How to prevent internal users from autoforwaring mails to external recipients
For reasons of their own, some users create Inbox rules to auto-forward their work mails to their private mail or other external domains. As an administrator thats not necessarily at desired scenario.
To prevent internal users from auto-forwaring mails to external recipients you can create a Transport Rule.
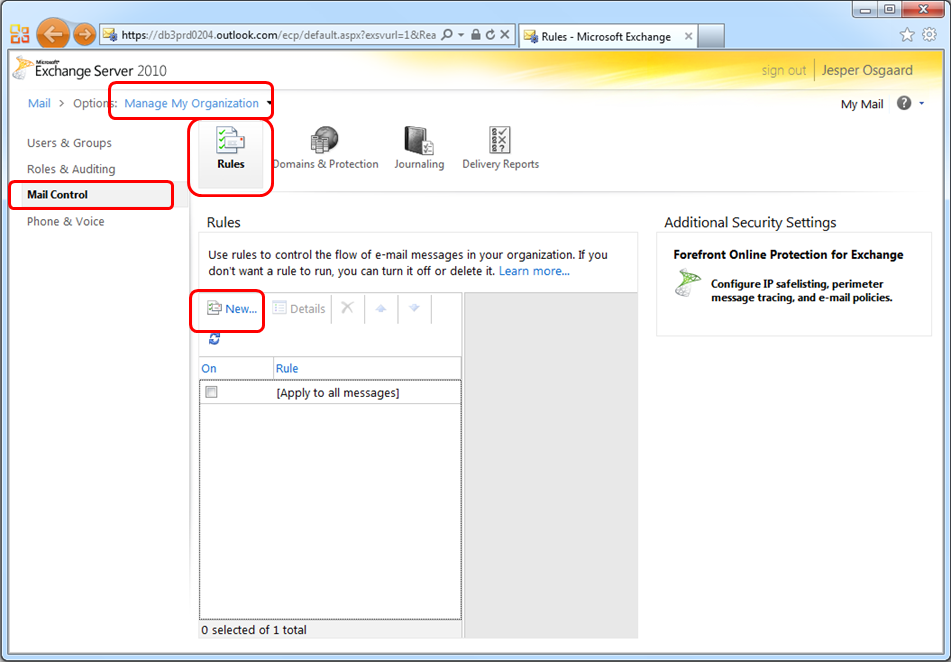
