Building a Web Application Proxy Test Lab in Azure
This is Part 3 in an ongoing series that will help you take advantage of Azure by showing you how you can utilize it to test different products before deciding to roll them out.
Part 1 Creating a Test Lab for Free in Azure
Part 2 Configuring Your First VM in Azure
In Part 2 of the series I walked you through creating your first VM in Azure and we gave it the Active Directory Domain Services role and it is the only Domain Controller in your new domain. In this article I will walk you through installing Active Directory Certificate Services on your DC, installing a new server that will be your Active Directory Federation Services Server, and installing a third server that will hold the Web Application Proxy (WAP) role. Once those are complete we will publish the IIS Server that is running on your Domain Controller. External clients will be able to access it through WAP.
Install the Active Directory Certificate Services Role on your DC
The reason for doing this is twofold . First, certificates are required for some of the aspects of the lab. The second reason is that doing this will also install Internet Information Server (IIS) on your domain controller which we will publish to the outside world with WAP.
To get started installing Active Directory Certificate Services:
1. Log in to the Azure Management Portal at https://manage.windowsazure.com
2. Choose your domain controller and from the Dashboard click on “Connect”. Log in to the RDP session with your Administrator credentials.
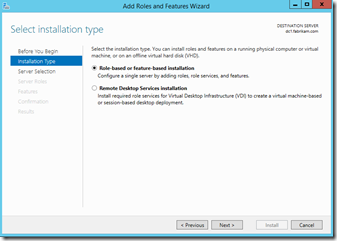
3. In Server Manager launch the “Add Roles and Features” Wizard.
4. Choose to do a “Role-based or feature-based installation. ”
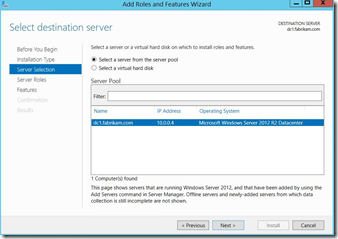
5. Select the DC in the Server Selection dialog.
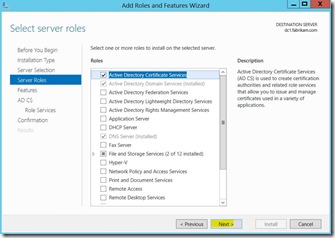
6.) Choose “Active Directory Certificate Services” and click “Next.”
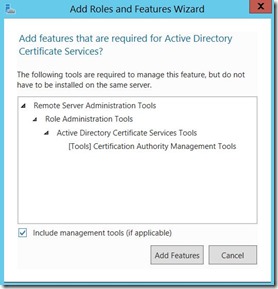
7.) Click “Add Features. ”
