Terminal Services Gateway and Terminal Services Web Access using Hyper-V (Part 1)
So over the weekend, I found myself with a few spare hours, and got back to “playing with technology” – something I haven’t had a lot of time to focus on recently. What I ended up with was something which I classify mostly as “because I can”, but nonetheless (IMHO) pretty cool and dead useful! What I was impressed most of all with was the simplicity of it.
Of course, Hyper-V being my favourite technology, that had to be in the mix. The mission was to install a 64-bit Windows Server 2008 virtual machine under Hyper-V, running a Terminal Services gateway and web access with remote applications available on the Internet to manage Hyper-V. I used the beta version of Hyper-V which is present as part of Windows Server 2008 RTM (Release To Manufacturing)
Let’s see how simple it really was. (Please note, I work in the Hyper-V team. While I get by in many, if not most Microsoft server technologies, I am by no means an expert in configuring or administering Terminal Services, Active Directory Certificate Services, Exchange or ISA Server. Feel free to drop questions you may have my way, but I may have to redirect you if it’s out of my depth!)
On an extremely modest machine (Dual Core desktop, 2GB RAM with a couple of very average 80GB SATA disks), I installed Windows Server 2008 Enterprise Edition and used Server Manager to enable the Hyper-V role. (BTW, Windows Server 2008 RTM is became available to MSDN and Technet subscribers this week).
After the Hyper-V role was installed, I built a Uni-Processor (UP) virtual machine running Windows Server 2008 Enterprise Edition with 1GB RAM on a single VHD. I joined it to my test domain, gave it an appropriate name, assigned a static IP address, enabled remote desktop and created an administrative account (TSAdmin) in my test domain to manage the machine. Finally I made TSAdmin a member of the local administrators group on the Virtual Machine. Nothing complicated so far – all standard operating procedure to get a blank machine up and running and ready to start work on.
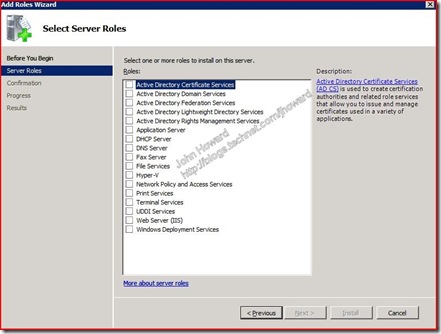
The first thing to do is to add the Terminal Services role using Server manager. Much like adding the Hyper-V role, this is a relatively simple wizard, and for most options in a simple configuration, the defaults are what you need.
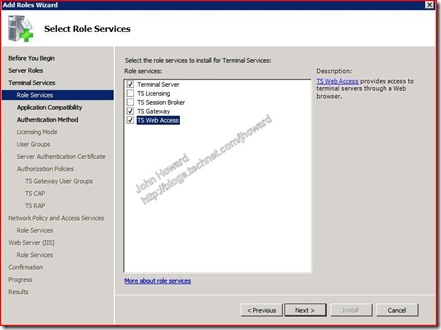
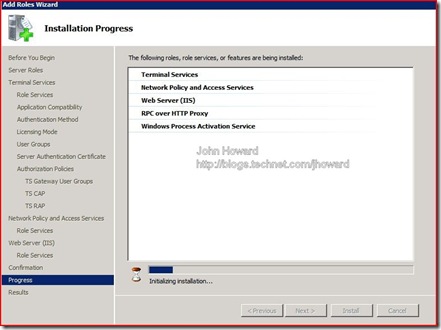
Click the Terminal Services checkbox and add the Terminal Server, TS Gateway and TS Web Access role service. You’ll note (and this is one thing I think is really quite cool about server manager), that you are prompted for the dependencies needed to make the TS Gateway and TS Web Access roles working correctly. No longer the need like there was in Windows Server 2003 when configuring things like Exchange and Outlook Web Access where you have to manually add all the dependencies such as RPC over HTTP proxy and IIS .
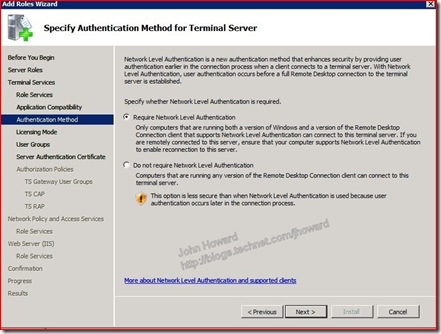
The first challenging question is the Authentication Method for Terminal Server. The answer really depends on which clients you are expecting to be connecting. In my case, it’s Vista SP1 clients, so there’s no need for me to allow computers running any version of Remote Desktop Connection client to be able to connect.
