Setting up an OWA Redirect in Forefront TMG 2010 - the Easy Way
One of the most common requests we see is for assistance setting up a redirect in either ISA 2006 or Forefront TMG 2010. Administrators of ISA/TMG want this so they don't have to tell all of their external clients to preface the URL with https and also to append it with either /exchange or /owa. They want their users to simply type in the Fully Qualified Domain Name of their Outlook Web Access application and it just works.
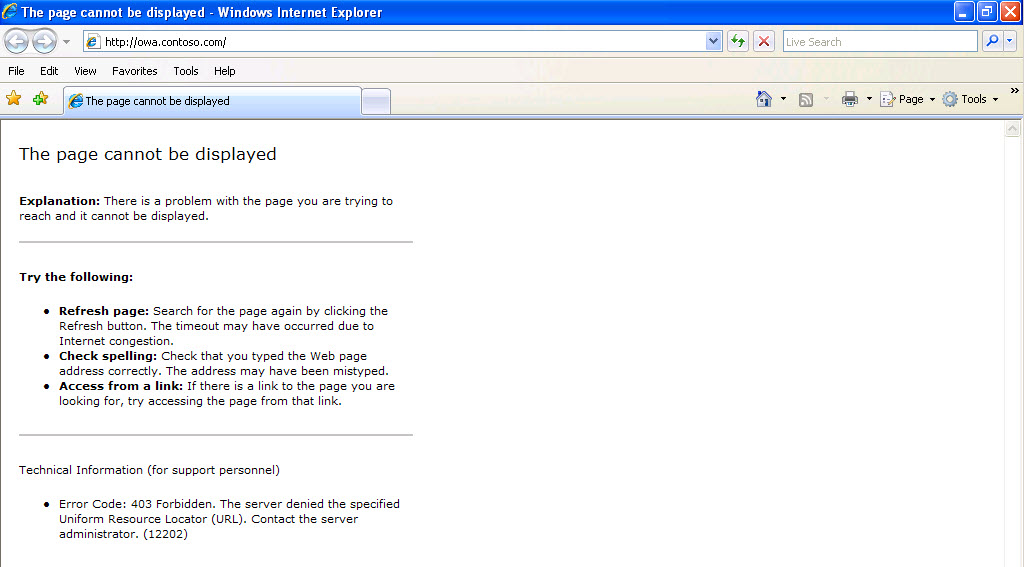
In my test lab I am publishing my Exchange 2007 Outlook Web Access at owa.contoso.com. If I do not have a redirect in place and simply type owa.contoso.com in my browser and hit enter I get the error "The page cannot be displayed." This is no good! (Figure 1)
Figure 1.
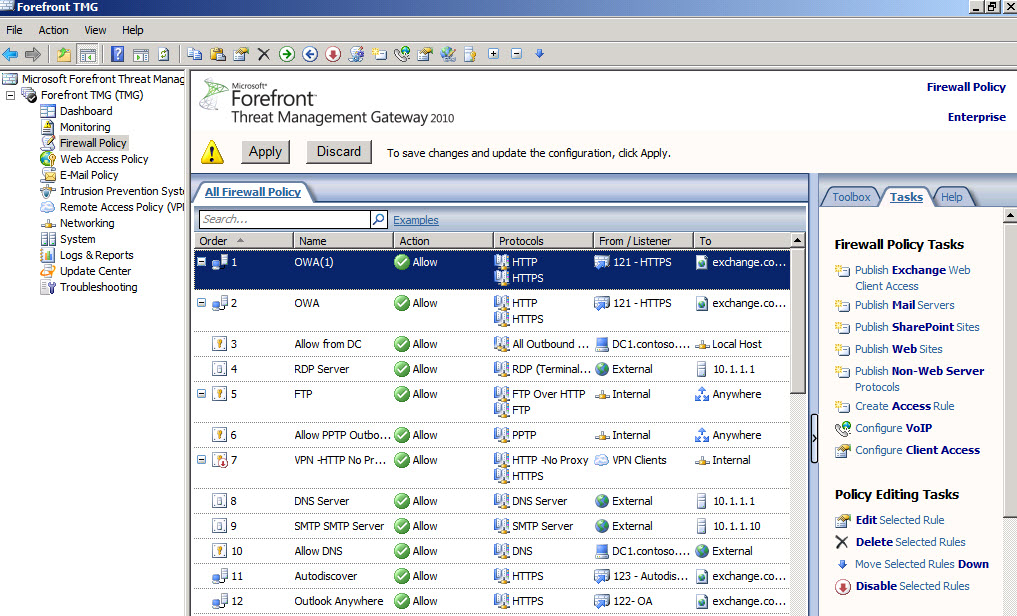
I am assuming you already have the rule created that publishes Outlook Web Access. To create the redirect simply go into your ISA or TMG MMC and highlight the rule in your Firewall Policy. Right-click on the rule and choose Copy. Now highlight the rule again, right-click and choose Paste. It will take whatever the rule was called and create a new one appending it with (1). (Figure 2)
Figure 2.
