OMS Log Analytics Forwarder
Summary: Collect and view data in OMS from your devices with no Internet connectivity.
Hi everyone, Nini here, and today I am going to talk about the new OMS Log Analytics Forwarder and how you can use it to allow your OMS-managed devices (Windows and Linux) to send data to a central server that has access to the Internet.
A problem some enterprises face today is the inability to collect data from servers and clients (including point of sale devices) when they have no Internet connectivity. This is where we come in! With the OMS Forwarder, which is now in public preview, you can transfer data from agents installed on these devices to OMS. This way, all agent data is sent through a single server that has the OMS Forwarder installed on it and access to the Internet. In this scenario, the Forwarder efficiently transfers data from the agents to OMS directly without analyzing any of the transferred data.
What is the OMS Log Analytics Forwarder?
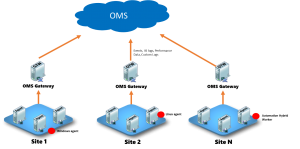
Now that we understand the problem being solved, you’re probably wondering what it is and how it works. Simply put, the OMS Log Analytics Forwarder is an HTTP forward proxy that supports HTTP tunneling through the HTTP CONNECT command. It is able to handle up to 1,000 OMS concurrently-connected devices when run on a 4 core, 8G Windows Server with a 1Gbps network connection. Here’s a simple diagram to show how it is all connected (click the image to see a larger version):
In order for the OMS Log Analytics Forwarder to know the service end points that it needs to communicate with, we recommend that you install the OMS agent on the computer where the Forwarder is also installed. Additionally, when an OMS agent and the OMS Log Analytics Forwarder are on the same computer, you can monitor the health and performance of the Forwarder. Note that the Forwarder must have access to the Internet in order to upload data to OMS. This forwarder will also support OMS automation hybrid workers after proxy support is added. Please note that for this Public Preview release, we do not support SCOM Management Server using the OMS Forwarder.
Do not install the forwarder on a computer that is also a domain controller.
Got it! How can I install the OMS Log Analytics Forwarder?
You can do this in three easy steps!
Step 1: Install the OMS agent on the same server where you plan to use to install the Forwarder.
In order for the OMS Forwarder to know the endpoints that it needs to talk to, you need to install the OMS agent on the server on which you plan to install the Forwarder.
Follow the instructions in Connect Windows computers directly to OMS to install the agent. This link will show you how you can install the agent via the UI and via command line.
Note: Please wait for 2-3 minutes after you install the agent to install the OMS Forwarder.
Step 2: Install the OMS Log Analytics Forwarder
Prerequisites: .Net Framework 4.5, Windows Server 2012 R2 SP1 and above
- Download the MSI.
- On the Welcome page, click Next.
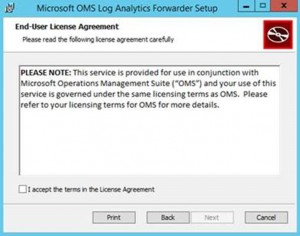
- On the License Agreement page, select I accept the terms in the License Agreement to agree to the EULA and then click Next.
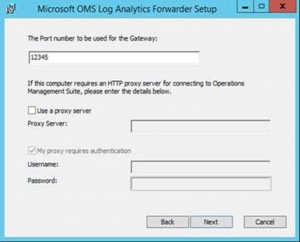
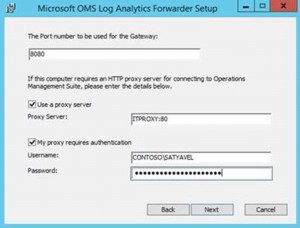
- On the Port and Proxy Address page, do the following:
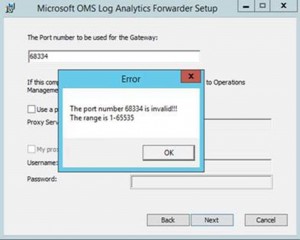
Type the TCP port number to be used for the forwarder. Setup opens this port number from Windows firewall. The default value is 8080. The valid range of the port number is 1 to 65,535. If the input does not fall within this range, an error message box will open.