8. Click “Next.”
9. Click “Next.”
10. Again click “Next.”
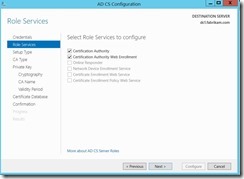
11. At Select Role Services choose “Certification Authority” and “Certification Authority Web Enrollment. ”
12. Click “Next.”
13. Accept the defaults and click “Next”
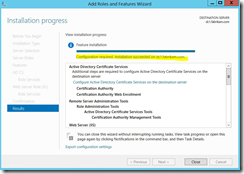
14. At the confirmation click “Install. ”
15. After the installation has succeeded click on the message “Configuration required. ”
16. Specify the credentials that will be used.
17. Click “Next.”
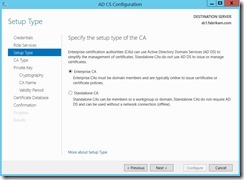
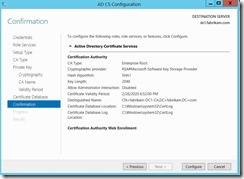
18. Choose “Enterprise CA. ”
19. Choose “Root CA. ”
20. Choose to “Create a new private key. ”
21. Accept the default cryptographic options and click “Next.”
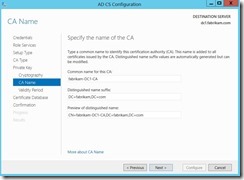
22. Leave whatever is the default at “Specify the name of the CA. ”
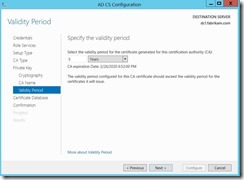
23. Leave it at a 5 year validity period and click “Next.”
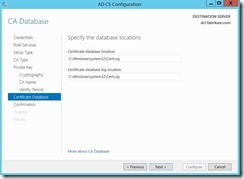
24. Accept default locations for CA Database and click “Next.”
25. At Confirmation screen click “Configure. ”
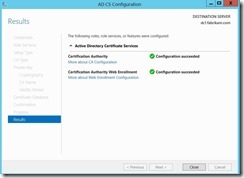
26. After you are notified that the roles were successfully installed click “Close.”
Creating a Certificate Template
Now that you have ADCS installed we will need to create a Certificate Template that will allow Computers to request a new certificate and allow the Private Key to be exported.
To do this you will need to:
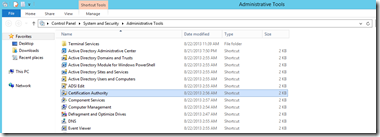
1. Launch the Certification Authority management console from your Administrative Tools group.
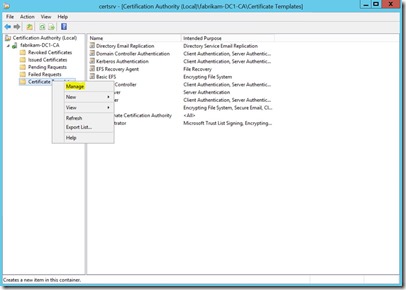
2. Highlight Certificate Templates and right-click, then choose “Manage.”
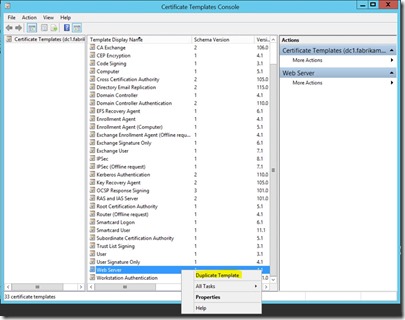
3. Highlight the Web Server template, right-click and then choose “Duplicate Template.”
4. On the General tab give you template a name meaningful to you.
5. On the Request Handling tab check the “Allow private key to be exported” box.
6. Under the Security tab add Domain Computers and Domain Controllers and then make sure they have the Enroll ability and then click “Apply.”
