Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Intune Customer Success
URL
Copy
Options
Author
invalid author
Searching
# of articles
Labels
Clear
Clear selected
Accessibility
Administrative templates (ADMX)
Adobe
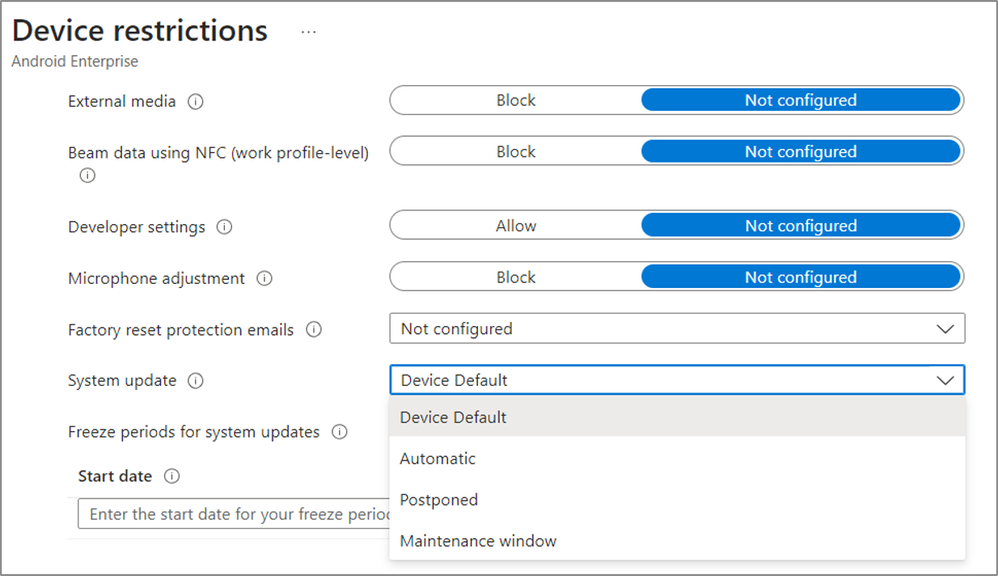
Android
Android Device Administrator
Android Enterprise
Android Work profile
Apple
Apple Configurator
Applications
Attack Surface Reduction (ASR)
Automated Device Enrollment (ADE)
BitLocker
BitLocker Series
Box Cloud Content Management (CCM)
Box for EMM
Certificates
Compliance
Conditional Access
Configuration as Code (CAC)
Configuration Manager
Day Zero
Diagnostics
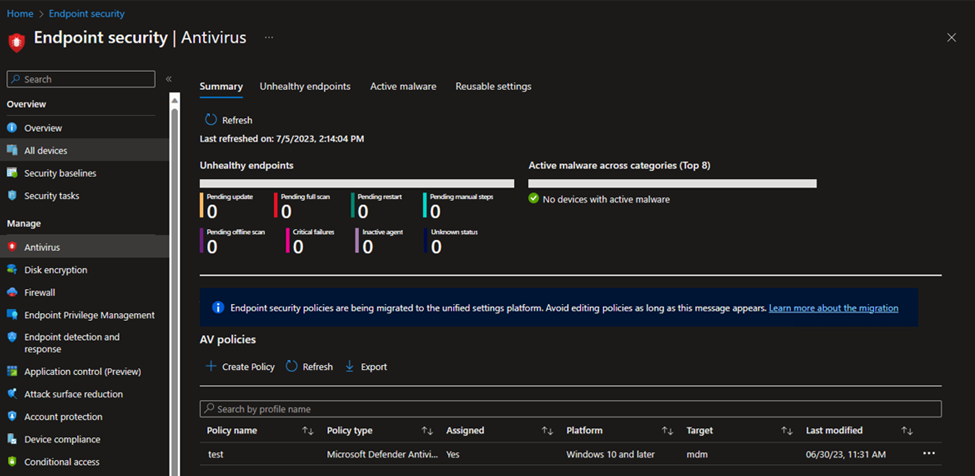
Endpoint Security
Enrollment
Enrollment Status Page (ESP)
Enterprise Mobility and Security (EMS)
Filters
Google
Google Mobile Services (GMS)
Google Play
Intune Company Portal
Intune for Education
iOS
Jamf
Just in Time (JIT)
Kiosk
Known Issue
macOS
Managed Home Screen
Microsoft 365
Microsoft Defender Antivirus
Microsoft Defender for Endpoint
Microsoft Edge
Microsoft Entra ID
Microsoft Graph Api
Microsoft HoloLens
Microsoft launcher
Microsoft Lists
Microsoft Outlook
Microsoft Surface
Microsoft Teams
Mobile Device Management (MDM)
Mobile Threat Defense (MTD)
Modern authentication
Network Access Control (NAC)
Network Device Enrollment Service (NDES)
OEMConfig
Office 365 APIs
Reporting
Role-based access control (RBAC)
Samsung
Scope tags
Security
Setup Assistant
Simple Certificate Enrollment Protocol (SCEP)
Support Tip
Troubleshooting
User guidance
Virtual Private Network (VPN)
Volume Purchase Program (VPP)
WIN32
Windows
Windows Autopilot
Windows Compliance
Windows Defender
Windows PowerShell
Zebra
- Home
- Microsoft Intune and Configuration Manager
- Intune Customer Success
Options
- Mark all as New
- Mark all as Read
- Pin this item to the top
- Subscribe
- Bookmark
- Subscribe to RSS Feed






















Latest Comments