Log into the Microsoft Online Portal, and navigate to the Exchange Online Control Panel (ECP)
- Change the view so you are managing the entire organization, and not just your individual mailbox (Mail>Options>"Manage My Organisation" -- see top of picture below)
- Select "Mail Control" and make sure you are viewing the "Rules" tab (see left of picture below)
- Click the "New" button to display the "New Rule" dialog and start building a new transport rule (see center of picture below)
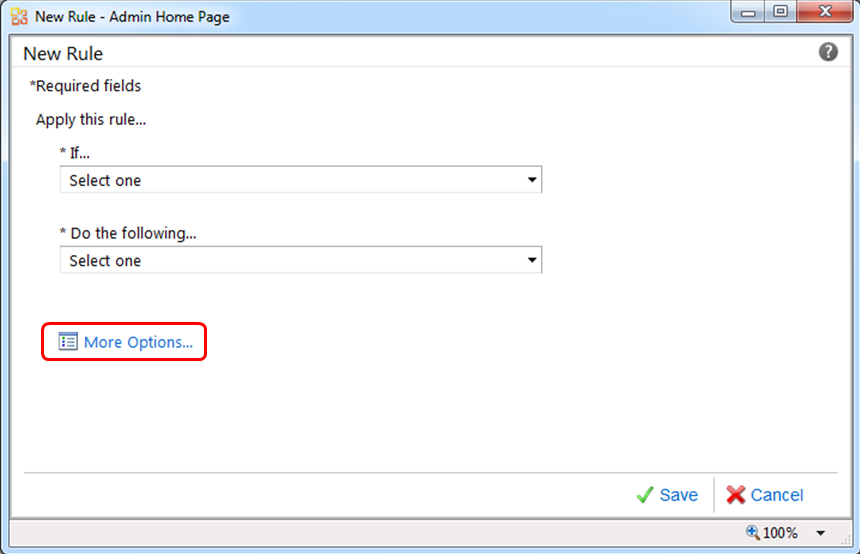
In the dialog "New Rule", clicking ”More Options” …
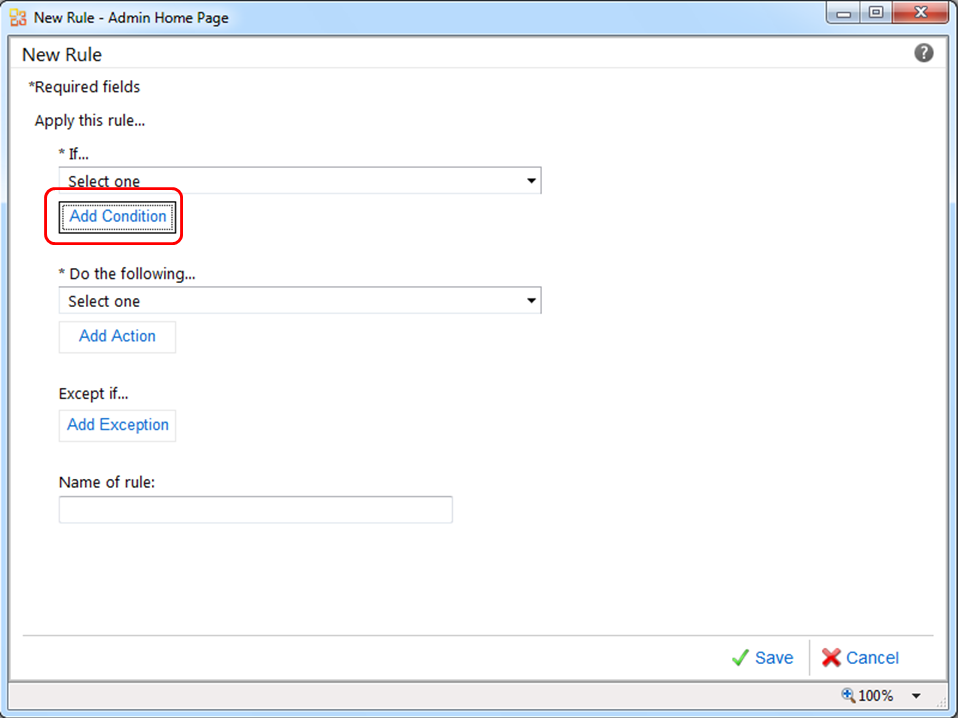
...will enable adding more conditions
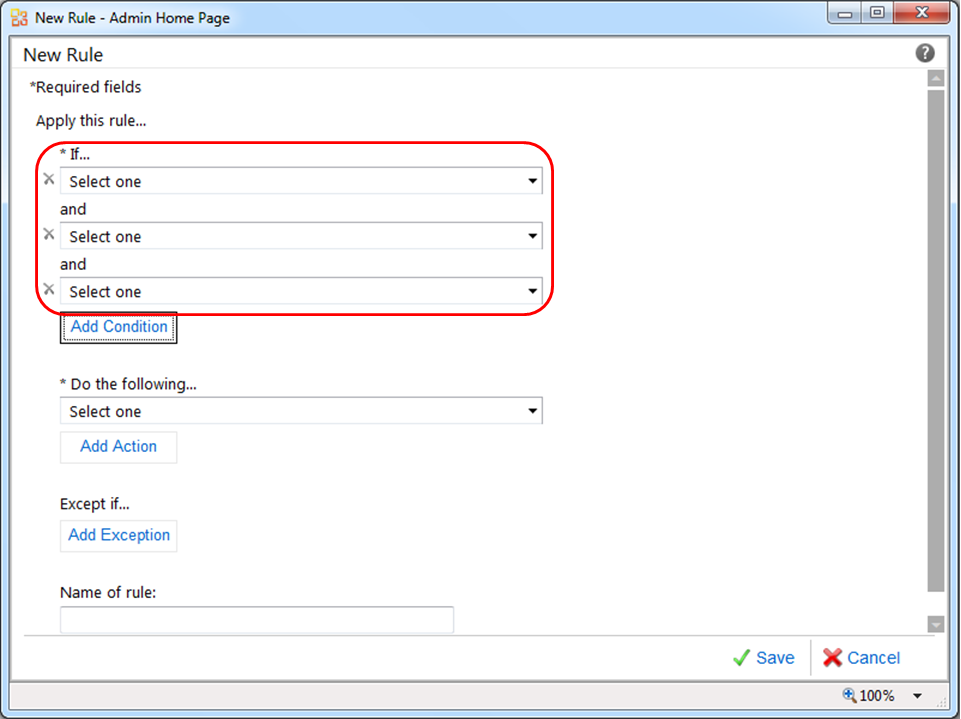
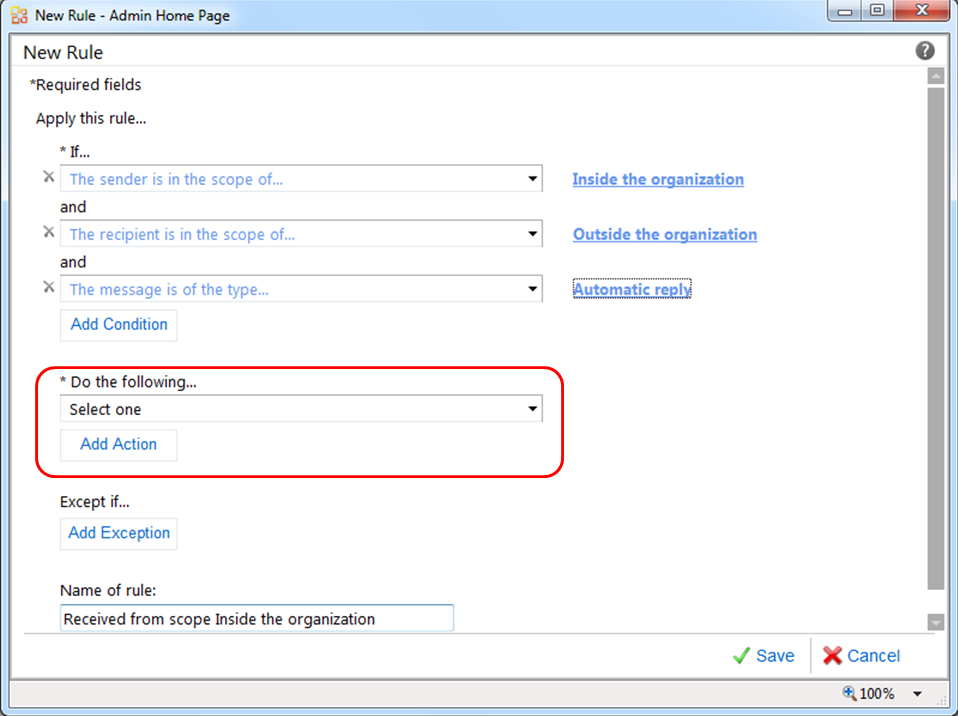
After clicking ”Add Condition” twice you have a triple AND-condition
