How to Build Your ADFS Lab on Server 2012 Part 1
Hey y’all Mark and Tom here with a series we think you guys will dig. I feel like half of our blog posts are building a lab of some kind. We love our labs in PFE. That’s how most of us learn. Set up a lab, play around with the technology, and get it configured. It’s fun for everyone! Right?! We are starting to get more and more customer requests around people just starting out with ADFS. We thought we’d get everyone starting by walking you through how to setup your very own ADFS Lab.
Initial Setup
First you have to have an AD Forest set up. If you don’t have that check out a blog post by Doug Gabbard. https://blogs.technet.com/b/askpfeplat/archive/2013/01/30/no-excuses-you-need-a-lab-for-active-directory-2012.aspx
We are going to assume you have the following setup before you dive in.
- Active Directory Forest
- ADFS Server running Windows Server 2012
- Domain Joined
- Valid network configuration
Creating a Service Account
ADFS runs on a service account. This will need to be created ahead of time before doing the install.
Some warnings about this service account:
#1: Don’t mess around with or set the Service Principal Names (SPN) on any accounts related to ADFS. The ADFS configuration wizard will automatically configure the correct Service Principal Names (SPN) on this service account so don’t worry about this configuring the SPN.
#2: Ensure that the physical computer name of any of the ADFS servers in the farm don’t match the ADFS service name. If you plan to call your ADFS service name sts.markmorow.com, ensure that none of the servers in the farm have this same actual computer name. If you do this, you immediately have a duplicate SPN scenario, which will prevent Kerberos authentication to this ADFS farm. Here is more information on duplicate SPN’s:
https://blogs.technet.com/b/askpfeplat/archive/2012/03/29/the-411-on-the-kdc-11-events.aspx
For my environment test environment I created an account called ADFS_SVC and my server is called ADFS01Corp.
Getting Certificates
As Jasmin talked about at https://blogs.technet.com/b/askpfeplat/archive/2013/07/22/faq-on-adfs-part-1.aspx we need three certificates on ADFS. But really, we only need to have 1 setup to do the install. We need a Server Communications (SSL) certificate. We got three choices.
1.) You could use an publically signed external cert. Since this is TEST you may not want to pay for one.
2.) You can generate a self-signed cert. This has a great walkthrough on doing that. https://www.sslshopper.com/article-how-to-create-a-self-signed-certificate-in-iis-7.html
3.) You can request a certificate from your internal PKI. You do have an internal PKI set up right??? https://social.technet.microsoft.com/wiki/contents/articles/4797.ad-cs-and-pki-step-by-steps-labs-walkthroughs-howto-and-examples.aspx
I picked #3. I had spent a few hours before and setup a PKI infrastructure in my lab. The walkthroughs are very easy to follow. Don’t be scared.
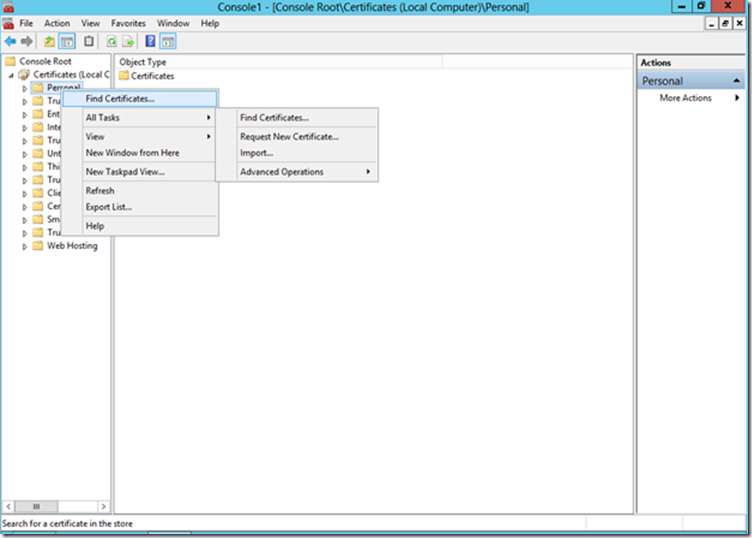
First we need to request a certificate. We do that by going to the MMC snap-in, adding certificates for the Computer Account, Local Computer, right click Personal, go to All Tasks, Request New Certificate.
