CloudLink SecureVM leveraging the Azure Key Vault
Welcome to our first partner blog
Thus far we have introduced you to the Key Vault, gave you a deep dive on how to use it yourself, and finally explored how it can be used with SQL VMs to provide data protection. In this forth blog we’re going to cover CloudLink Secure VM, which now offers Azure Key Vault support. We’ll start with a tour of the product and then end with an interview of our partner. Because this topic has been covered before in Azure blogs, I lifted some of Bryon Surace’s excellent framing content (link below). Let’s dive in…
As many of you know, security and control is and important topic when deciding to run a workload in public IaaS. Who has the encryption keys? How can one verify if data is really encrypted? How is the data destroyed after use?
Security-conscious IT admins are well familiar with BitLocker which keeps physical machines protected by encrypting the entire disk drive. Instead of adding a proprietary cryptographic package to an OS, CloudLink leverages what is already there, relying on the support framework and update cycle of the OS rather than introducing its own. For Windows operating systems, SecureVM fully leverages BitLocker. For those who run Linux workloads in Azure, SecureVM also supports Linux native encryption packages.
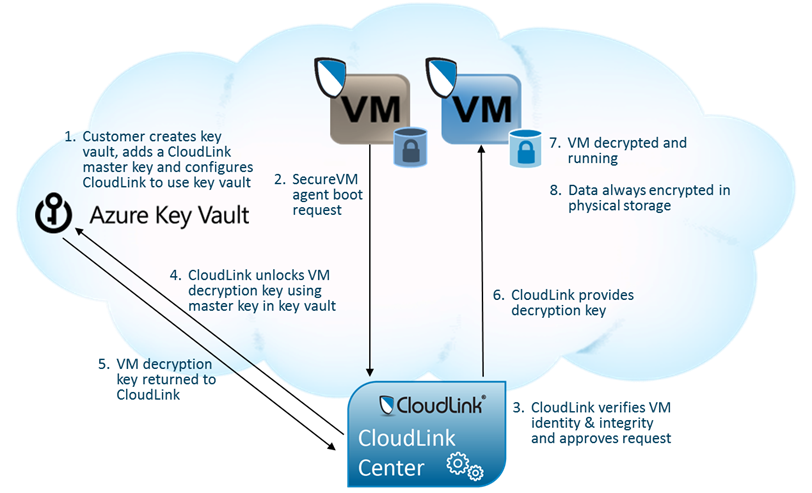
What makes CloudLink SecureVM particularly interesting is the fully automated boot from the encrypted volume in the cloud. Customers can configure their policy to pre-authorize some or all of their VMs to boot without any operator intervention. Unless of course CloudLink detects that something is fishy– like when a duplicate copy of a VM that is already marked as running is trying to obtain the key to boot again. Here is a high-level diagram explaining how CloudLink SecureVM integrates with Azure Key Vault.
When it comes to key management, CloudLink is following the same principle of avoiding burdening customers with extra software. Instead of using their own, CloudLink integrates with third-party key managers. CloudLink Center is a virtual appliance that customers use to manage and control the deployment of SecureVM. Whereas it can manage keys itself, it also integrates seamlessly with key management solutions such as RSA Data Protection Manager or can use Active Directory Server as a key store. CloudLink Centre can run in the private part of a hybrid cloud on Hyper-V, other virtualization platforms, or right here on Azure.
The SecureVM Agent is a small, lightweight software application that runs on each protected VM.
Deployment of CloudLink SecureVM is straightforward and simple:
Obtain and Deploy CloudLink Center. A preview version which supports Key Vault is available from CloudLink. Commercial releases of CloudLink Center may be deployed using Azure Marketplace or by obtaining the CloudLink Center VHD for on premise deployment in Hyper-V or other virtualization environments.
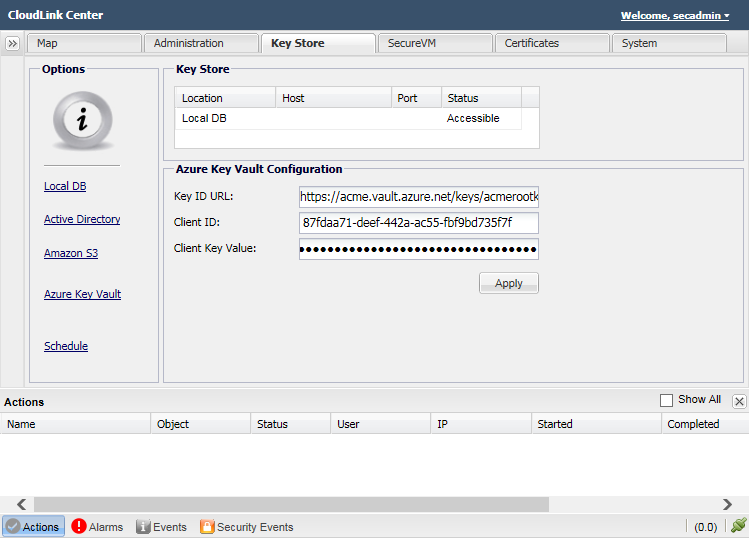
Configure CloudLink Center to use Key Vault
Deploy SecureVM agent manually on the VMs in Azure, or deploy the CloudLink SecureVM Agent extension using PowerShell or through the Azure portal. Alternatively, agent deployment can be done using AD group policy or Chef/Puppet scripts (msi package of SecureVM is contained within CloudLink Center and is accessible via a URL).
