ActiveSync clients are unable to authenticate with ISA Server/Forefront TMG using SecurID
Consider the following scenario:
- You are currently using ISA Server 2006 or Forefront TMG to publish your internal OWA server.
- You require SecurID authentication for external OWA clients.
- You have only one IP address bound to the external interface of the ISA server.
- You have successfully configured the ISA/TMG server as an Agent Host for the RSA Authentication Manager.
- The Web Listener, used to publish OWA, is configured for Forms Based Authentication using SecurID and has the correct Certificate bound.
Using the above configuration, your external OWA clients are able to successfully authenticate with ISA/TMG using their SecurID credentials and are able to connect to the internal OWA.
You’d like to publish ActiveSync:
Next, you’d like to configure ActiveSync publishing. It is not uncommon for many administrators to simply use the existing OWA Web Listener and Publishing rule to configure ActiveSync publishing. Certificate, IP address and external name registration limitations are the most common reasons for making use of the existing OWA rule and listener when adding ActiveSync publishing. Most of the time, this is not an issue. As long as the following basic criteria are met:
- ActiveSync clients use the same external server name as the OWA clients (i.e. owa company.com).
- ActiveSync clients have the trusted Root (and possibly Intermediate) certificate<s> installed.
- You have added the ‘Microsoft-Server-ActiveSync’ path to the OWA publishing rule.
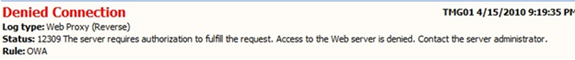
However, after meeting the above criteria, you may find that the external ActiveSync clients are unable to connect and ISA/TMG may deny the connection attempt with error 12309:
Explanation:
Forms based authentication cannot be used by the ActiveSync client. By default, when form-based authentication cannot be used with a specific client, ISA Server requires Basic authentication instead. This is commonly referred to as “Fallback to Basic”. ISA/TMG makes the determination to fallback to basic by examining the User-Agent string presented by the client. If the User-Agent string is not accepted, ISA will challenge the client for Basic Credentials instead. However, ‘fallback to basic’ is not applicable when using Forms Based Authentication with a Validation Method of ‘RSA SecurID’, therefore the ActiveSync client will fail to authenticate with the ISA/TMG server.
More Information:
For example, “Fallback to Basic” is applicable when the Forms Based Authentication validation method is ‘Windows (Active Directory)’. If the web listener is configured for Forms Based Authentication using the ‘Windows (Active Directory)’ validation method, ISA/TMG will “Fallback to Basic” and challenge the ActiveSync client for Basic credentials. The ActiveSync client will then provide Basic credentials to ISA/TMG. ISA/TMG will then validate the credentials and Delegate (provided the Publishing rules Delegation settings are set to Basic) the Basic credentials to the Exchange server.
Conclusion:
ISA/TMG is unable to authenticate ActiveSync clients when the Web Listener is configured with Forms Based Authentication with the RSA SecurID Validation method.
Possible solutions:
- If you require ISA/TMG to authenticate OWA clients with SecurID, but ActiveSync clients do not require SecurID authentication:
You must create a separate Web Listener, using a separate IP address with an authentication method other than RSA SecurID. Then create a new ‘ActiveSync’ Publishing rule using this separate Web Listener. - If you require SecurID authentication for both OWA clients and ActiveSync clients:
Remember that ISA/TMG can authenticate OWA clients but not ActiveSync clients using SecurID. For ActiveSync clients, you must create a separate Web Listener, using a separate IP address with an authentication method other than RSA SecurID. Then create a new ‘ActiveSync’ Publishing rule using this separate Web Listener. You must then install the latest “RSA Web Agent” software on the Exchange CAS server.
NOTE:
Please contact RSA support for details regarding the “RSA Web Agent” and how properly configure the “RSA Web Agent” software to authenticate ActiveSync client with SecurID.
Author
Richard Barker - Sr Security Support Escalation Engineer, Microsoft CSS Forefront Security Edge Team
Reviewer
Gabriel Koren, Forefront Security Edge Test Team