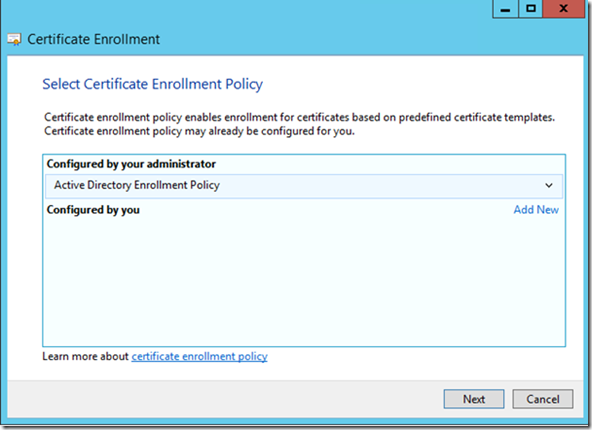
We are going to select our Active Directory Enrollment Policy and click Next
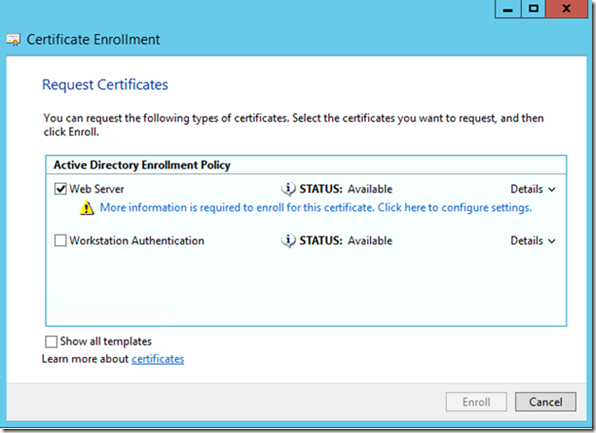
If you don’t see Web Server make sure your Web Server template is published and you have rights to it. As we can see here we need some additional configuration information. Click on the blue text.
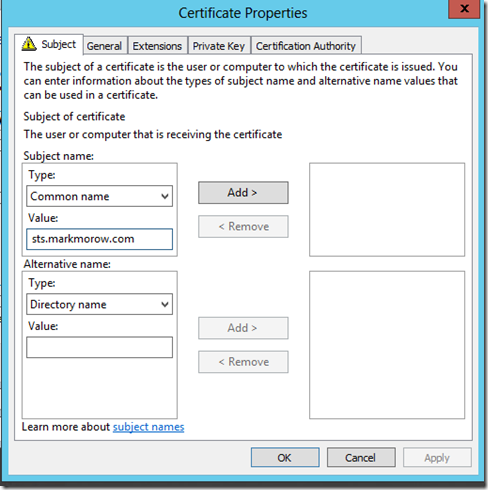
Our certificate name is going to be STS.yourdomain.com. Obviously configure this to fit your needs. Click ok and finish the cert process.
Installing ADFS
Ok now that we got all our pre-reqs in order let’s do the actually install of ADFS.
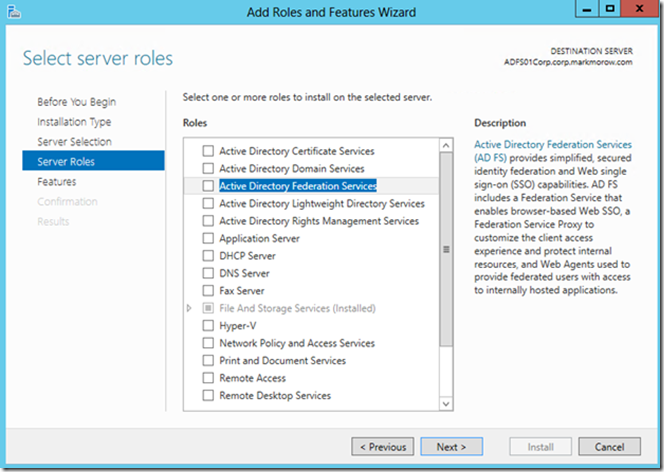
You’ll want to start by going to Server Manager and adding the ADFS role. Click Next
It will add any other additional roles and features it needs. Click Add Features and next through these new features until you hit the ADFS Role services.
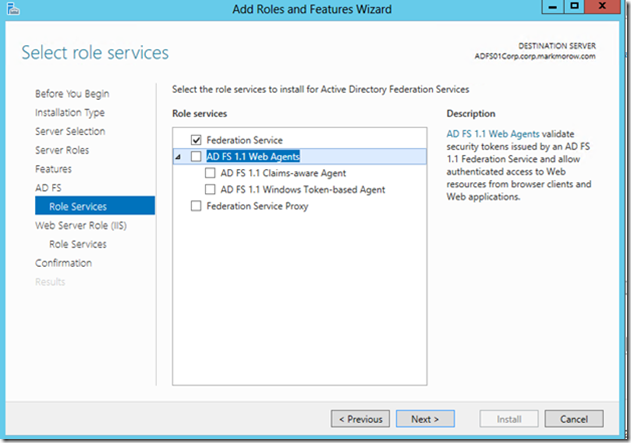
After you next your way a few default screens you’ll come up to this screen. We’ll come back later to an ADFS Proxy, but for now just leave the Federation Service checked. Hit next a few more times than Finish. Let the install finish.
