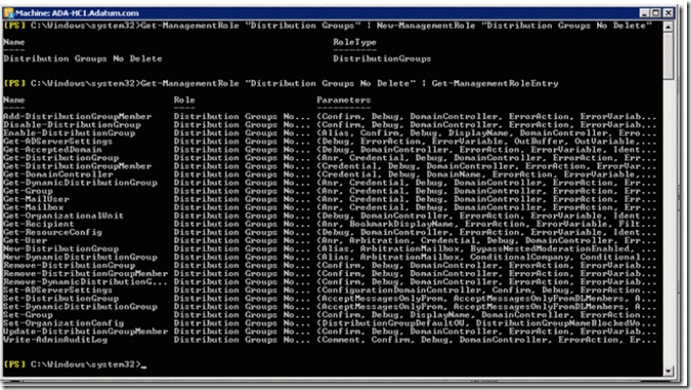
Best practice states that we should not change any of the built in Management Roles, so I copied this Management Role using the following command:
Get-ManagementRole "Distribution Groups" | New-ManagementRole "Distribution Groups No Delete"
As you can see, I copied this Management Role, and it contains the same Management Role Entries as before.
I wanted to remove the "Remove-DynamicDistributionGroup","Remove-DistributionGroup" and "Disable-DistributionGroup" entries for my custom group. To do this I ran the following command:
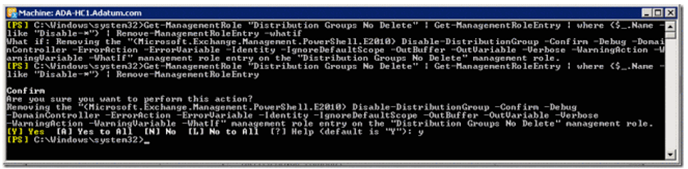
Get-ManagementRole "Distribution Groups No Delete" | Get-ManagementRoleEntry | Where {$_.Name -like "Disable-DistributionGroup”} | Remove-ManagementRoleEntry -Whatif
This command breaks down as follows:
Get-ManagementRole “Distribution Groups No Delete” | Get-ManagementRoleEntrywill return all the Management Role Entries assigned to this Management Role. TheWhere {$_.name –like “Disable-DistributionGroup”}will filter this down to a single Management Role Entry, which is then passed to theRemove-ManagementRoleEntryto remove the entry.
I added the "Whatif" parameter on this command so we could be sure we were removing the correct entry. If we are, then we can run this command again without that parameter.
I repeated this for the Remove Cmdlets:
Get-ManagementRole "Distribution Groups No Delete" | Get-ManagementRoleEntry | Where {$_.Name -like "Remove-DymanicDistributionGroup"} | Remove-ManagementRoleEntry -WhatifGet-ManagementRole "Distribution Groups No Delete" | Get-ManagementRoleEntry | Where {$_.Name -like "Remove-DistriubutionGroup"} | Remove-ManagementRoleEntry -Whatif
If you prefer, you could run this command specifying "Remove-*" in the Where clause. This will work, however, not all cmdlets need to be removed. For instance, you will still want the user to be able to run the "Remove-DistributionGroupMember" cmdlet. I have listed below the cmdlets that should be removed for this example.
And to make sure this was successful, I ran the Get-ManagementRole "Distribution Groups No Delete" | Get-ManagementRoleEntry command to ensure that the Disable and Remove cmdlets specified have been removed.
At this point, we’re done for the custom Distribution Groups Management Role. We then needed to repeat the above Process for the remaining Management Roles.
I then had to create custom roles for the following:
- Mail Enabled Public Folders (Remove access to the "Disable-MailPublicFolder" Command)
- Mail Recipient Creation (Remove Access to the "Remove-MailContact", "Remove-MailUser", "Remove-Mailbox", "Remove-RemoteMailbox" commands)
- Mail Recipients (Remove Access to the ""Disable-MailContact", "Disable-MailUser", "Disable-Mailbox", "Disable-RemoteMailbox" Commands)
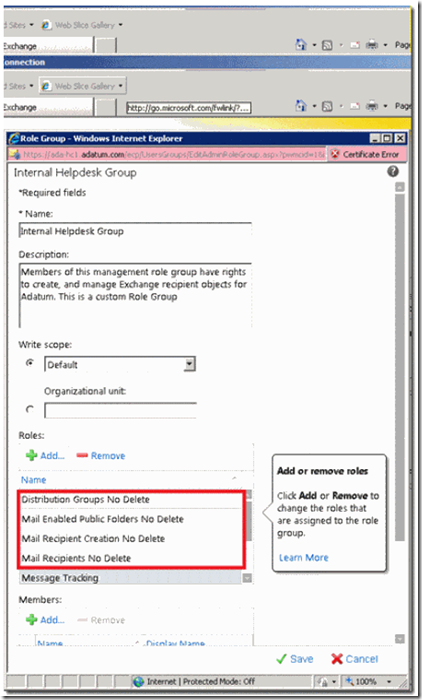
After completing these steps, we completed our Management Role customisation. We can then go into ECP, and assign these new Roles to the custom Management Role Group
First remove the existing roles:
And add our new Custom Role:
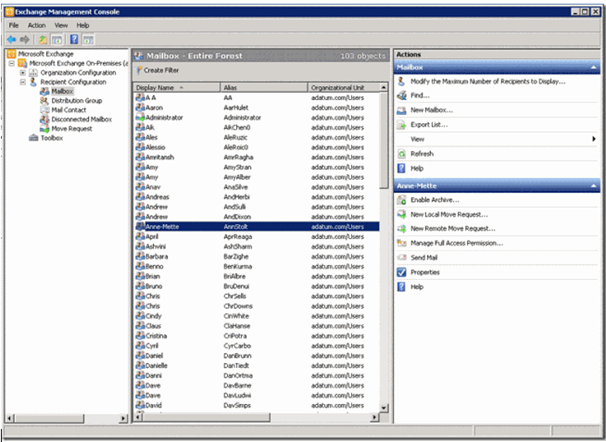
After we assigned this group to the helpdesk staff, when they log into the EMC, the removal options are unavailable.
That’s it! Hope you found this helpful.
(article by Matt Abraham)