Autopilot profile assignment using Intune
We’ve had questions over the past several months, as customers scale up with Autopilot, about how to assign an Autopilot profile to new devices, as it can get kind of tedious to have to do this manually each time you add a new batch of devices (either by uploading them yourselves, or having an OEM do it for you). Fortunately, the Intune team has been busy working on a mechanism to do this.
Let’s start with a basic premise: Instead of doing things to individual devices or users (which is tedious), you instead want to do things to groups. And as those groups get new members, those new members should be handled automatically. That’s the mechanism that Intune uses today for lots of things: apps, policies, settings, etc. You assign those to a group, and members of that group get whatever is assigned to them. See this article for an example.
Now, if you think about an Autopilot profile, it’s really just a group of settings that control how the device should behave when it is being set up. So it makes sense to assign an Autopilot profile to a group so that all devices that are members of that group automatically get that profile assigned.
The Simple Case
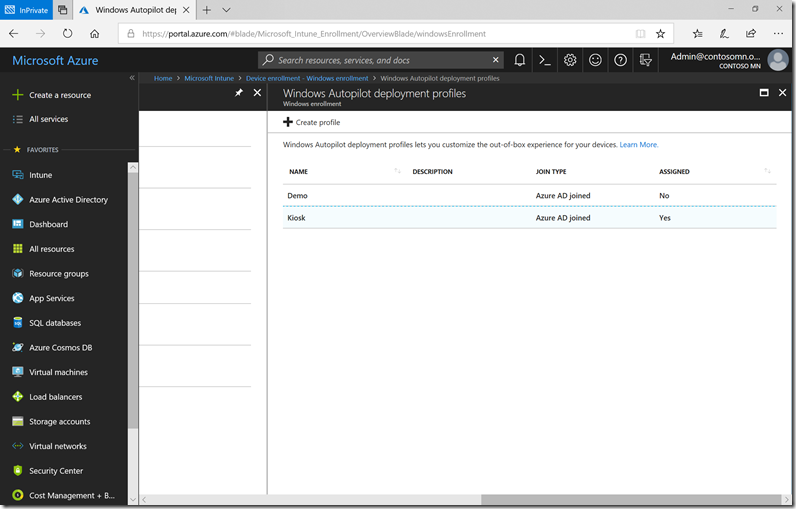
In the simplest case, you can do this using a group containing static members. Let’s walk through an example from my Intune tenant. First, I have an Autopilot profile called “Kiosk” that is configured with the settings I want:
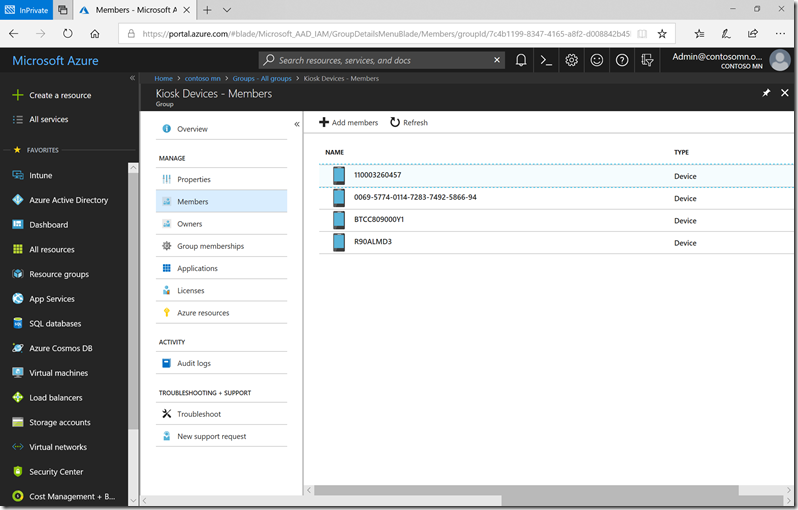
And I have an Azure AD group with a number of devices that are members:
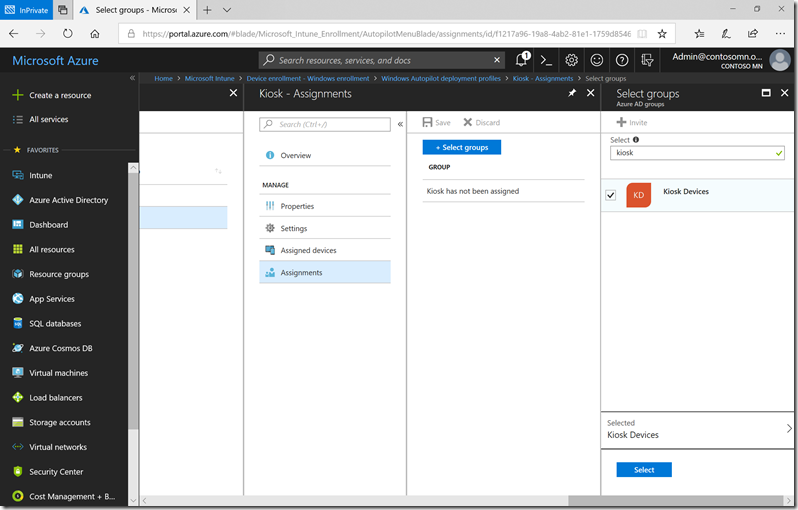
So, all I need to do is assign the Autopilot profile to that group. Select the profile, click on Assignments, click “Select groups” and choose the appropriate group (or groups) that the profile should be assigned to:
Click “Select” and then “Save” (don’t forget that step). In the background, the assignment will be processed. If you watch carefully, you can see each Autopilot-registered device in that group change from “Not assigned” to “Assigning” to “Assigned” without you doing anything. (Give it a few minutes.)