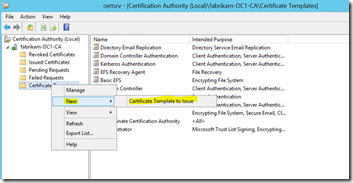
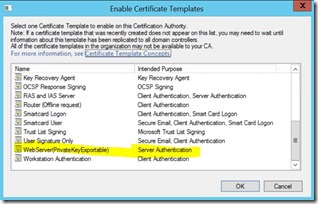
7. Highlight Certificate Templates, right-click on it and choose New, then “Certificate Template to Issue. ”
8. Choose the template you configured earlier and click “OK. ”
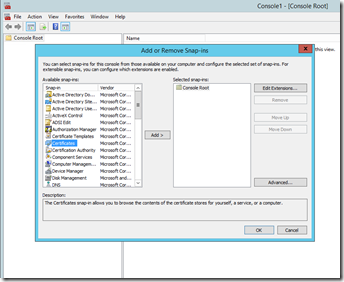
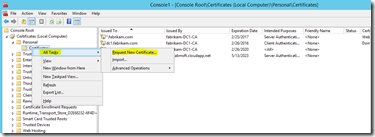
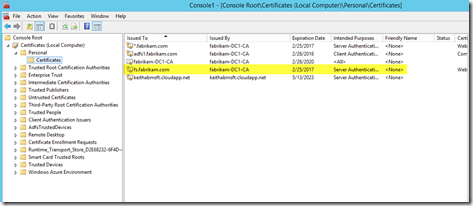
9. Open an MMC and add the Certificate snap-in. Click “OK. ”
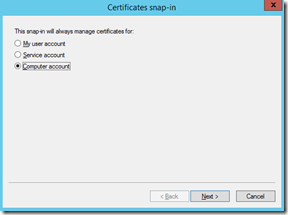
10. Choose “Computer Account.”
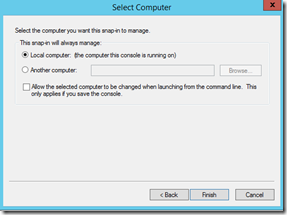
11. Select the Local computer and click “Finish”, then “OK. ”
12. Expand the Personal branch and highlight Certificates, right-click on “All Tasks”, then “Request New” Certificate.
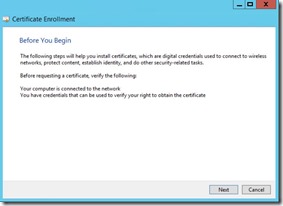
13. The Certificate Enrollment Wizard will launch. Click “Next.”
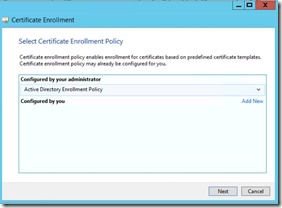
14. Highlight Active Directory Enrollment Policy and click “Next.”
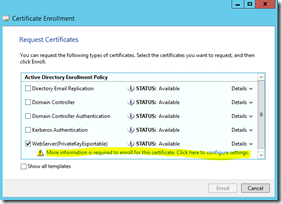
15. Check the box next to the template you configured and then click on the “More information is required to enroll for this certificate. ”
16. On the Subject Tab click on the Type dropdown box and choose Common Name and under value put in a wildcard asterisk followed by your domain name. So mine would be *.fabrikam.com and then click “Add. ”
17. Click “Apply. ”
18. Now click “Enroll. ”
19. You should get a message that is succeeded.
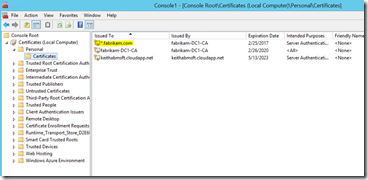
20. You should now have a Wildcard certificate for your domain installed in your Certificate Store and you will be able to export that certificate with the private key when we need it later.
Create and Configure Your ADFS Server
I will assume that you are somewhat familiar with creating a machine and that you followed Part 2 of this series.
To get started creating the ADFS Server:
1. While logged in to the Azure Management Portal click on “Virtual Machines” and then create a new Virtual Machine.
2. From the Gallery pick Windows Server 2012 R2 Datacenter as the image you will use.
3. Under the “Virtual Machine Configuration” menu choose your name, the Tier you will be using, the size of the VM, the name you used as administrator when you configured your DC, and the password.
4. Choose your existing cloud service (needs to be the same one where you DC is located) and use the same Storage Account which was used for your DC.
5. Provision the machine and wait until the status in the portal says “Running.”
6. Connect to the new machine and log in with your administrator credentials.
7. I found the easiest way to add the computer to the domain is to open PowerShell as an Administrator and use the command Add-Computer –DomainName fabrikam.com (Note: If you did not use fabrikam.com as your domain substitute your own domain name in).
8. You will be prompted for your domain admin credentials and then you will need to restart after it is completed.
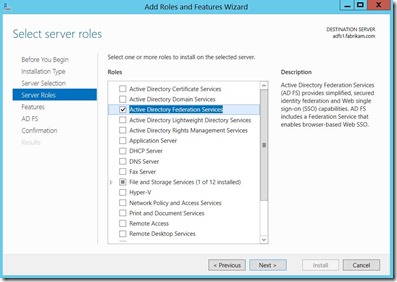
9. After the machine has been restarted it is now a member of the domain and we will add the Active Directory Federation Services role using the Add Roles and Features Wizard.
10. Click Next at every choice and just accept all the defaults.
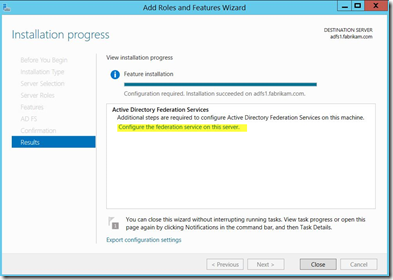
11. After feature is installed you will need to configure the service.
12. Before finalizing the configuration of the ADFS role you should request a certificate that will be used by ADFS.
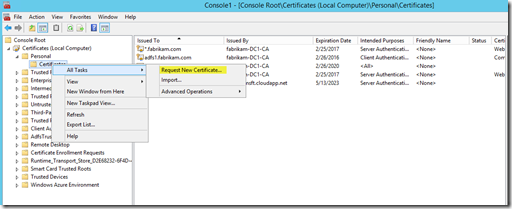
13. Open an MMC and add the Certificates Snap-in (Local Computer).
14. Expand the Personal branch and right-click on “Certificates”, choose “All Tasks”, then “Request New Certificate. ”
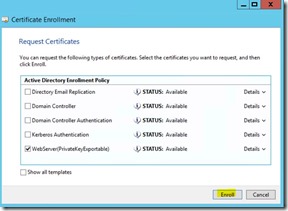
15. This will start the Certificate Enrollment Wizard. Click “Next” , leave the Active Directory Enrollment Policy selected and click “Next” .