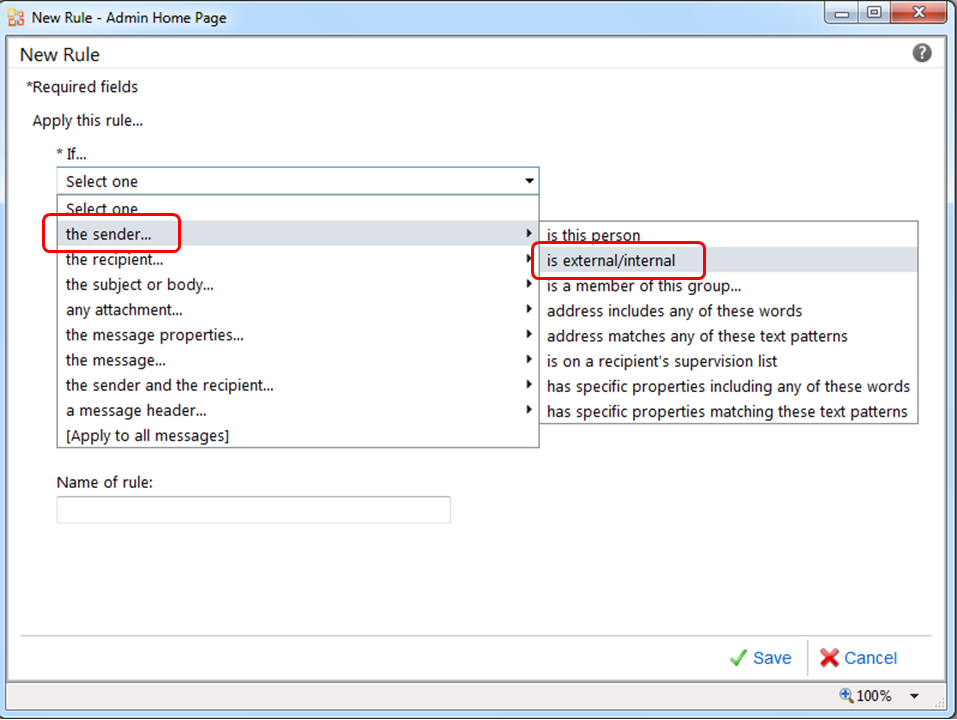
For the first condition, in the "If..." section pick ”the sender….” and then ”is external/internal”
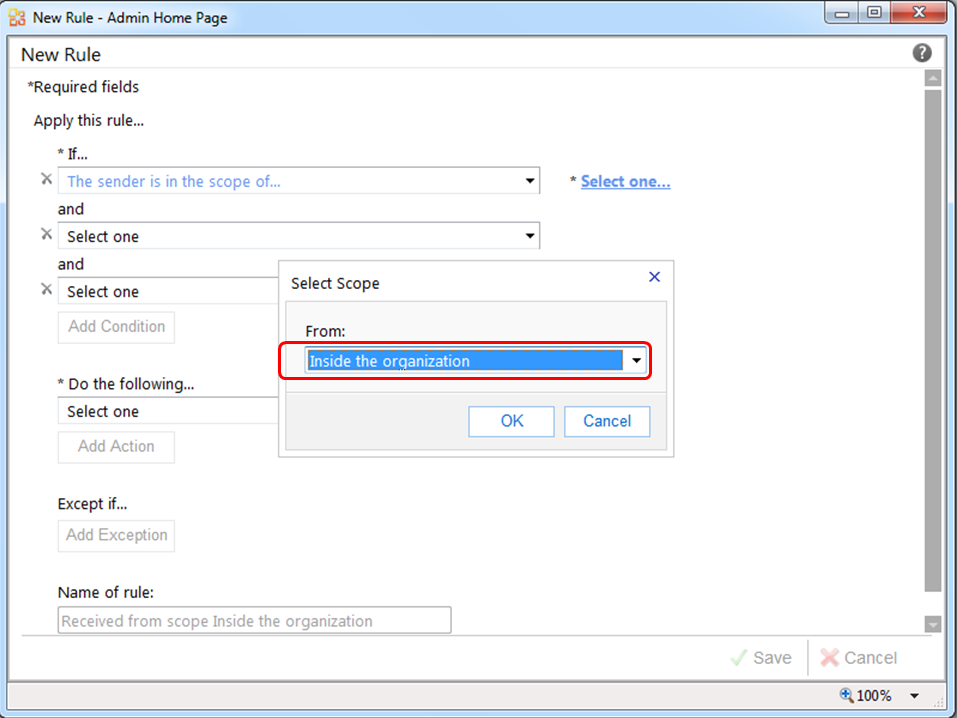
In the ”Select Scope” dialog pick ”Inside the organisation”
For the second condition repeat the above with ”the recipient…” and then ”is external/internal” and then ”Outside the organisation”
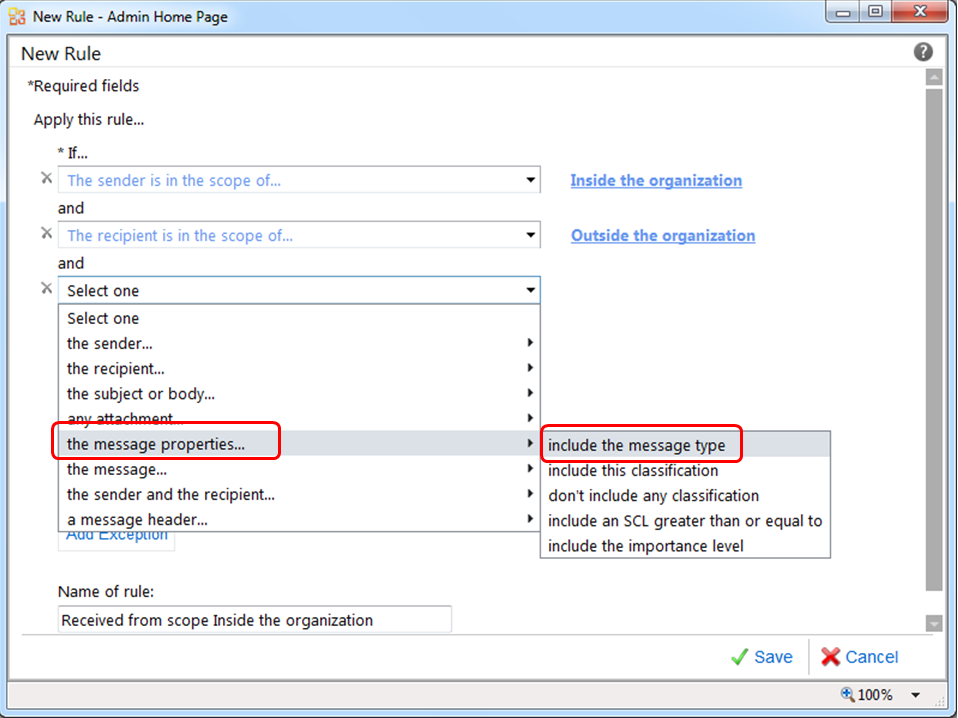
