Error While Configuring WAP–The Underlying Connection Was Closed
We have seen a couple of these issues this week when running the Web Application Proxy wizard to complete an install. I am pretty sure we will see quite a few more of these so I thought I would write up a quick blog on the issue.
Problem
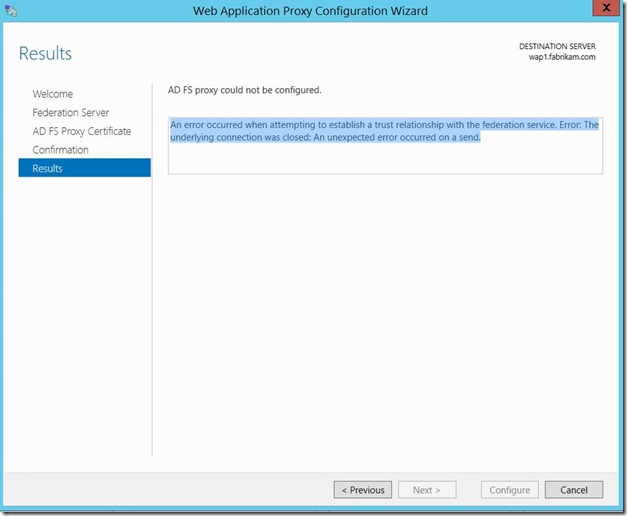
After installing the role for Web Application Proxy you are trying to finish the configuration wizard but you encounter the below error.
“An error occurred when attempting to establish a trust relationship with the federation service. Error: The underlying connection was closed: An unexpected error occurred on a send.”
Figure 1 shows the error we see in the wizard.
Fig. 1
Data Gathering and Analysis
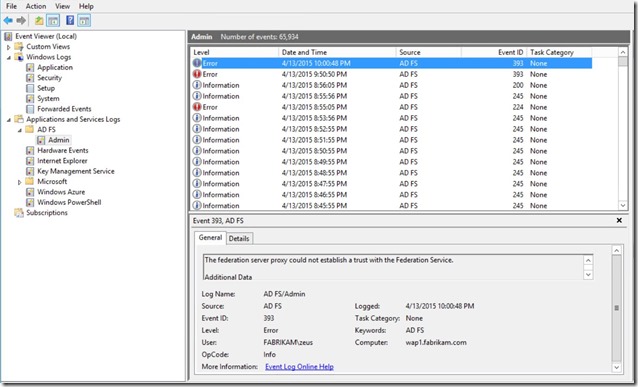
It was not immediately obvious what was causing this error so the first place I looked for more information was in the Event Viewer. Under the ADFS Admin events you may find an Event ID 393. The details do not tell us much more than the error in the wizard.
Fig. 2
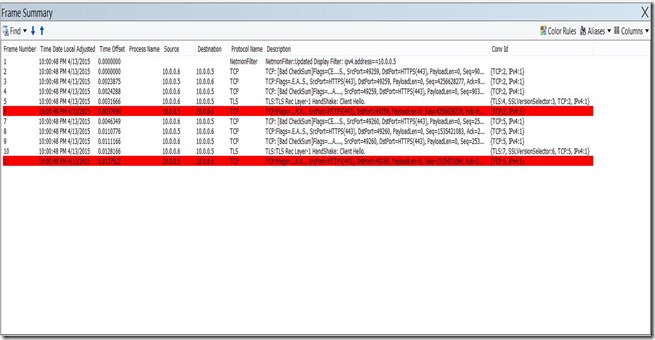
I wanted to see what was happening on the wire so I set up Netmon 3.4 to capture the network trace and filtered it to see the traffic destined for the IP address of the ADFS Server. In this case it was 10.0.0.5. You would also want to take a trace from the ADFS server to make sure that the traffic is truly making it there.
We can see in Figure 3 that right after the Client Hello in the trace, the ADFS Server resets the connection.
Fig. 3
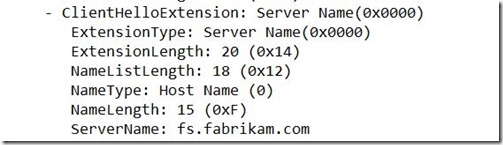
Drilling down into the Client Hello packet we find an extension called “Server Name”
Fig. 4
As we can see the server name is fs.fabrikam.com
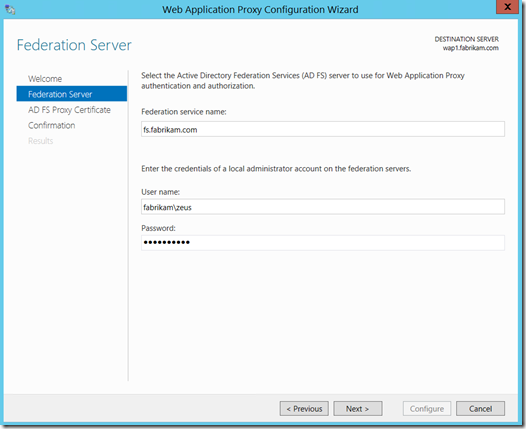
The server name in the trace was what was put in the WAP configuration wizard during the second step (Figure 5).
Fig. 5
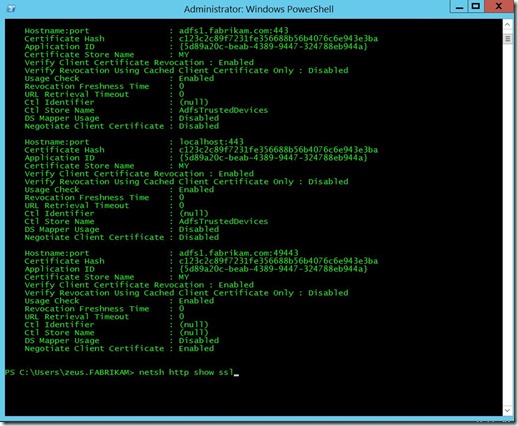
We should compare this to the bindings in ADFS. From an administrative command prompt on the ADFS Server run the command netsh http show ssl
Figure 6 shows the results of the netsh command.
Fig. 6
As we can see the bindings to port 443 do not match what was in the Server Name of the network trace.
Resolution
When planning your ADFS infrastructure always keep in mind what you want your external users to use as the FQDN. In this case the FQDN that was intended did not actually match the Federation Service name. I was able to easily remedy this by uninstalling the ADFS role and then reconfiguring it using the intended external FQDN as the Federation Service name. In the example above I would reconfigure it as fs.fabrikam.com. The Web Application configuration wizard will then complete successfully.
Note: If the information contained here was useful please let me know in the comments below. Also, if there are any corrections needed or you would like to see future content on a particular subject please let me know that as well. Thanks!