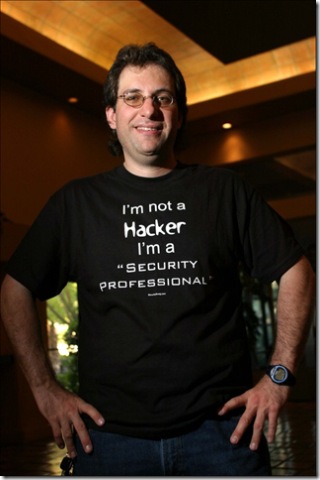
Mitnick and Me
Well, if you've been in the information security business for more than just a few months, you probably know who Kevin Mitnick is. In case you are just joining us, he's one of the most world renown, hacker-turned-security speaker. He even started Mitnick Security Consulting LLC, which I hope is doing quite well for him. He is also the author of two terrific books, the first of which is The Art of Deception: Understanding the Human Element of Security , which I consider to be probably the best book ever written on the topic of social engineering.
This past Friday (yes, Friday the 13th) I had the opportunity to partake in a seminar in which Kevin was the featured speaker. Despite some technical glitches (C'mon Kev....A Mac OSX with Windows emulator? That made me sad. I was soooo expecting a Ubuntu or Debian box. I can even get you a good deal on a Windows Vista O/S.) getting the Windows emulator to run, which is challenging in any case, Kevin pulled off a terrific and eye-opening presentation. As one who does this for a living, Kevin did a great job of holding our attention and keeping it engaging. Just a terrific job! As expected he spent the majority of his time explaining how it's the "human link" that is the weakest link in your security chain and the most exploitable. He even used himself as an example and discussed how he was able to use the power of persuasion to get the source code for a soon-to-be-released mobile phone back in the 1990s. As Kevin joked, "It was about that time that some people in Federal law enforcement were interested in speaking to me. I was not interested in speaking with them, however."
Now, one of the more disturbing live demos he presented, was using an Open Source VoIP solution that I know many have never seen. It's called Asterisk (yep....like the little star thing on the keyboard). It is a free IP based PBX, and is incredibly extensible. Now you may ask, why Kevin Mitnick chose to demonstrate this innocuous little application. I mean, he's supposed to be showing us a bunch of "31337 h4x0R" stuff, right? Well Mr. Security Pro, you need to take notes on this little item. There's a new risk in town and it's called "vishing". It's just little targeted phishing attack, where I send all of your bank customers a little email, that explains they need to call to verify their bank account number. When they do, and enter the bank account, SSN, username, Mother's maiden name, pet name, etc. like this. Meanwhile, our bad guy is sitting at his favorite coffee house/wireless ISP watching all of these numbers magically appear on his screen....multiple times (you did type it in to confirm your account number, like the vice prompt asked, correct?). I heard about this being a quickly rising threat from some of my buddies in law enforcement, but to see it in action was truly disturbing.
For more information on "vishing" check out the wonderful presentation delivered at BlackHat last year by Jay Schulman.
Finally, I'm going to try and get Kevin to join me for an interview on TechNet Radio, assuming we can get all the details and scheduling to work out. Should be pretty interesting! Keep checking back!