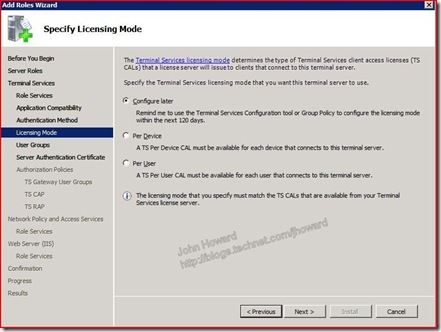
You are then asked for a licensing mode. By default, you have up to 120 days to configure this, and for this test, I just left it to remind me later.
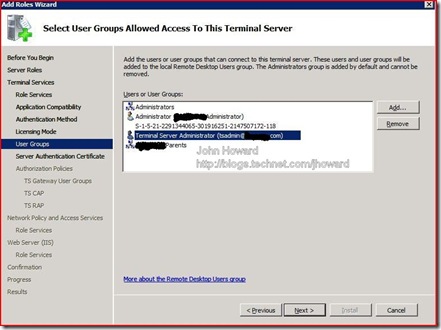
Next you are asked for the user groups allowed to access the server. In my case, I added the TSAdmin user account and the “Parents” domain group, which I’m a member of on my test domain.
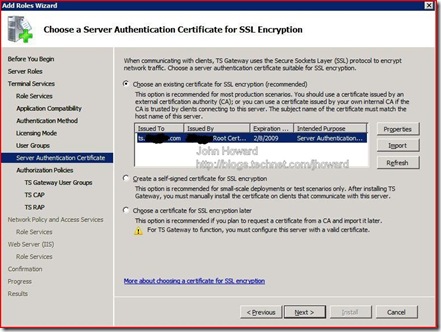
The next page of the wizard asks you to select a Server Authentication Certificate. As I have a Certificate Authority already setup on a Windows Server 2003 virtual machine, a certificate for Server Authentication was already available as part of joining the Virtual Machine to the domain, this was a simple choice. Note that you also have a choice of creating a self signed certificate for test scenarios such as this where a Certificate Authority is not available. I thought that was a really nice touch to include that option in the wizard from the Terminal Server team.
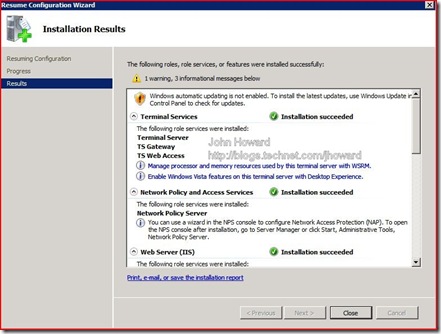
The next steps are to create appropriate policies. In a simple configuration, I allowed myself (obviously) access through the gateway, and to use the default “password only” option for the connection authorization policy (CAP). On the resource authorization policy step, I allowed users to be able to connect to any network resource (this is not the default). Under Network Policy and Access Services and Web Server (IIS), I just chose the defaults and clicked Next through the steps and allowed the role to be installed. That takes a minute or so for everything to complete.
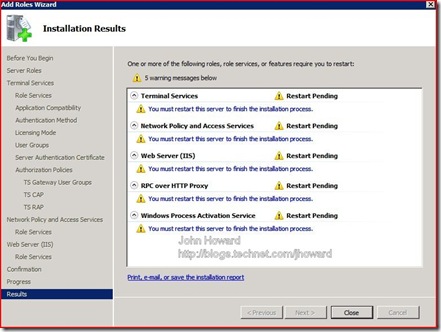
Finally, you must restart the (virtual) machine – do you know, that at this point, I’d forgotten the machine was a VM, not a physical machine
Server manager completes the role installation once the restart has been completed and you have logged on again. You’ll note I have a warning as I haven’t yet enabled Automatic Updates on this VM. Time to turn that on….
In part 2, I’ll look at the next steps, including one way of setting up ISA 2006 to provide a secure front end to the gateway.
Cheers,
John.