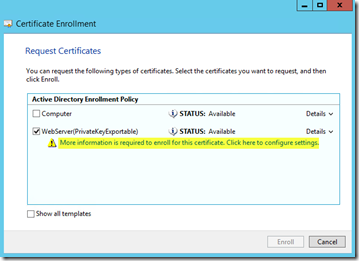
16. Put a check next to WebServer(PrivateKeyExportable) which was the template you created earlier. You will then need to click on the “More information is required to enroll for this certificate. Click here to configure settings. ”
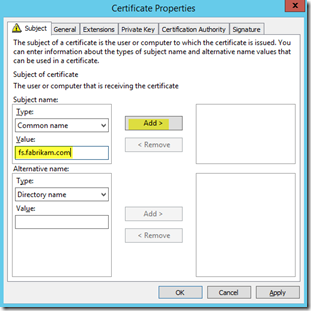
17. Under the Type drop down box choose common name, type in whatever you want to call your Federation Server. You can use the actual server name or deviate from that. I chose fs.fabrikam.com. Click “Add. ”
18. Your new CN will appear on the right hand side and then click “Apply. ”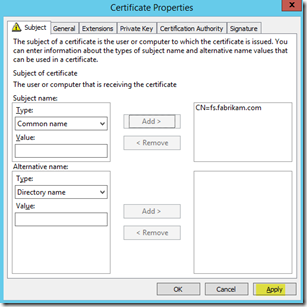
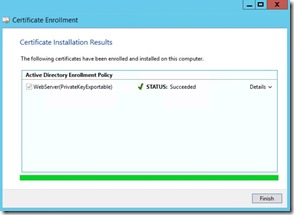
19. Enrollment should succeed and you should now see the certificate you requested in your Personal Certificates branch.
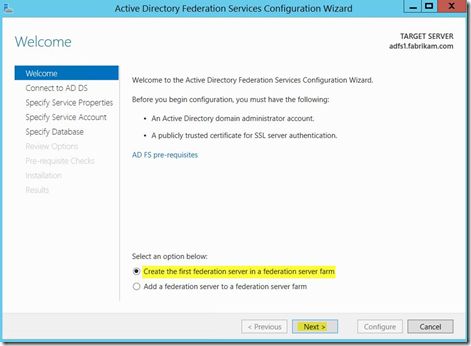
20. Go back to your Add Roles and Feature Wizard and click on “Configure the federation service on this server” . This will start the Active Directory Federation Services Configuration Wizard. Leave “Create the first federation server in a federation server farm” as the choice and click “Next.”
21. At the next step just specify the current user as the account you want to use to perform the federation service configuration. Click “Next.”
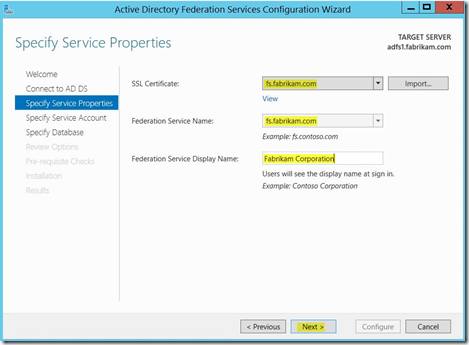
22. You will now choose the certificate you created earlier, give your Federation Service a name, give it a Display Name, and choose “Next.”
