Filter the security events the OMS Security collects
OMS Security collects all events from Windows Security, App Locker, and Firewall event logs. As OMS is a big data service, it can handle a large amount of data, and customers don’t need to carefully sift through their events to decide which ones to save. But, we have heard from customers that in some cases, they would like to reduce the volume of events that are being collected.
Today, we are enabling a new capability to filter the collected events by selecting sets of events. We wanted to balance the need to reduce the volume while maintaining enough events for investigation, auditing, and threat detection. We also wanted to create a simple mechanism that would allow customers to choose the right filtering policy without maintaining endless lists of event IDs.
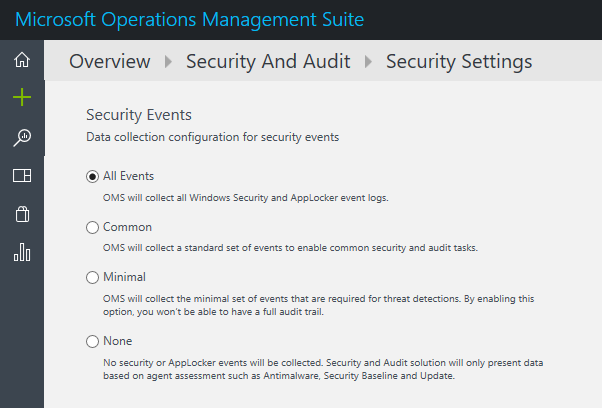
With this new capability, OMS Security allows the selection of four sets of events to be collected by the agent. The four sets are:
- All events – For customers who want to make sure all events are collected. This is the way OMS Security worked until now and will continue to be the default.
- Common – This is a set of events that will satisfy most customers and allow them a full audit trial.
- Minimal – A smaller set of events for customers who want to minimize the event volume.
- None – Disable security event collection from security and App Locker logs. For customers who choose this option, their security dashboards will have only Windows Firewall logs and proactive assessments like antimalware, baseline, and update.
These sets were designed to address typical scenarios. Make sure to evaluate which one fits your needs before implementing it.
To choose the set for your workspace, click the Settings button from the main security dashboard:
To determine the events that will belong to each set, we worked with several dozen customers and industry standards. We processed the statistics that they shared with us to learn about the unfiltered frequency of each event and their usage. We used the following guidelines in this process:
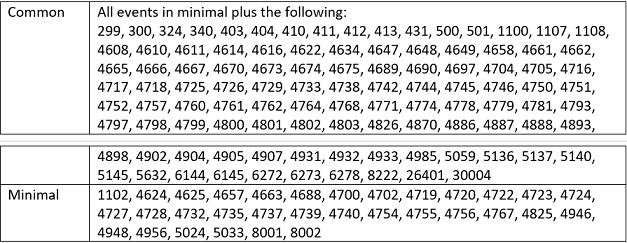
- Make sure that the minimal set covers only events that might indicate a successful breach and important events that have a very low volume. For example, this set contains user successful and failed login (event IDs 4624, 4625), but it doesn’t contain logout which is important for auditing but not meaningful for detection and has relatively high volume. Most of the data volume of this set is the login events and process creation event (event ID 4688).
- Provide a full user audit trail in the common set. For example, this set contains both user logins and user logoff (event ID 4634). We also included in the common set auditing actions like security group changes, key domain controller Kerberos operations, and other events that are recommended by industry organizations.
- Events that have very low volume were included in the common set as the main motivation to choose it over all the events is to reduce the volume and not to filter out specific events.
Here is a complete breakdown of the Security and App Locker event IDs for each set:
Other than offering the filtering option, we are always working to improve the parsing and indexing capabilities of the security events. For frequent events, we are making sure that all properties are extracted and indexed. For these events, we removed the EventData property that includes the unparsed XML to reduce their volume.
We are looking for feedback and will fine-tune the event IDs in the different sets. Send us your feedback to: omssecfeedback@microsoft.com. As much as we can, we will try to move events from the bigger sets like all events and common to the smaller sets like minimal and not vice versa.