For the third and final condition pick ”the message properties…” and then ”include the message type”
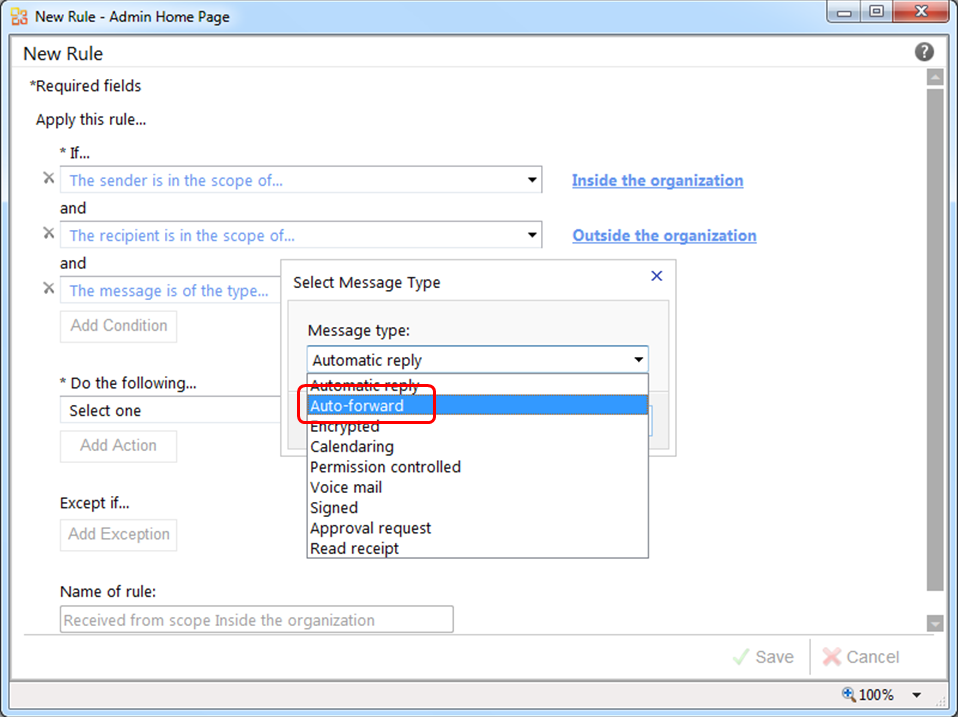
In the ”Select Message Type” dialog pick ”Auto-forward”
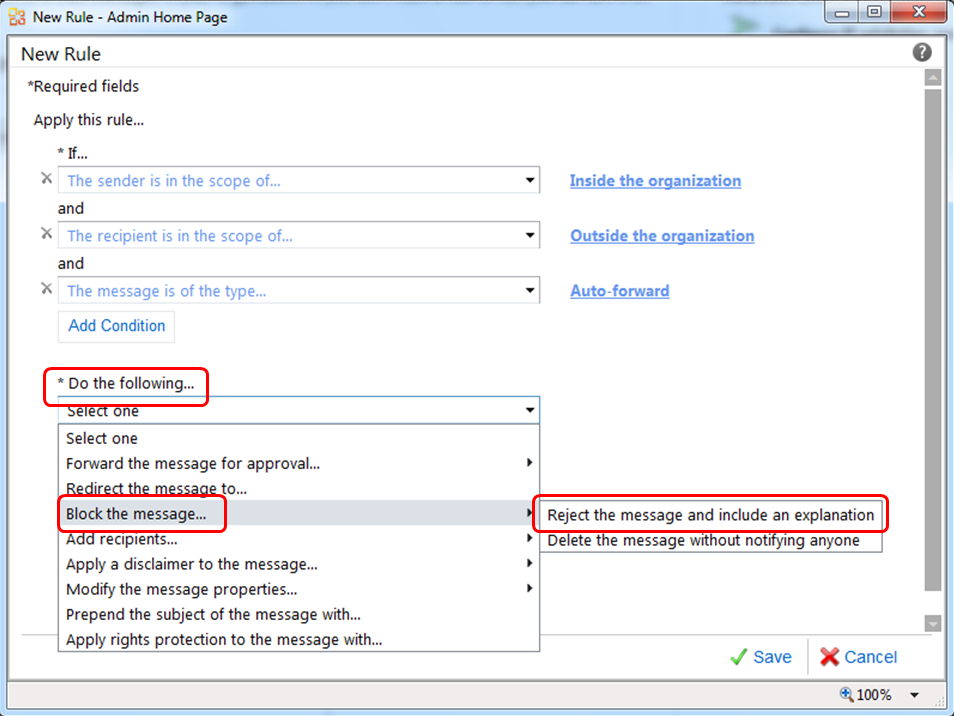
Finally set the Action to be taken if the above condition is met. Under the ”Do the following….” click ”Add Action”