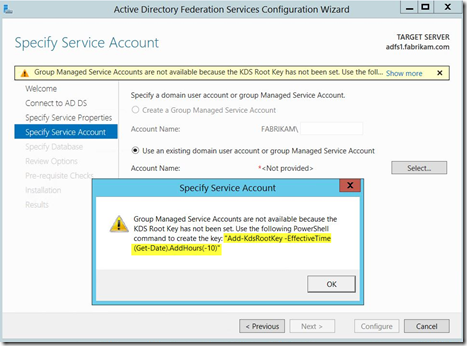
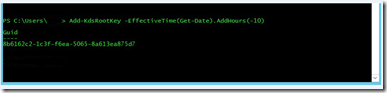
23. The next step will let you know that Group Managed Service Accounts are not available because the KDS Root Key has not been set. It will give you the PowerShell command that you need to run. Click OK to acknowledge it.
24. Open an Administrator PowerShell Command window and then run the command.
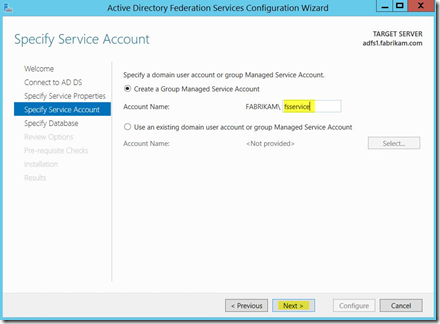
25. Now specify the Group Managed Service Account that you want created and click “Next.”
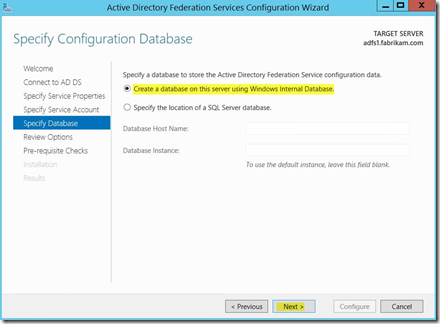
26. Leave the choice “Create a database on this server using Windows Internal Database” and click “Next.”
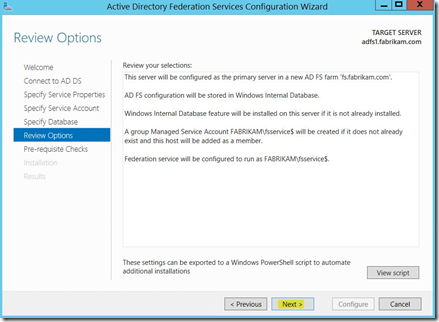
27. At the Review Options screen click “Next.”
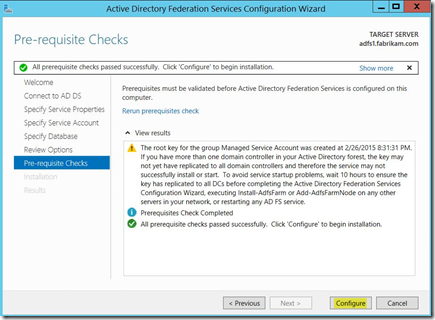
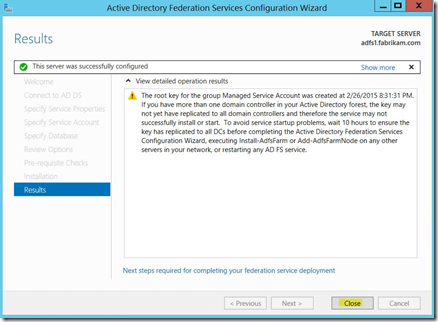
28. Assuming you did everything correctly you should get a message that All Prerequisites checks passed. Click “Configure.”
29. You should get a Results screen that tells you “This server was successfully configured”. Click “Close. ”
Congratulations! You now have an ADFS Server in your Azure test lab.
Create and Configure Your Web Application Proxy Server
Again I will assume at this point that you are familiar with creating a new virtual machine in Azure. In your Azure Management Portal create a new virtual machine that will be your WAP Server. After it has been created you will need to connect to it via RDP.
To get started creating the Web Application Server:
1.) Add your new server to the domain and reboot it.
2.) Export the wildcard certificate you created earlier on your Domain Controller and copy the file over to your new WAP Server. Import the wildcard certificate into the Certificate Store (Local Computer) under the Personal Certificates branch.