Where did the Azure AD device come from?
You might think “how can I add a device to an Azure AD group before it’s joined to Azure AD.” If so, you’re on the right path. What happens when you add a new device to Autopilot (via Intune, Microsoft Store for Business, or any other path)? An associated Azure AD object is automatically created. That object is named using the serial number of the device, and it is not enabled until the device actually completes the Azure AD join process. When that happens, the device is renamed to have the “real” computer name from the device.
So these pre-created devices enable you to place the devices into Azure AD groups and use them for Intune assignment purposes.
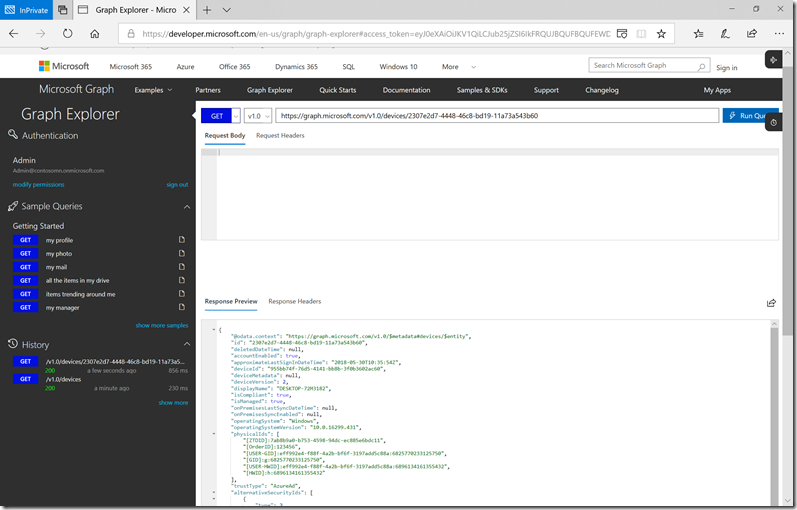
It’s also worth mentioning that there are multiple properties automatically “tagged” onto those pre-created Azure AD objects; the usefulness of those will become apparent later. For those that are technically inclined, you can you look at these using the Graph Explorer website. Here’s an example from my tenant:
The key part is the “physicalIds” values (a multiple-value property, basically an array of values):
"physicalIds": [
"[ZTDID]:7ab8b9a0-b753-4598-94dc-ec885e6bdc11",
"[OrderID]:123456",
"[USER-GID]:eff992e4-f88f-4a2b-bf6f-3197add5c88a:6825770233125750",
"[GID]:g:6825770233125750",
"[USER-HWID]:eff992e4-f88f-4a2b-bf6f-3197add5c88a:6896134161355432",
"[HWID]:h:6896134161355432"
]
There are three values that you should be aware of:
- ZTDID. This is a unique value (a GUID) assigned to all Autopilot-registered devices. So you can use this value to easily determine which devices are registered.
- PurchaseOrderID (not set in my sample above). This value is set by OEMs when processing an order for new devices; when they upload those devices to the Autopilot deployment service, they will set the PurchaseOrderID value to the purchase order number for the order. That makes it easy to identify all the devices from a particular order.
- OrderID. This value is actually more of a “tag.” When you upload devices to Intune, you can specify an optional “OrderID” column that is used to arbitrarily group devices. For example, you could set the OrderID value to “Kiosk” and use that to easily tag all kiosk machines.
All three of these values can be used as part of a dynamic membership rule for an Azure AD group, which leads to all sorts of interesting scenarios.
Assign a profile to all Autopilot devices
If you have simple requirements, e.g. all devices will use the same Autopilot profile, this gets even easier: You can create an Azure AD dynamic group that automatically selects all devices that are registered with Autopilot.
How do you do that?
Here’s the step-by-step:
-
- Navigate to “Azure Active Directory –> Groups” and click “New group”.
- Specify “Security” for the group type, and provide an appropriate group name.
- Select “Dynamic Device” as the membership type.
- Click “Add dynamic query” and then “Advanced rule” and paste in this exact string (yes, including the parenthesis):
(device.devicePhysicalIDs -any _ -contains "[ZTDId]")
- Click “Add query” and then “Create.”
After a period of time (think minutes, not seconds), the group will be populated with all the Autopilot clients defined to your Azure AD tenant. You can then take the next step of assigning an Autopilot profile to that group.
Assign a profile to a purchase order ID
This is the same basic process, but with a different dynamic query:
(device.devicePhysicalIds -any _ -eq "[PurchaseOrderID]:333000")
Put in your own purchase order ID value (instead of the “333000” value in the sample above) and you’re all set.
Assign a profile to an order ID
Again, just a different dynamic query:
(device.devicePhysicalIds -any _ -eq "[OrderID]:123456")
Put in your own order ID value (instead of the “123456” value in the same above) and you’re all set.
Got any other interesting scenarios? Leave comments with the details.