Before applying the changes you want to edit a few properties in the rule. Under the General tab rename it something meaningful. I renamed mine simply OWA Redirect. Next click on the Action tab. Here you will choose Deny and then click the "Redirect HTTP requests to this Web page:" and you will enter the full path, in this case it would be https://owa.contoso.com/owa (Figure 3)
Figure 3.
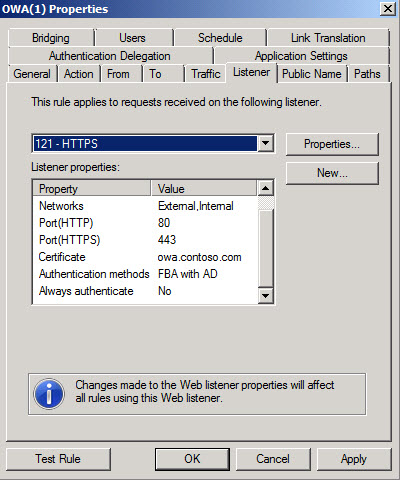
Next click on the Listener tab. It is important that your listener is listening on port 80 for the HTTP request. It is also important that the area that says "Always Authenticate" says No. You don't want the Listener to require authentication. (Figure 4)
Figure 4.
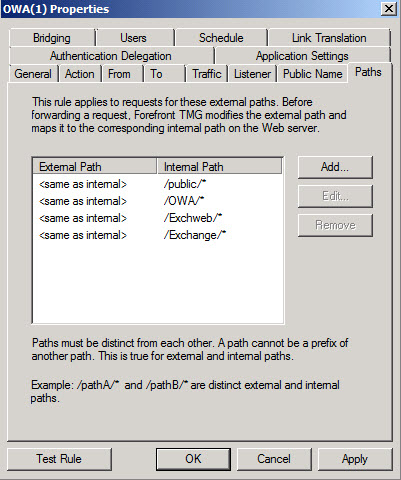
Next go to your Paths tab. We will need to make some changes here. The typical rule for Exchange 2007 would be publishing /public/*, /owa/*, /exchweb/*, and /exchange/*. (Figure 5)
Figure 5.
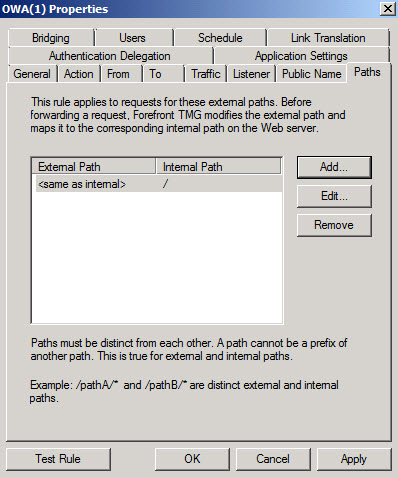
We need to remove all of these paths and add only "/" without the quotes. Do not make the mistake of adding "/*" because that says everything from the root on down. (Figure 6)
Figure 6.
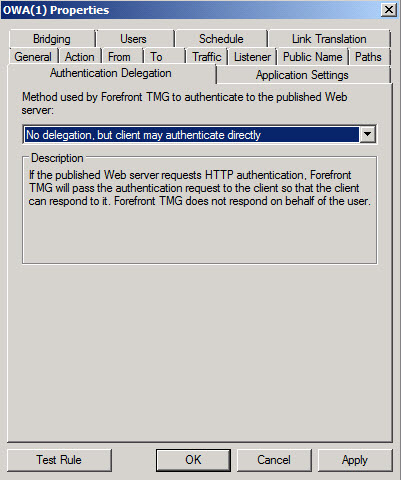
Now click on the Authentication Delegation tab and choose "No delegation, but client may authenticate directly" in the dropdown box. (Figure 7)
Figure 7.