Input the proxy address where the Forwarder needs to connect, if the server on which the Forwarder resides needs to go through a proxy. For example, myorgname.corp.contoso.com:80. This is an optional value. If it’s blank, the Forwarder will try to connect to the Internet directly. Otherwise, the Forwarder will connect through your internal proxy. If your proxy requires authentication, you can provide a username (domain\user) and password.
Note: If you do not provide a domain for the user, it will not work.
Click Next.
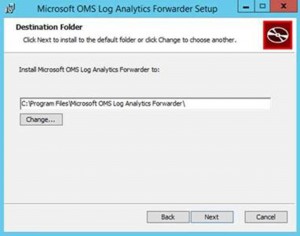
- On the Destination Folder page, either leave the default folder, %ProgramFiles%\OMS Log Analytics Forwarder, or type the location where you want to install forwarder, and then click Next.
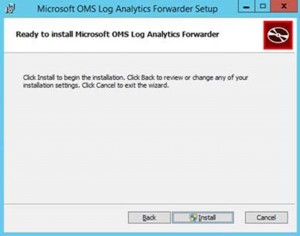
- On the Ready to install page, select Install. A User Account Control might appear requesting permission to install. If so, click OK.
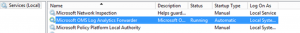
- After Setup completes, click Finish. You can verify that the service is running by opening the services.msc snap-in and checking for Microsoft OMS Log Analytics Forwarder.
Step 3: Configure OMS Agent to use the OMS Log Analytics Forwarder to send data
See Configure proxy and firewall settings for information about how to configure an OMS Windows agent to use a proxy server, which in this case is the OMS Forwarder. If you are using the OMS Linux agent, use the steps in Configuring the agent for use with an HTTP proxy server.
Troubleshooting the OMS Log Analytics Forwarder
We highly recommend that you install the OMS agent on computers where you install the Forwarder. You can then use the agent to collect the events that are logged by the Forwarder . 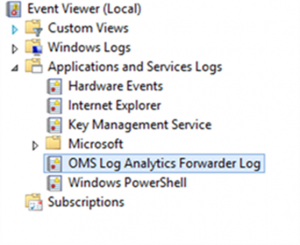
OMS Log Analytics Forwarder Event IDs and Descriptions
| Name | Description |
|---|---|
| 400 | Any application error that does not have a specific id |
| 401 | Wrong configuration. For example: listenPort = “haha” instead of an integer |
| 402 | Exception in parsing TLS handshake messages |
| 403 | Networking error. For example: cannot connect to target server |
| 100 | General information |
| 101 | Service has started |
| 102 | Service has stopped |
| 103 | Received a HTTP CONNECT command from client |
| 104 | Not a HTTP CONNECT command |
| 105 | Destination server is not in allowed list or the destination port is not secure port (443) |
| 106 | In any reason that the TLS session is suspicious and rejected |
| 107 | The TLS session has been verified |
Performance Counters to Collect
| Name | Description |
|---|---|
| OMS Log Analytics Forwarder\Active Client Connection | Number of active client network (TCP) connections |
| OMS Log Analytics Forwarder\Connected Client | Number of connected client |
| OMS Log Analytics Forwarder\Rejection Count | Number of rejections due to any TLS validation error |
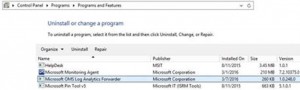
Uninstalling the OMS Log Analytics Forwarder from Add/Remove Program
Supported number of Agent connections
| Gateway | Approx. Number of Agents Supported |
|---|---|
|
|
|
|
This support is based on agents uploading ~200KB of data every 6 seconds. The data volume per agent tested is about 2.7GB per day.
Supported Operating System
- Client SKU: Windows 7, Windows 8.1, Windows 10
- Server SKU: W2K8 R2, W2012, W2012R2
What's next?
Moving forward, we plan on releasing a solution that allows you to view the health and performance of your Forwarders and Agents in OMS, as well as improving the functionality of the OMS Forwarder based on your feedback!
That is all I have for you today. If you have any feedback or questions, please comment below.
Priscilla Nini Ikhena
Microsoft Operations Management Team