How to provide a Vista image to departments without storing your MAK in clear text
This scenario comes up frequently and I want to show exactly how the process works. The concern I have heard is from Universities that wish to provide an image to a remote department and for whatever reason the KMS is not an option. In most cases the KMS will work but there are examples of departments that are not well connected and have fewer than 25 machines or they consistently work off campus and the machines do not connect in for more than six months, etc.
So you want to provide the image to a remote department but you are concerned about exposing your MAK? No problem, while you cannot encrypt the key in the answer file you can store and protect the key in your image. The key point of understanding is which setup pass you select for storing the key in your answer file and when you use it. Let's take a look at the documentation for the ProductKey attribute in the unattended reference guide:
ProductKey
ProductKeyspecifies the product key to apply for each unique installation of the Windows operating system.There are two Product Key settings you can configure.
- Use this
ProductKeysetting to specify the Windows image to install during Windows Setup. This product key specified by this setting is stored on the computer after installation. If you choose to activate Windows, this product key will be used.- Use the ProductKey setting to specify a different product key to activate Windows. For example, you can specify one product key to install Windows with the
ProductKeyin Microsoft-Windows-Setup component, and then specify a different product key to activate Windows with ProductKey
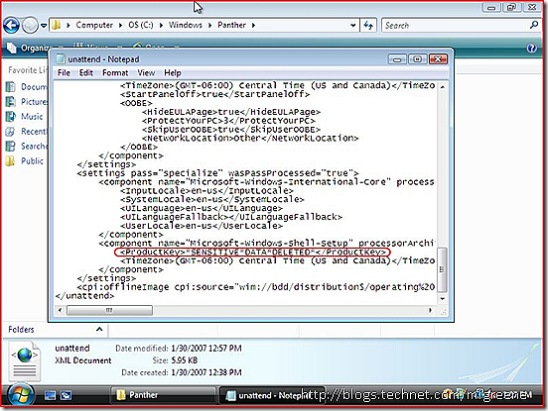
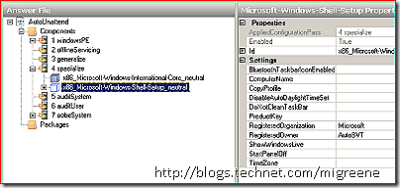
This translates in System Image Manager to whether you store the key in pass 1 (Windows PE) or 4 (Specialize). They key you store in pass 1 will be used for the install but would not be retained through a sysprep. However, you can set the key in pass 4 and it will be retained even through a sysprep, until the machine has been activated. However, the key will not be shown in clear text within the cached answer file, it is protected within the OS.
System Image Manager:
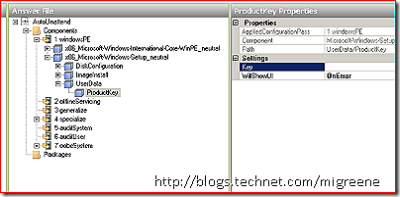
Pass 1 - Setup - User Data - ProductKey - Key
Pass 4 - Shell Setup - ProductKey
Once you have created your answer file, use it when running setup to build your base machine. You would not just provide the answer file to the department or leave it stored in the image. When you are ready to build a workstation to create your custom image, boot off the Vista DVD and make sure the answer file is stored on removable media (floppy, USB key, etc) so it will be used during setup. Do not activate the machine yet. Once you have your customizations complete, run sysprep (possibly specifying another answer file for future OOBE) and after the machine shuts down use imagex.exe to capture it.
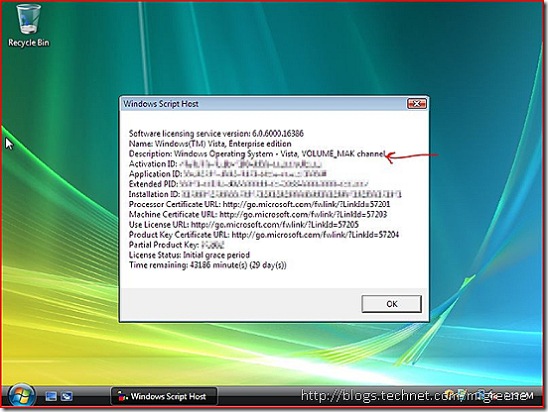
Even though the machine has been syspreped, the ProductKey is stored securely in the image. It is not displayed in clear text as you can see below but is retained as I demonstrate in the screenshot using slmgr.vbs. If you provided the key during pass 1 of setup, this would not be the case.
Finally, one concern I have heard on this topic is how to prevent someone from using the image with the MAK stored in it even though they do not have permission (piracy). It's true you now have an image that you need to protect from broad availability. However, if a problem should arise where a department admin accidentaly exposes the image publicly, VA 2.0 can handle the issue without needing to reimage or rekey existing machines. The available activations for the embedded MAK would be changed to 0 and a new key would be issued for future use.