Configure IP addresses for VMs on which you plan to deploy SecureVM agent by adding them to the Accepted List in CloudLink Center in order to authorize the boot automatically or manually approve the boot request from SecureVM agents.
Manage and monitor secured VMs via CloudLink Center.
That’s it. Customers can now securely boot VMs using CloudLink SecureVM with their root of trust in Azure Key Vault. Furthermore, all data stored on the boot volume and any or all data volumes is encrypted by SecureVM using BitLocker.
CloudLink + SQL Server + Azure Key Vault
Earlier this week we posted a blog on integration of SQL Server with Key Vault. In it, we described how TDE can be deployed with Key Vault as an extensible key management provider. This adds an additional layer of security by taking keys used to encrypt database encryption keys out of SQL Server and placing them in Key Vault, realizing the scalability, performance, and highly availability offered by the service. In addition, Key Vault allows these keys to be generated and maintained in hardware, for an even higher level of protection.
Individually, CloudLink SecureVM and SQL Server offer compelling value for securing VMs and databases, respectively. Things get even better when they are used together:
SQL Server uses TDE tied to Key Vault to encrypt data as it is written to disk. However, SQL Server requires credentials to be able to access Key Vault. These credentials are very sensitive as malicious access to a vault could be used to gain access to the database. Here’s where CloudLink SecureVM comes in. Instead of storing Key Vault credentials on disk, they can be stored on a CloudLink SecureVM encrypted volume. This approach offers some notable benefits. First, sensitive Key Vault credentials are encrypted at rest. Second, SecureVM performs a number of checks on VMs prior to allowing them to boot, providing assurance that the SQL Server VM hasn’t been tampered with and is running in its expected environment.
CloudLink
Let’s learn a bit more about CloudLink from Tim Bramble, Director of Product Management…
Dan: Tim. Who is CloudLink? And tell us more about your beginnings and how you make Azure better.
Tim: CloudLink is an independent software vendor focused on delivering security solutions for virtualized and cloud environments. Although the company has been around for more than ten years, we began our cloud security journey four years ago with the introduction of our first product on the CloudLink Platform.
Today, CloudLink offers several products aimed at securing data at different levels of the virtualization stack. CloudLink SecureVSA is a virtual storage appliance which provides encryption at the storage infrastructure level. CloudLink SecureFILE offers policy-based application-aware file encryption that is completely transparent to users and Windows applications.
We introduced CloudLink SecureVM, our most recent addition to the platform, in July last year. We maintained close communication with the Azure team as we developed this product and Azure was the first cloud platform it supported. SecureVM offers encryption for VM boot and data volumes and allows VMs to boot only if they meet security policy defined by a CloudLink administrator. This provides Azure customers the assurance that their sensitive VMs and data are secure no matter where they are deployed across the hybrid cloud and that the customer remains in control of them at all times. Security is often cited as the top concern enterprises face when considering migrating workloads to the public cloud. SecureVM provides Azure customers a seamless way to address this concern.
Dan: How did Azure Key Vault help you make your product better?
Tim: Azure Key Vault is a very nice complement to SecureVM. It allows the keys SecureVM uses to encrypt VMs to be secured with root-of-trust keys it generates and stores. Since Azure Key Vault keys are non-exportable and, optionally, generated and stored in hardware, customers gain confidence that their VMs and data remain secure with high-assurance key management.
Dan: How hard was it to modify your application to use Azure Key Vault?
Tim: Integration with Azure Key Vault was very straight-forward. We were engaged with the Azure Key Vault development team early on and had the opportunity to provide feedback as the offering developed. The Azure Key Vault REST APIs are well structured and were easily integrated into our product.
Most of the integration work involved structuring CloudLink Center (CloudLink SecureVM’s management virtual appliance) to work with keys generated and stored in Azure Key Vault and having CloudLink Center authenticate correctly to Azure Key Vault. The Azure Active Directory Authentication Library (ADAL) made authentication easy. In addition, Microsoft supplied a wealth of PowerShell scripts which provide useful functions and examples of how to use the APIs.
Dan: Besides the links we provide below, how should people learn more or contact you?
Tim: We encourage people to visit our web site for more information on SecureVM for Azure and our other products. CloudLink SecureVM can be purchased and deployed directly from Azure Marketplace. In addition, we can help people get started with a trial. We are available at 866-356-4060 or info@cloudlinktech.com to provide more information and answer any questions.
Dan: Thanks Tim.
Tim: Thanks Dan. And thanks to the Azure Key Vault team for your wonderful partnership. Together we are making it easier for our mutual Azure customers to migrate workloads to Azure!
Ok, that’s it. Here are a few relevant links:
- Encrypting Azure Virtual Machines with CloudLink SecureVM
- Azure virtual machine encryption – making data security easy to buy, deploy and manage
- Hybrid Multi-cloud Security, now with Microsoft Azure Key Vault
- Azure Virtual Machine Disk Encryption using CloudLink
- CloudLink SecureVM for Microsoft Azure (VIDEO)
- Deploying CloudLink via the Azure Portal (VIDEO)
As usual, thanks for your support!
Dan (twitter) on behalf of the Azure Key Vault Team
Please take a moment to send us feedback , join our advisory board , and/or visit our forum