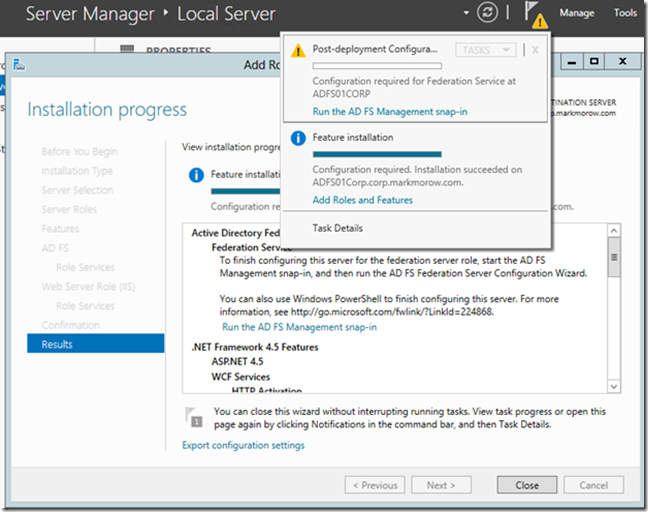
You should see a yellow exclamation point at the top right to let you know there is additional configuration requirements. Click “Run the AD FS Management snap-in”
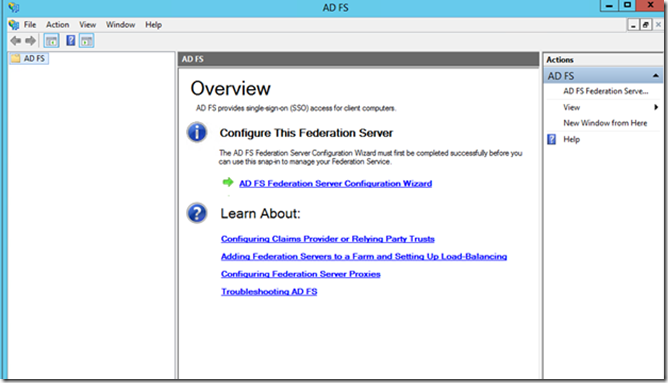
You’ll then get the ADFS Snap in to finish configuring. Click “ADFS Federation Server Configuration Wizard”
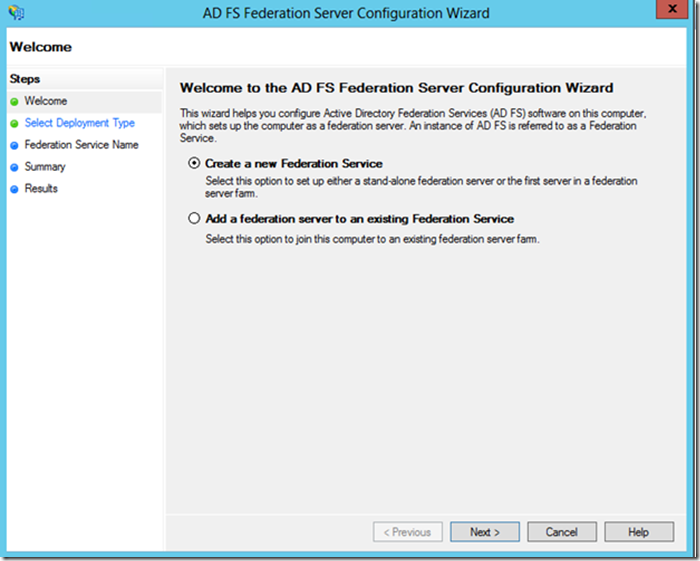
Since this is our first ADFS Server we are going to select “Create New Federation Service” and hit next.
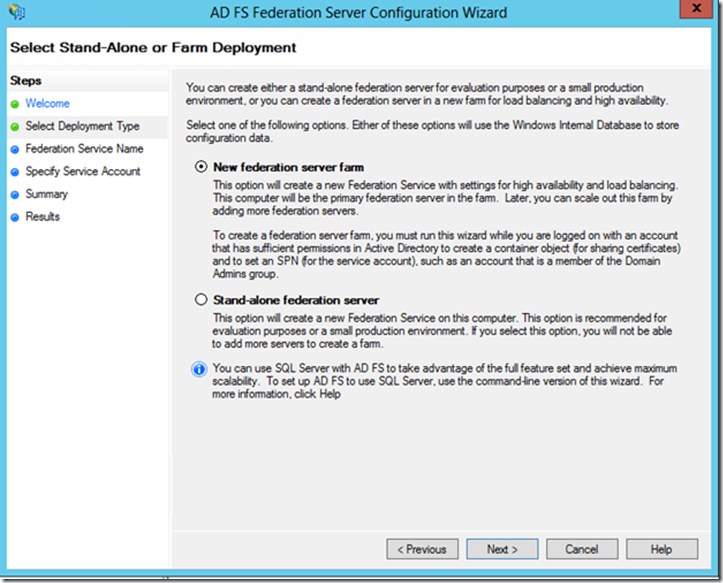
We’ll be creating a server farm of one. Click next.
