Choosing a sourceAnchor for Multi-Forest Sync with AAD Connect - Part 6, Moving off objectGuid
Update 25th May 2017:- As of AAD Connect May 2017 release, version 1.1.524, the default sourceAnchor used by the setup wizard is mS-DS-ConsistencyGuid. This renders most of this blog post series moot but it will be maintained for reference.
This blog post series is based upon and tested with AAD Connect, December 2016 release, version 1.1.380.0. Test all deployment designs before production implementation.
Table of Contents
Part 3, An Aside on EmployeeID
Part 4, Using msDS-SourceAnchor
Part 5, Using mS-DS-ConsistencyGuid
Part 6, Moving off objectGuid
Correcting an earlier choice of objectGuid
As it turns out, if you've previously selected objectGuid as you sourceAnchor, you can very easily change to using msDS-SourceAnchor or mS-DS-ConsistencyGuid.
Pause the sync service by opening a PowerShell prompt and executing
Set-ADSyncScheduler -SchedulerSuspended $true
Choose either msDS-SourceAnchor or mS-DS-ConsistencyGuid and make the rule edits described in Part 4 of this series for msDS-SourceAnchor or Part 5 of this series for mS-DS-ConsistencyGuid.
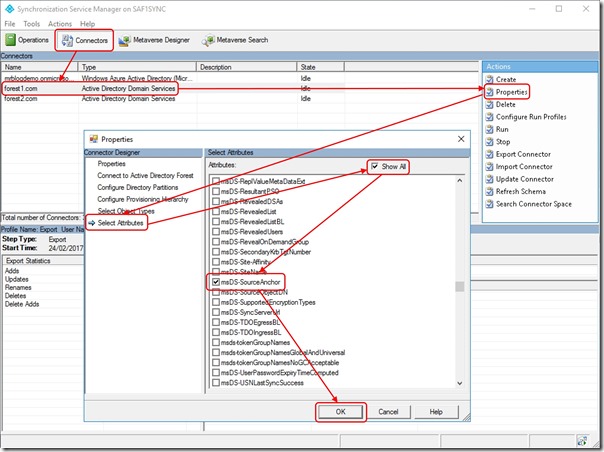
Open "C:\Program Files\Microsoft Azure AD Sync\UIShell\miisclient.exe"
Navigate to Connectors
Select the first Forest connector and click Properties
In the properties sheet, click Select Attributes
Check Show All
Scroll down and check msDS-SourceAnchor (or mS-DS-ConsistencyGuid if you're using that)
Click OK
Repeat for all other Forest connectors
Resume the sync service by opening a PowerShell prompt and executing
Set-ADSyncScheduler -SchedulerSuspended $false
Trigger a delta sync by executing
StartADSyncSyncCycle -PolicyType Delta
What about when other attributes are used for sourceAnchor?
Now you're in a world of hurt.
You need to uninstall AAD Connect and have the wizard remove all components including the sync database. You need to delete your users from Azure Active Directory and you need to start again.
An alternative to starting over is to change the ImmutableID by
Logging into https://manage.windowsazure.com
Navigating to the Azure Active Directory tenant
Selecting Directory Integration
Disabling Directory Sync
Note: It will take time to disable sync for all users … around 1 hour for every 2000 users. Due to the asynchronous nature of this task under the hood, it may not begin immediately (sometimes a delay of hours and in rare cases days). Sync cannot be enabled again until this task is complete.
Change the UPN for users to the .onmicrosoft.com tenant domain -
Set-MsolUserPrincipalName -NewUserPrincipalName user@tenant.onmicrosoft.com -UserPrincipalName user@publicdomain.com
Change the ImmutableID to the value you want to use for each user -
Set-MsolUser -UserPrincipalName user@tenant.onmicrosoft.com -ImmutableId newValue
Change the UPN back to the public domain name -
Set-MsolUserPrincipalName -NewUserPrincipalName user@publicdomain.com -UserPrincipalName user@tenant.onmicrosoft.com
Enable sync for the Azure Active Directory tenant again (again more time for sync to start again)
AAD Connect configuration will need to be updated to reflect the use of the new sourceAnchor
Depending on the services you're using with your Azure Active Directory tenant, you may be facing mailbox export/import operations and various other problems.
I would recommend engaging with Microsoft Premier Field Engineering, Microsoft Consulting or a trusted cloud partner to help you through it.
Conclusion
Moving away from objectGuid over to msDS-SourceAnchor or mS-DS-ConsistencyGuid as your sourceAnchor is relatively easy.