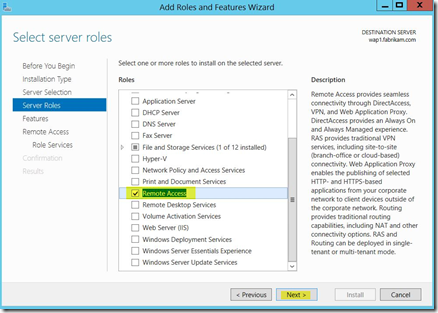
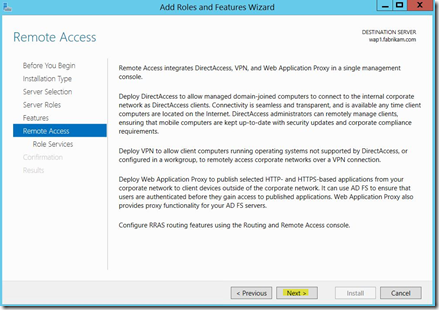
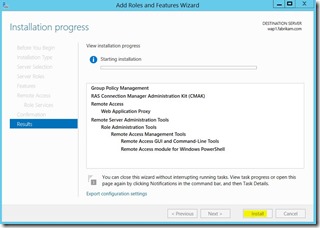
3.) Start the Add Roles and Features Wizard on the WAP Server. Once you get to the Server Roles section put a check box next to Remote Access and click “Next.”
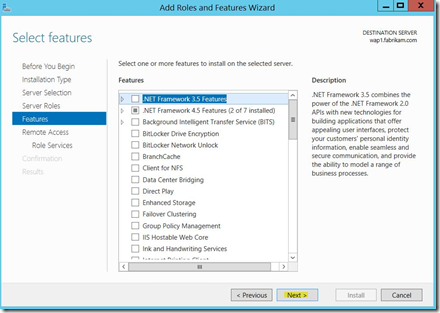
4. Click “Next” at the Select Features screen.
5. Click “Next.”
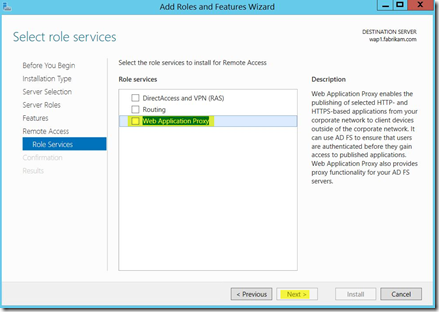
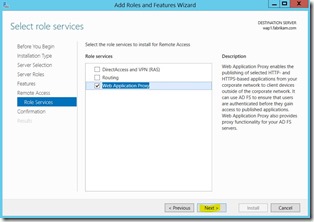
6. At the Select Role Services put a check box next to Web Application Proxy and click “Next.”
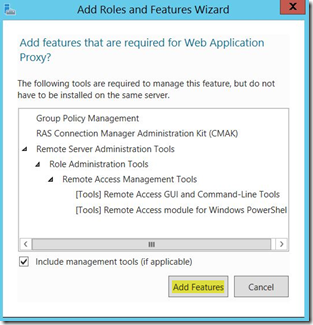
7. Click “Add Features. ”
8. Click “Next.”
9. Click “Install.”
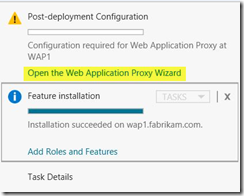
10. After the install succeeds you will need to click “Open the Web Application Proxy Wizard” to finish the configuration.
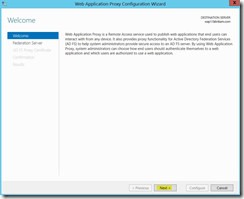
11. Click “Next” at the Welcome screen.
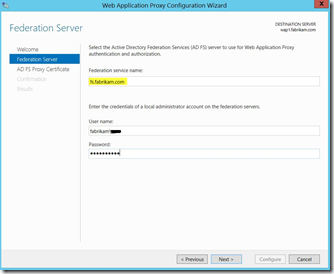
12. Select your Federation Service Name and credentials. (Note: Since my federation service names differs from the actual name of the ADFS server, I had to either add a HOSTS name entry or create a CNAME in DNS so that the WAP Server knows how to resolve the FQDN of fs.fabrikam.com ).