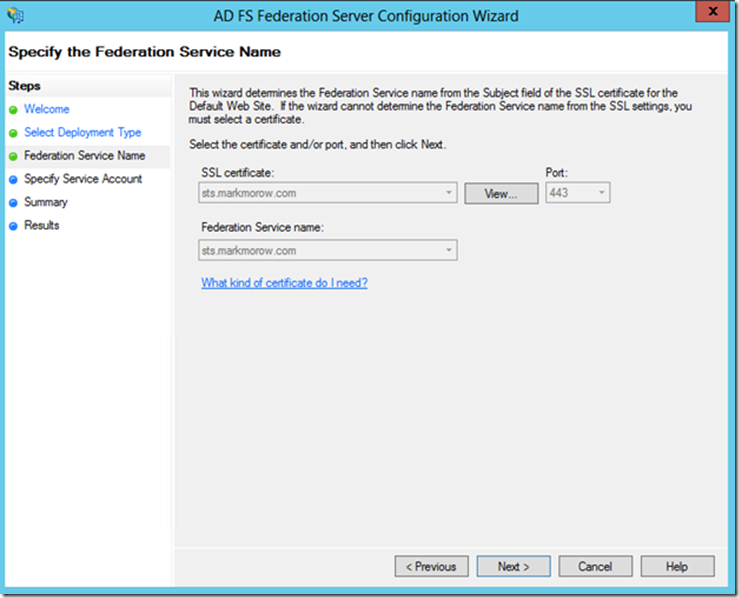
ADFS should automatically pick up the Server Certificate. We’ll click next.
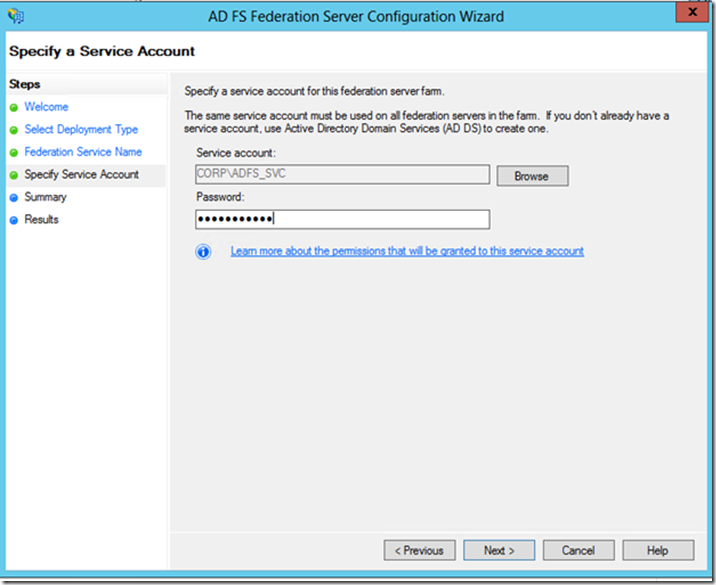
Input the service account we created earlier and click Next. The install should start.
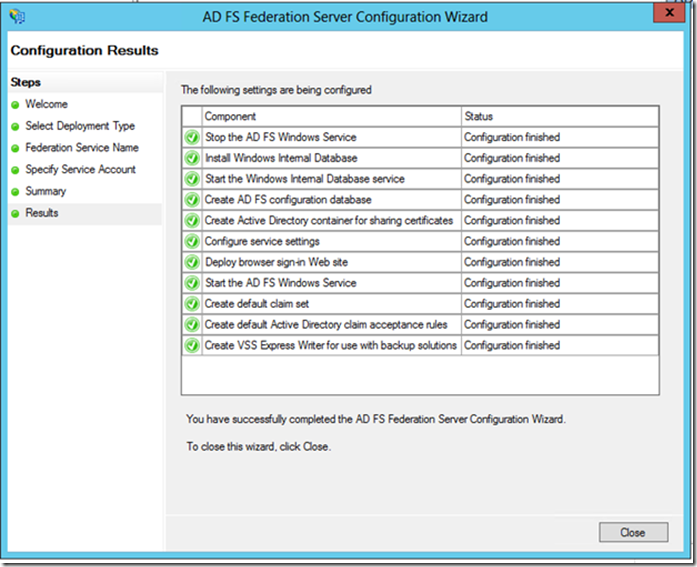
All done. We are now setup using the WID database. If you wanted to use a SQL database you would have to do the install from the command line. Check back for Part 2 on how to configure a relaying party and a web app to view claims.
Mark “Next, Next” Morowczynski, Tom “Finish” Moser