Ports Required for a Site System in DMZ in Configuration Manager
Overview:
I’m often setting up a site system (MP/DP/SUP) in a DMZ for internet based client management or for managing machines in the DMZ.
One of the more common questions around this scenario are the ports required between the Site Server (Internal) and the Site System (DMZ) .
All the ports for Configuration Manager 2012 are documented on TechNet here: https://technet.microsoft.com/en-us/library/hh427328.aspx but I will list the ports for a site system in the DMZ that host the following roles: management point, distribution point, software update point.
Use PortQryUI to perform the port checks: https://www.microsoft.com/en-us/download/details.aspx?id=24009
Minimizing the Risk:
When working with site system in a DMZ taking connections from the internet you want to reduce the amount of traffic that’s initiated from the site system in the DMZ to the site server.
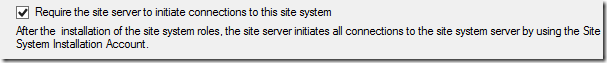
By default, site systems initiate connections to the site server to transfer data, which can be a security risk when the connection initiation is from an untrusted network to the trusted network. When site systems accept connections from the Internet or reside in an untrusted forest, configure the site system option Require the site server to initiate connections to this site system so that after the installation of the site system and any site system roles, all connections are initiated from the trusted network.
This option can be found in the wizard when you are setting up the new site system:
Ports Required:
When using the “Require the site server to initiate connections to this site system” option for the site system, you will only need the following ports opened:
Site Server (Internal) --> Site System (DMZ)
- Ports: TCP/UDP Port 135
- Protocol: RPC Endpoint Mapper
- Reason: Used for initiating WMI connections from the site server to the site system
Site Server (Internal) --> Site System (DMZ)
- Ports: TCP Ports 49152 – 65535
- Protocol: RPC
- Reason: Used for WMI connections from the site server to the site system
Site Server (Internal) --> Site System (DMZ)
- Ports: TCP Port 445
- Protocol: Server Message Block
- Reason: Used for the site server to push content to the distribution point
Site Server (Internal) --> Site System (DMZ)
- Ports: TCP Port (80 or 443 or 8530 or 8531) – it depends on the port you configure WSUS to use on the Site System in the DMZ
- Protocol: HTTP or HTTPS
- Reason: Used by the site server’s WSUS Configuration Component to connect to the WSUS server on the site system to configure the upstream server
Site System (DMZ) --> Software Update Point (Internal)
- Ports: TCP Port (80 or 443 or 8530 or 8531) – it depends on the port you configure WSUS to use on the software update point (Internal)
- Protocol: HTTP or HTTPS
- Reason: Used by the site systems (DMZ) server to sync it’s WSUS catalog with the Software Update Point (Internal) WSUS catalog
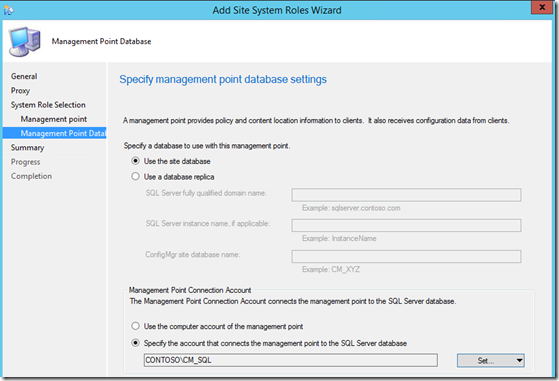
Site System (DMZ) --> SQL Server (Internal)
- Ports: TCP 1433 (Default unless SQL using custom port)
- Protocol: SQL over TCP
- Reason: Used for the management point in the DMZ to hit the site database (If the site server is not hosting the site database you will need to create to rule to the appropriate server) to receive information
Site System (Management Point - DMZ) --> Domain Controller (Internal)
- Ports: TCP/UDP 135,TCP 389, TCP 3268-3269, TCP 49152 – 65535
- Protocol: RPC Endpoint Mapper, LDAP, LDAP SSL, Global Catalog LDAP, Global Catalog LDAP SSL, RPC
- Reason: Allows the management point (DMZ) to authenticate to active directory so it can connect to the site database server using its computer account.
- Exception: If you use a domain user account for the management point connection account rather than the computer account of the management point (See screenshot), authentication can fallback to use NTLM rather than Kerberos if ports to an internal domain controller are not open. In this scenario, the site system would not need any ports open to an internal domain controllers.
Additional Information:
Configuration Manager requires each site system to be a member of an Active Directory domain so you cannot install a site system in a DMZ if the server is not joined to a domain.
You can install a site system in an untrusted domain. However, the site systems forest does not trust the forest the site server is in user based deployments are not supported. When no trust exists, only computer policies are supported.
More information about untrusted scenarios can be found here: https://technet.microsoft.com/en-us/library/dd8eb74e-3490-446e-b328-e67f3e85c779#Plan_Com_X_Forest
Disclaimer: The information on this site is provided "AS IS" with no warranties, confers no rights, and is not supported by the authors or Microsoft Corporation. Use of any included script samples are subject to the terms specified in the Terms of Use