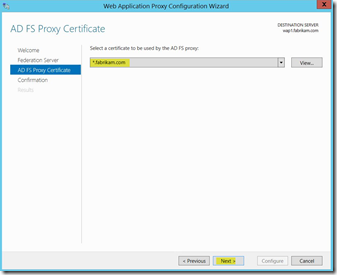
13. Now we select the wildcard certificate that was imported earlier and click “Next” .
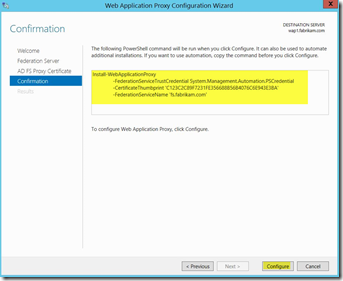
14. The next screen will show you the PowerShell command that will be run under the covers. Click “Configure.”
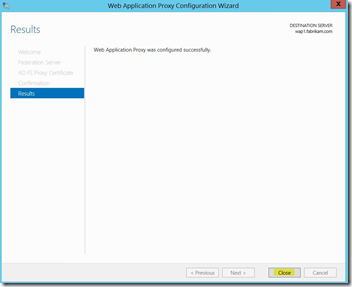
15. If all went right you should get a message that the configuration was successful. Click “Close. ”
Congratulations! Web Application Proxy is now installed on your server.
Configuring WAP to Publish Your First Application
We are now going to configure your WAP Server to publish IIS which is running on your Domain Controller. This is just a very basic rule but demonstrates how to publish something from your Azure virtual machine domain to the outside world.
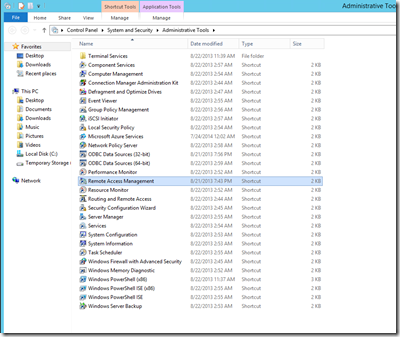
1. From your Administrative Tools program group double-click on Remote Access Management.
2. Click “Next” at the Welcome screen.
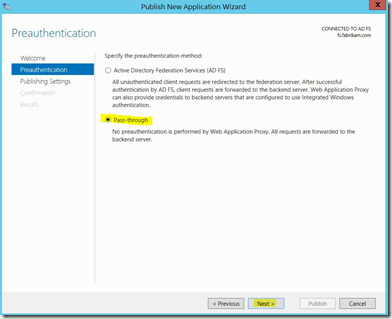
3. Choose “Pass-through” as the authentication method and click “Next.”
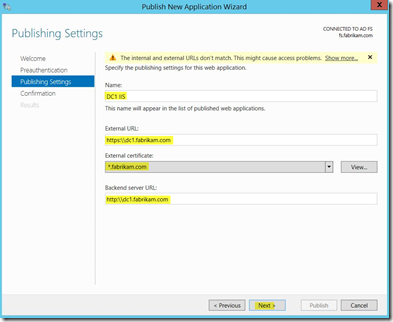
4. Call it anything you like in the Name dialog. The External URL will be what external clients type into their browser to access the application and should be prefaced by HTTPS. Choose the Wildcard certificate you imported previously. The Backend Server URL will be used by WAP to proxy the request. In the lab we created this should be the FQDN of your domain controller prefaced by HTTP. So in my case it is http:\\dc1.fabrikam.com. You will get a Warning at the top but just ignore it. Click “Next” .
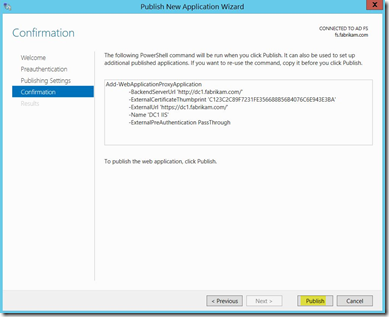
5. At the Confirmation screen click “Publish.”
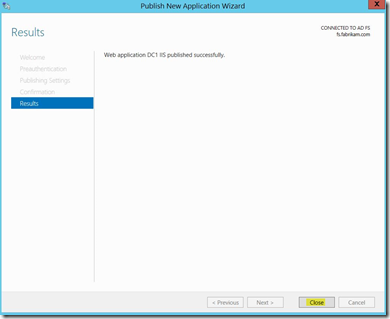
6. If all went right you should get a message that your application was published successfully. You can close the wizard.
