Use OMS Security to assess the Security Configuration Baseline
Summary: Learn about the security baseline assessment capability in OMS Security & Audit.
The most important defense against malicious attackers is to ensure that the server’s operating system is well hardened and using available built-in security capabilities. Server operating systems are delivered with a wide range of security measures. Some of them are enabled by default, and some are disabled by default to allow various types of real-world scenarios.
Microsoft, together with industry and government organizations worldwide, defines a Windows configuration that represents highly secure server deployments. This configuration is a set of registry keys, audit policy settings, and security policy settings along with Microsoft’s recommended values for these settings. This set of rules is known as Security baseline. You can read more about Windows security baseline here:
There are various tools to manage security baselines. The most commonly used tool is Microsoft Security Compliance Manager that lets you generate group policy to enforce baselines.
Today, we are bringing the security baseline assessment capability to OMS Security & Audit. Because OMS is a cloud service, you can seamlessly scan all your computers for compliance and manages all of the results in the cloud with no additional effort. This functionality is available for all OMS Security & Audit customers with no need to turn it on explicitly or install anything.
The OMS agent was extended to perform this evaluation. This works both for customers who are using OMS Direct agent and customers who are using OMS via System Center Operations Manager (SCOM). Once a day, the agent checks all the rule configuration settings and evaluates the results. It adds to the OMS workspace data on the state of each rule and a summary on each evaluation.
OMS supports the domain member baseline profile on Windows Server 2008 R2 up to Windows Server 2012 R2. Windows Server 2016 baseline isn’t final yet and will be added as soon as it is published.
Security baseline dashboard
OMS Security & Audit solution includes a new dashboard to reflect the baseline results:
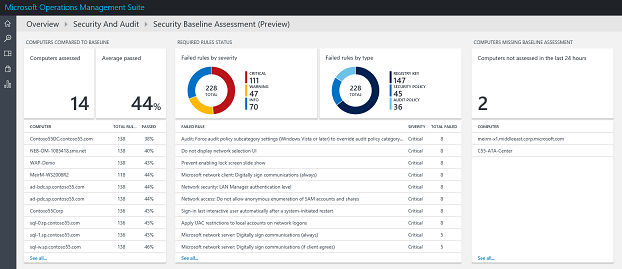
In the dashboard, you can review:
- Which machines in the workspace have most failed rules
- Which rules failed the most
- Which machines were not evaluated due to operating system incompatibility or other failures
Query the security baseline results
All results are stored in the OMS in two new data types:
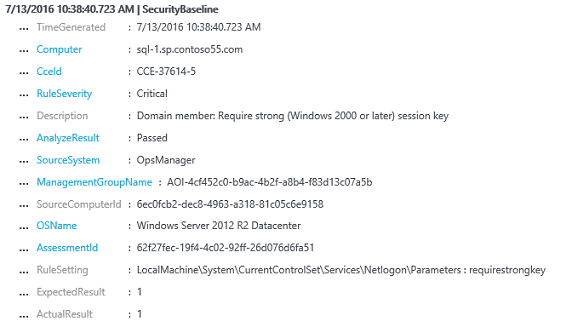
- SecurityBaseline
Each record represents a single baseline rule evaluation on a single computer and includes all data on the rule, expected result, and actual result:
- SecurityBaselineSummary
Each record represents a full set of baseline assessment on a single computer and includes a summary of the results. The SecurityBaselineSummary record could be associated with the multiple SecurityBaseline records via the AssessmentId property.
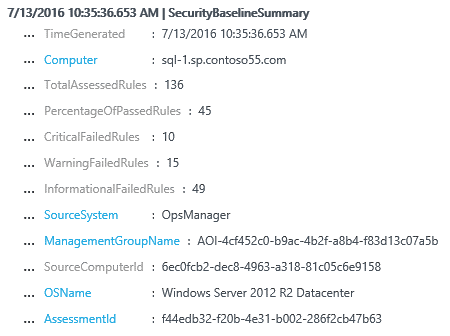
You can use these records to create your own dashboards, reports, or alerts. You can also use them in conjunction with computer groups to filter according to your organization logic.
Here are two examples of how to search for baseline data:
- Show all results for a specific computer over time:
Type=SecurityBaselineSummary Computer="sql-0.sp.contoso55.com" | select PercentageOfPassedRules
- Show all critical rules that failed for a specific computer group:
Type=SecurityBaseline RuleSeverity=Critical AnalyzeResult=Failed Computer IN $ComputerGroups[SQL_Servers]
What's next
This is just the beginning of our work on security baselines. We are going to expand it in the future. Here are the areas that we are looking at:
- Provide additional description on the baseline rules
- Ability to ignore specific rules
- Creation of additional custom rules
- Baseline for Linux
I invite you to follow me on Twitter and the Microsoft OMS Facebook site. If you want to learn more about Windows PowerShell, visit the Hey, Scripting Guy Blog.
Get a free Microsoft Operations Management Suite (#MSOMS) subscription so that you can test the new alerting features. You can also get a free subscription for Microsoft Azure.
Microsoft Operations Management Team