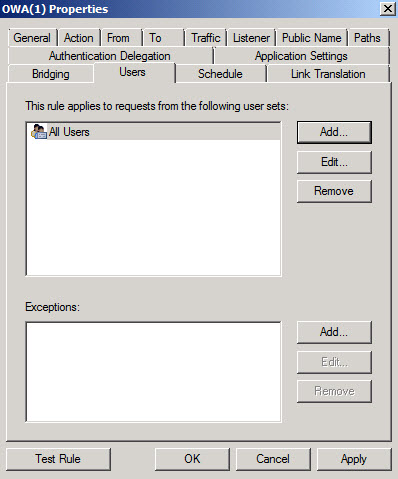
Next click on the Users tab, remove All Authenticated Users and replace it with All Users. (Figure 8)
Figure 8.
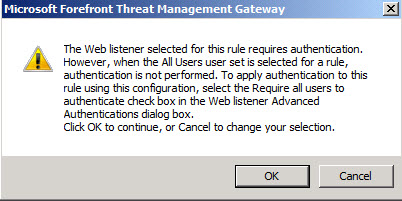
Now click Apply and you will receive a warning (Figure 9). Ignore the warning and say OK.
Figure 9.
In the ISA/TMG MMC move your new Redirect rule to just below your OWA publishing rule. It will be evaluated because the request will be to the root directory which was covered when we added "/" to the path.
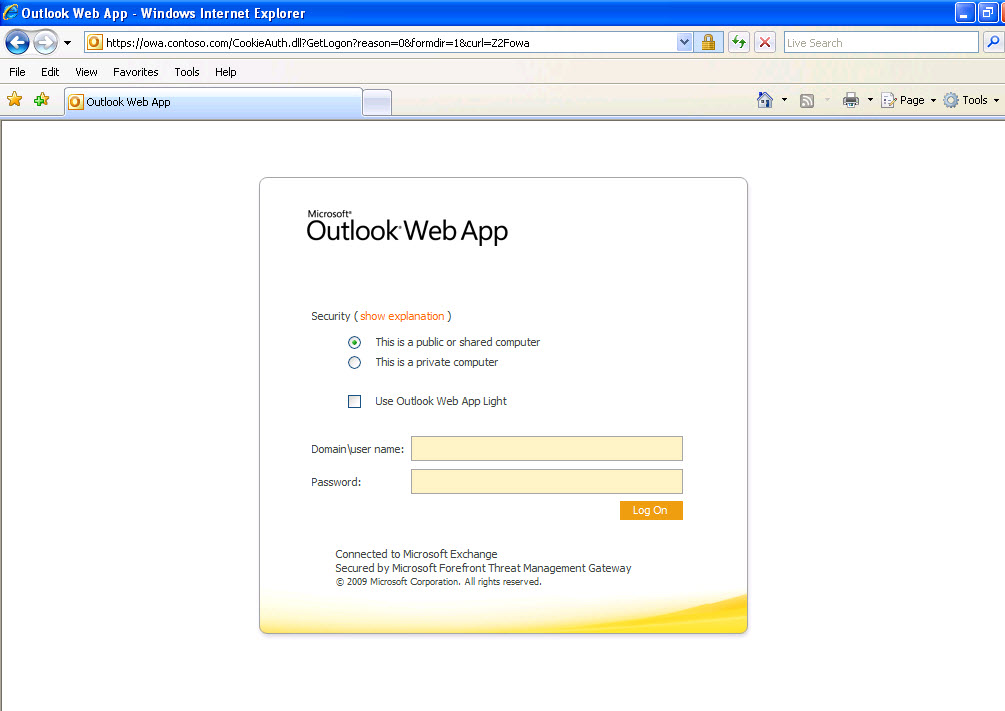
Now test using an external client by simply typing in the FQDN of your OWA Rule and you should be redirected automatically and greeted with the Forms Based login page present by ISA/TMG. (Figure 10)
Figure 10.