7. You should see your application listed in the Remote Access Management console.
Allowing Access From the Outside World
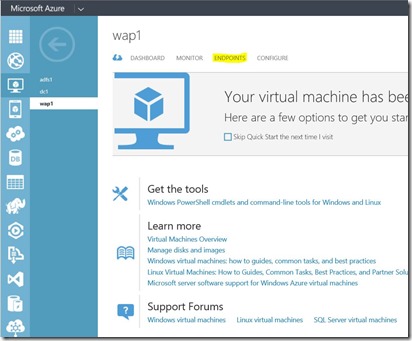
Before you can actually access your published application externally you will need to create an Endpoint in Azure to allow the HTTPS traffic to be forwarded to your WAP Server.
1. To do this go to your Azure Management Portal, highlight your WAP virtual machine, and click on “Endpoints” at the top.
2. Azure will show you what you currently have in the way of service endpoints. You will notice that PowerShell is there and so is Remote Desktop. Click “Add (+)” at the bottom of the screen.
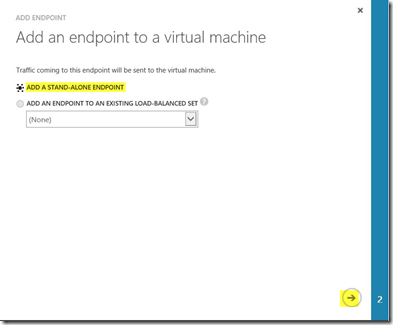
3. Choose to “Add a Stand-Alone Endpoint” and then click the arrow in the bottom right hand corner to move to the next screen.
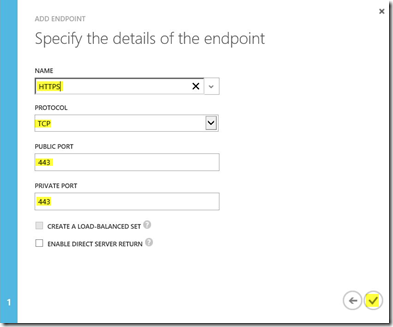
4. In the drop down box for Name choose HTTPS and Protocol TCP. Public and Private Port will both be 443. Click the checkbox to complete.
5. Your endpoints will be updated and should reflect the change.
Accessing From An External Client
The final step will be testing access from a client not located in Azure. You will need to add an entry to your clients HOSTS file so that it will be able to resolve the FQDN of both your Domain Controller and your Federation Service Name correctly. You can find the IP address that will be used in the hosts file by clicking on your Virtual Machines Dashboard and looking along the right hand column. There will be an IP address underneath the Public Virtual IP (VIP) Address section. So in my case I added host entries for fs.fabrikam.com and dc1.fabrikam.com to resolve to my Public IP. (Note: Since no authentication is being done at this time the fs.fabrikam.com entry is not really needed but I am putting it in there for future applications that will need it.)
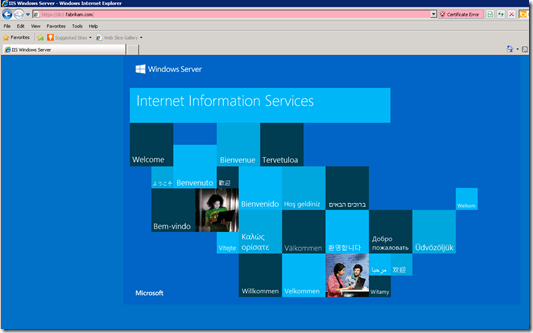
Once that is done you can test access to your IIS Server. (Note: You will get a warning about not trusting the certificate and that is to be expected unless you install the Root CA from your DC in the certificate store on your client. You can safely ignore it and choose to continue.)
If you have done everything right you should see the IIS landing page.
Conclusion
I know I have covered a lot in this article and I hope it was valuable to you. Many of you may not have needed the detailed screenshots but I wanted to include them for those that did. I will be continuing this series by building out other machines that will be needed in typical test labs. Please keep in mind that you pay for what you use in Azure. To minimize my costs I only leave my Domain Controller running when I am not actively testing or troubleshooting. By shutting down your other machines through the Azure Management Portal you will not be incurring expenses for them while they sit idle.
Cheers!
Note: If the information contained here was useful please let me know in the comments below. Also, if there are any corrections needed or you would like to see future content on a particular subject please let me know that as well. Thanks!