Pick ”Block the message…” and then ”Reject the message and include an explanation”
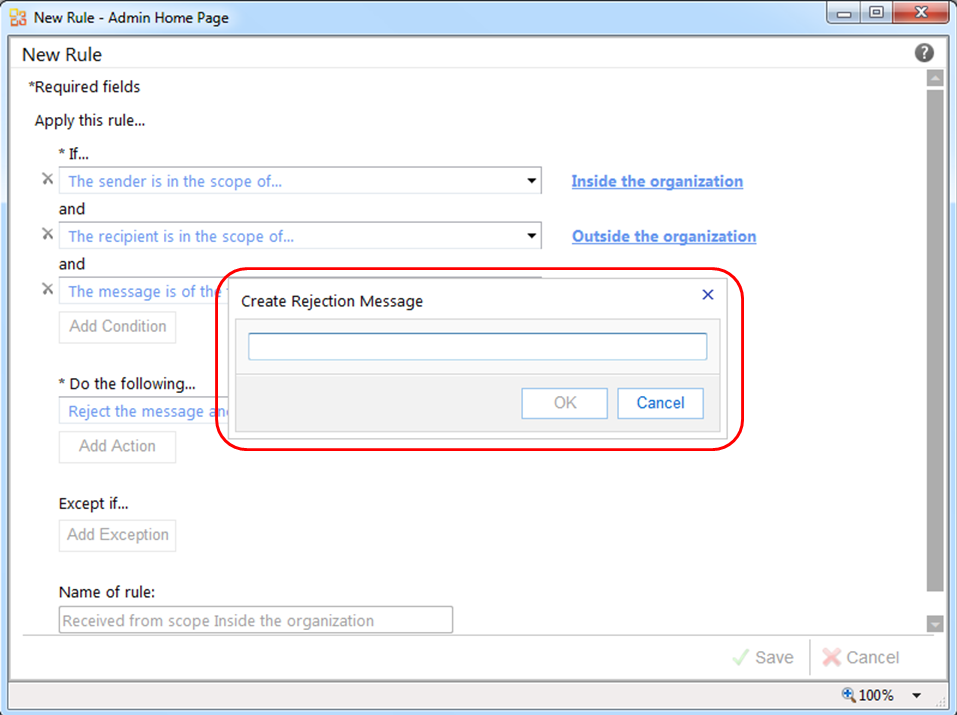
If the conditions are met and the message is rejected, a non-delivery report (NDR) is returned to the sender. You can create customized text, which appears in the NDR, to explain why a message was rejected (e.g. Auto-forwarding from internal to external is blocked)
Optional – name the rule
Click Save to save the rule.